Everything You Need to Know About Proxy Servers
From what a proxy server is to choosing the best type for your use case — 22 expert articles covering every aspect of proxy technology, privacy, and performance for Hong Kong users.
From what a proxy server is to choosing the best type for your use case — 22 expert articles covering every aspect of proxy technology, privacy, and performance for Hong Kong users.
A proxy server acts as an intermediary between your device and the wider internet. Instead of your browser connecting directly to a website, your request is first sent to the proxy, which then fetches the content on your behalf and returns it to you. The destination website only ever sees the proxy's IP address, not your own, providing a basic layer of anonymity and access control.
Proxy servers have been a foundational internet technology since the early days of the web. Originally deployed by organisations to cache frequently visited pages and reduce bandwidth consumption, they have evolved into sophisticated tools used for privacy protection, large-scale data collection, content filtering, and bypassing geographic restrictions. Today, the proxy market is a multi-billion dollar industry serving everyone from individual privacy-conscious users to enterprise-scale data operations.
In Hong Kong, proxy servers are widely used across both personal and corporate contexts. Businesses use them for competitive intelligence gathering, accessing global market data, and maintaining secure internal networks. Individuals use them to access geo-restricted content and protect their browsing activity from being monitored by ISPs and network administrators.

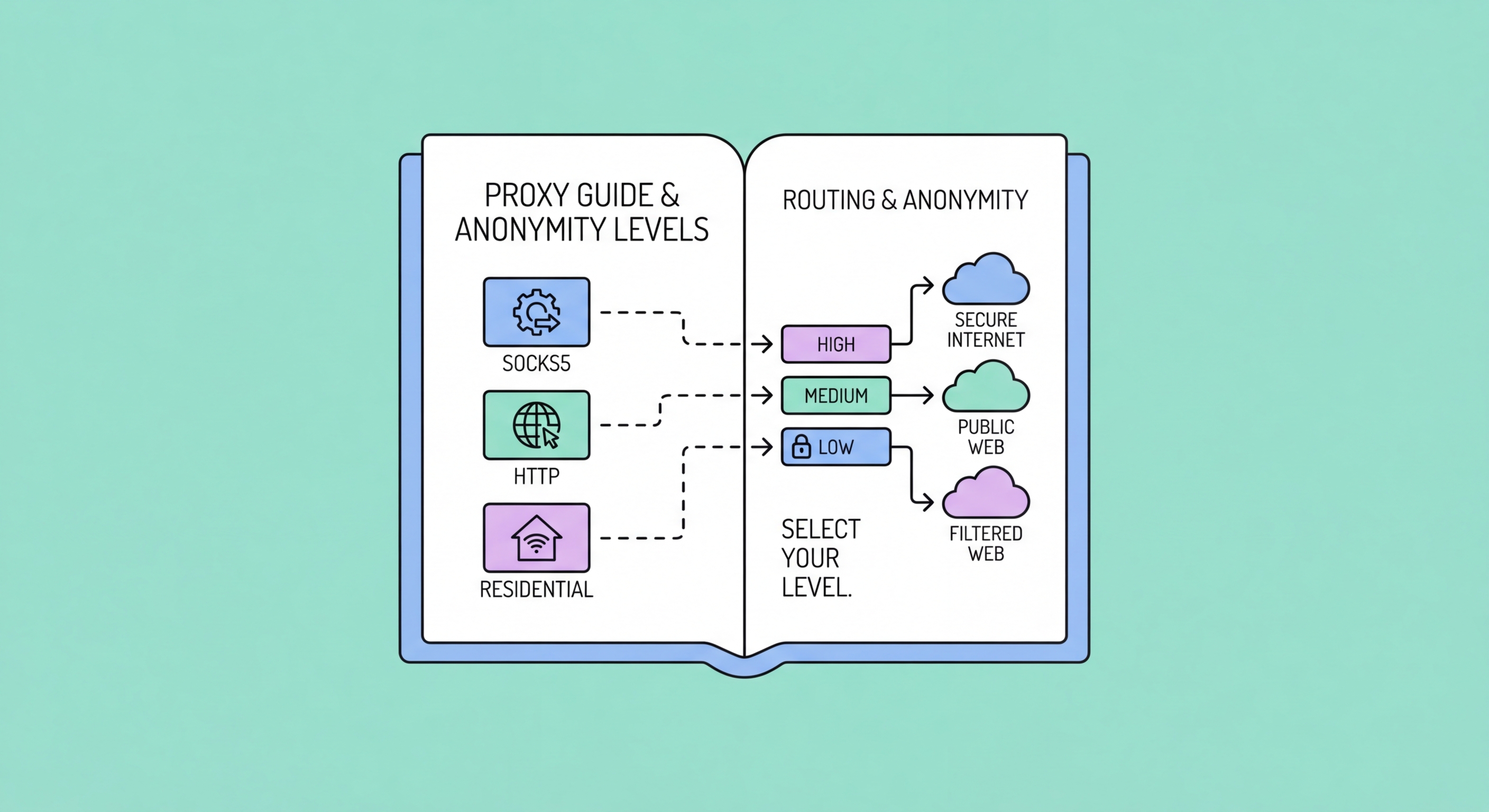
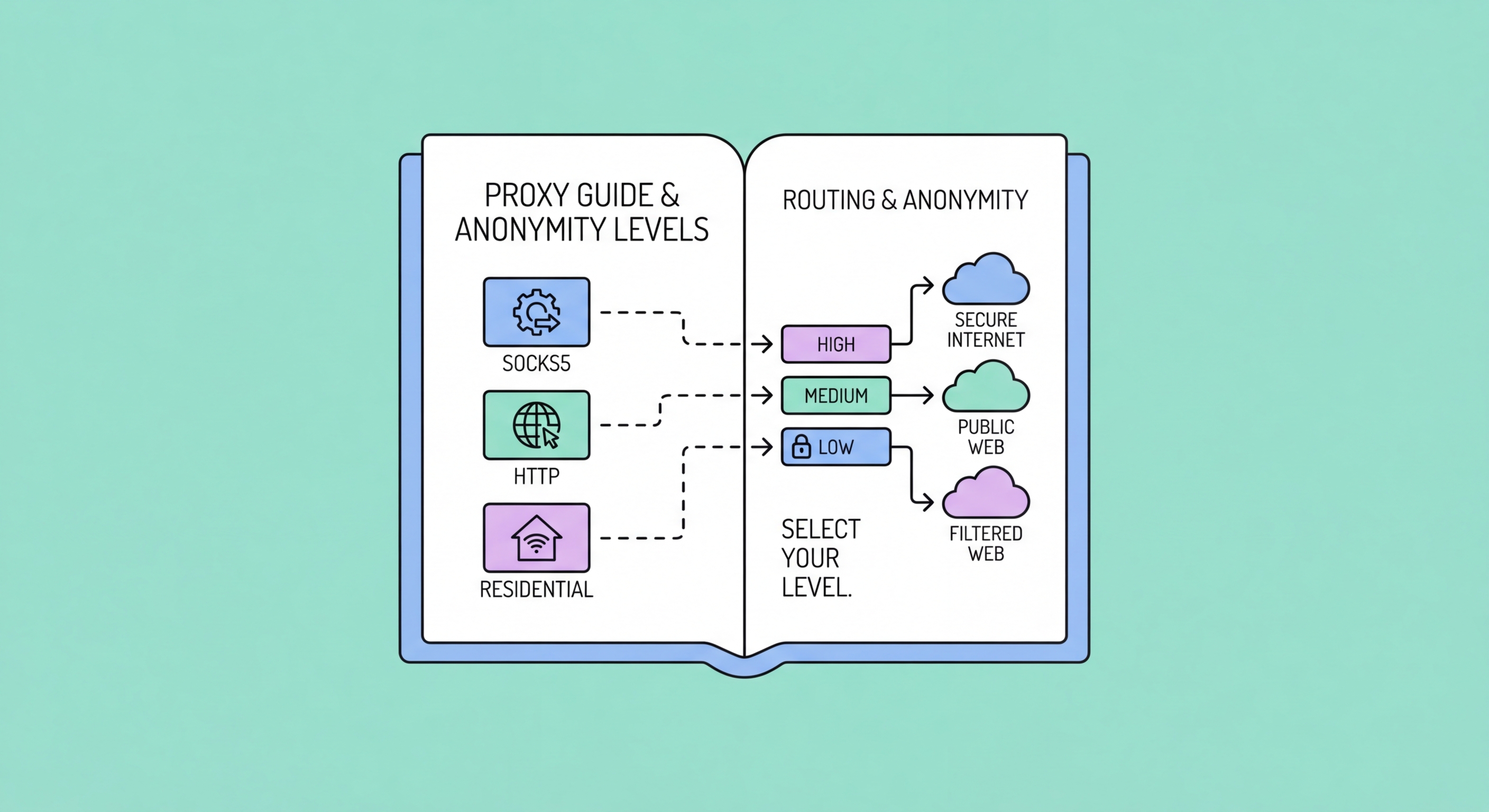
