Why Free Proxy Services Are Dangerous
Free proxy lists and web proxy services look appealing, but the hidden costs — data logging, credential theft, and malware injection — make them a serious security liability.
Free proxy lists and web proxy services look appealing, but the hidden costs — data logging, credential theft, and malware injection — make them a serious security liability.
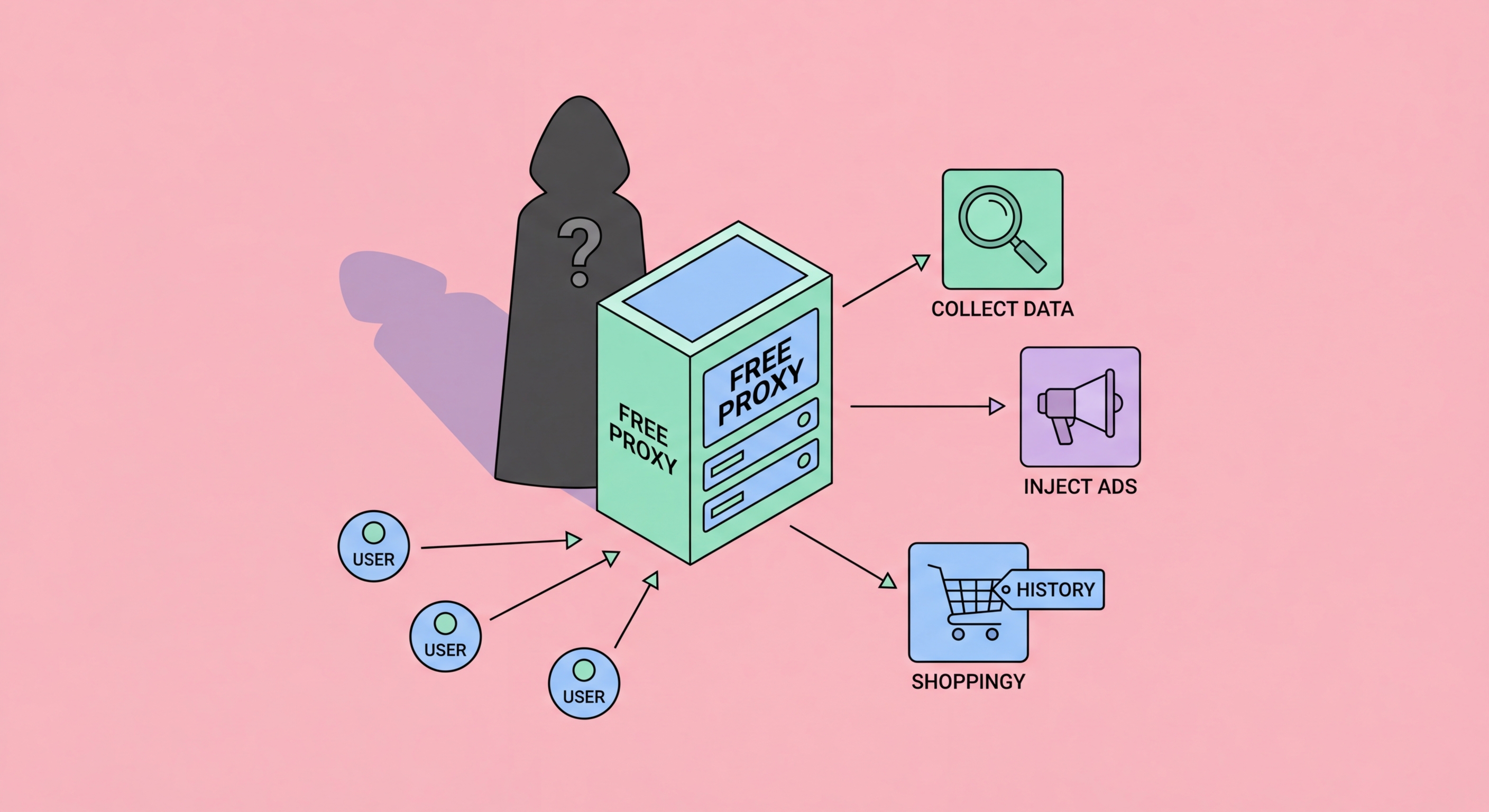
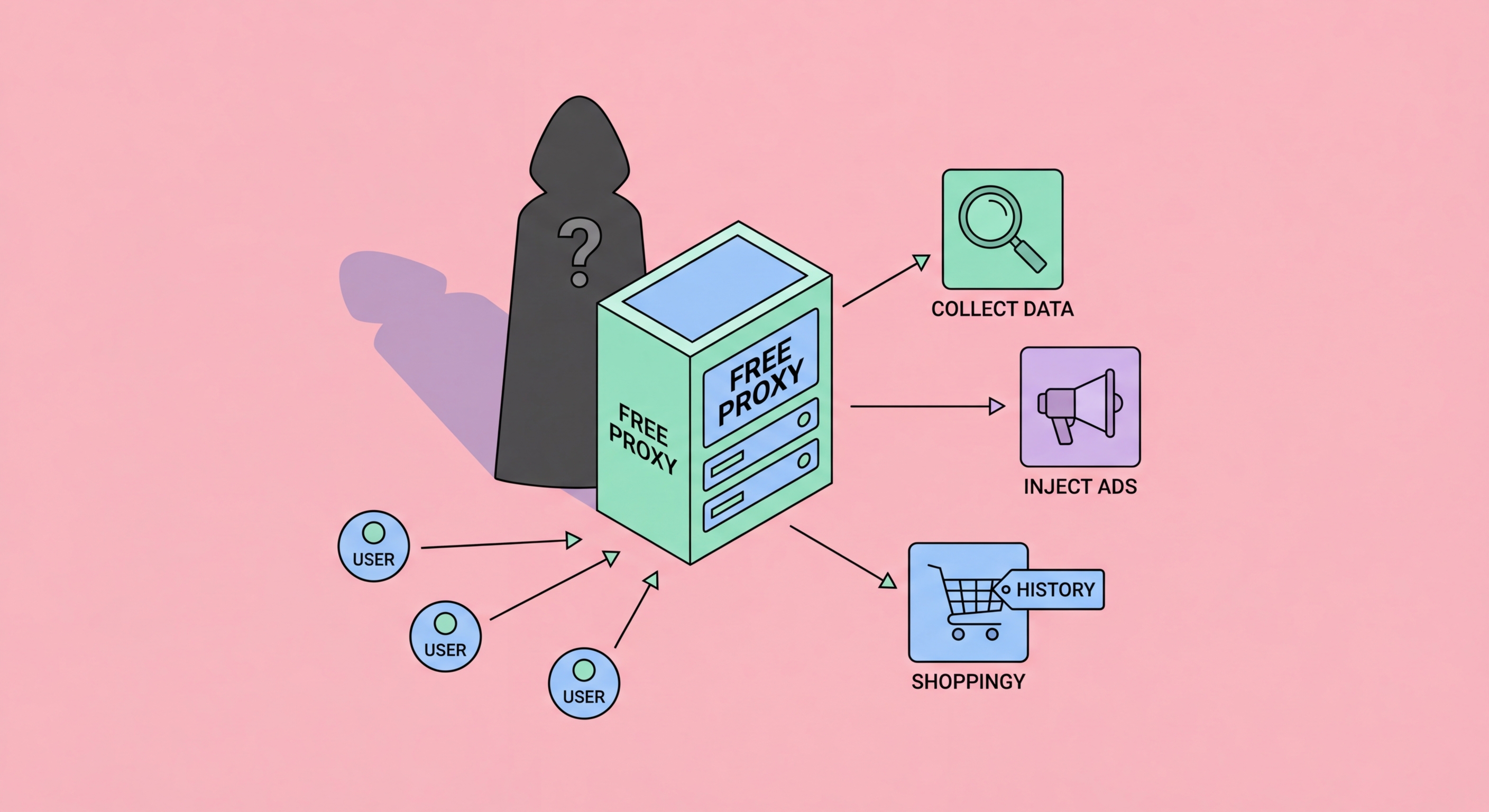
The fundamental problem with free proxy services is economic: operating a proxy network with sufficient bandwidth and server capacity to serve millions of users costs significant money. If users aren't paying with cash, they're paying with something else — and that something else is almost always their data. Free proxy operators sit in a perfect position as man-in-the-middle: every request you make, every website you visit, every form you submit passes through their infrastructure, giving them complete visibility into your browsing behavior.