Not all proxies are created equal. The proxy landscape spans dozens of distinct types differentiated by their source of IP addresses, their level of anonymity, their supported protocols, and their intended use cases. Understanding these distinctions is essential to selecting the right proxy for your specific needs and avoiding the wrong tool for the job.
At the broadest level, proxies are categorised by IP source: datacenter proxies use IPs from commercial server farms and are fast and cheap but easily detectable; residential proxies use IPs assigned to real home internet connections and are harder to block; mobile proxies use IPs from mobile carriers and are the most difficult to detect of all. Each type occupies a different point on the cost-versus-undetectability curve.
Protocol is another key differentiator. HTTP proxies handle only web traffic, while HTTPS proxies add SSL/TLS support for encrypted connections. SOCKS proxies — particularly SOCKS5 — are protocol-agnostic and can handle any type of traffic including UDP, making them suitable for gaming, torrenting, and VoIP applications that HTTP proxies cannot support.

Proxies and VPNs are frequently confused because they both route your traffic through an intermediary server, masking your IP address in the process. However, they are fundamentally different technologies designed for different purposes. Understanding this distinction is critical — using the wrong tool can leave you with a false sense of security.
The core difference is encryption. A VPN encrypts all traffic from your device using protocols like WireGuard or OpenVPN, protecting everything you send and receive at the operating system level. A proxy, by contrast, typically offers no encryption — it merely forwards your traffic. An HTTPS proxy connection to an HTTPS website is encrypted end-to-end by TLS, but the proxy itself adds no additional encryption layer. This means your ISP can still see the volume and timing of your traffic, even if not its content.
Proxies have clear advantages where encryption is not the priority. They are generally faster than VPNs because there is no encryption overhead. They can be configured on a per-application or per-browser basis without affecting all device traffic. And for use cases like web scraping where you need to manage thousands of distinct IP addresses simultaneously, proxies are the only practical solution — no VPN service offers residential IP pools at that scale.

Hong Kong's position as Asia's leading financial and commercial hub creates unique and diverse proxy use cases. The city's businesses are among the most prolific users of commercial proxy services in the region, driven by the need to access global markets, conduct competitive intelligence, and manage international operations from a single hub location.
E-commerce businesses use proxies to monitor competitor pricing across regional markets without triggering rate limits or revealing their identity. Financial firms use them to gather real-time market data from global exchanges and news sources. Marketing agencies use them to verify that international advertising campaigns are displaying correctly in target markets, a practice known as ad verification that requires IPs genuinely located in specific countries and cities.
On the individual side, HK residents use proxies to access streaming platforms with different regional libraries, to protect their privacy when browsing on corporate or shared networks, and — for the technically inclined — to automate legitimate tasks like price comparison, flight tracking, and social media monitoring. Understanding the legal and ethical boundaries of proxy use is important for all users.