Research by cybersecurity firms has consistently found that free proxy services engage in data harvesting at scale. A widely cited academic study examining hundreds of free proxy services found that a significant majority modified traffic in some way, with a large proportion injecting HTML or JavaScript into pages and some recording user credentials. The data collected is commercially valuable: browsing histories, login credentials, behavioral profiles, and device fingerprints can be sold to data brokers, used for targeted advertising, or — in the worst cases — used directly for identity theft and account takeover attacks.
Some free proxy operators are even more brazen in their monetisation strategy. They install tracking cookies and persistent browser identifiers in the traffic they proxy. They inject referral codes into shopping links, earning commissions on purchases you make while browsing through their proxy. They insert advertising into web pages, replacing the page's own ads with their own revenue-generating placements. Every one of these techniques involves interfering with your internet traffic in ways you have not consented to and may not notice during a normal browsing session.

Beyond data harvesting, some malicious free proxy operators inject malicious code directly into the web pages you view. Because the proxy sits between your browser and the destination server, it has the ability to modify any unencrypted HTTP response before delivering it to your browser. A malicious proxy can insert a JavaScript snippet into every page — this code runs in your browser with full access to the page's content, including forms, session cookies, and all user input.
Credential harvesting via injected JavaScript is a well-documented attack technique in this context. The injected script attaches event listeners to form fields and submits copies of everything you type — usernames, passwords, payment card numbers, one-time verification codes — to the proxy operator's servers before the form data reaches the legitimate destination. This attack is particularly dangerous because the legitimate website still receives your data and functions normally, giving no visual indication that your credentials have been stolen in transit.
HTTPS provides partial protection against content injection — a proxy cannot modify the content of an HTTPS response without breaking the TLS certificate chain, which triggers browser security warnings. However, this protection applies only to correctly implemented HTTPS sites. Sites serving mixed content remain vulnerable. Additionally, some free proxy tools — particularly browser extensions — request broad permissions that allow them to modify encrypted page content within the browser itself, defeating HTTPS protections from within the browser environment.

Even when a free proxy operator has benign intentions, the performance of free proxy services is consistently poor. Free proxies are typically overloaded with thousands of simultaneous users sharing limited bandwidth on under-resourced servers. Unlike paid services that invest in infrastructure capacity proportionate to their user base, free proxy operators have no financial incentive to upgrade bandwidth when demand exceeds capacity — users who complain are simply replaced by new users who find the list on the same public directories.
Many IP addresses listed on free proxy aggregator sites are not intentionally operated proxy services at all. They are compromised devices — poorly secured home routers, corporate servers with misconfigured firewall rules, or malware-infected computers — running open proxy software without their owners' knowledge. These unintentional proxies may disappear at any moment when the device is patched, rebooted, or when the ISP detects the anomaly and terminates the connection, making them entirely unsuitable for any task requiring consistent availability.
Free proxy IPs are also rapidly identified and blocked by websites. Because the same IP addresses are used by thousands of users making requests in automated-looking patterns, website anti-bot systems flag and block them quickly. A free proxy that appears to work today may be blocked by your target website within hours. Commercial proxy providers continuously refresh their IP pools and have direct relationships with networks to maintain access — a capability free services fundamentally cannot replicate.

The good news is that trustworthy alternatives to free proxies are accessible and affordable. For individual users wanting basic geo-access and browser-level privacy, a quality paid VPN subscription starts at roughly HK$30–50 per month and provides encrypted, reliable protection. Unlike free proxies, reputable VPN providers have audited no-logs policies, transparent privacy practices, and business models funded by user subscriptions rather than data harvesting.
For users who specifically need proxy functionality — per-browser routing, SOCKS5 support for specific applications, or geographic testing — low-cost paid proxy services from established providers are available. Providers like IPRoyal, Proxy-Cheap, and Webshare offer datacenter proxies starting at just a few US dollars per month for limited but legitimate usage. The cost is minimal compared to the security risk of free alternatives, and these services maintain proper infrastructure with reliable uptime and customer support.
For businesses with professional data collection needs, investing in a commercial residential proxy service from providers like Bright Data, Oxylabs, or Smartproxy is the appropriate solution. These providers operate with proper consent frameworks for their IP contributors, offer robust APIs, comprehensive documentation, and technical support, and maintain compliance with data protection regulations. The cost per gigabyte is fully justified by the reliability, legality, and performance that free alternatives simply cannot provide at any scale.
