What Is the Dark Web? A Complete Explainer
A clear, factual explanation of what the dark web is, how it works technically, what's actually found there, and what Hong Kong residents genuinely need to know about it.
A clear, factual explanation of what the dark web is, how it works technically, what's actually found there, and what Hong Kong residents genuinely need to know about it.
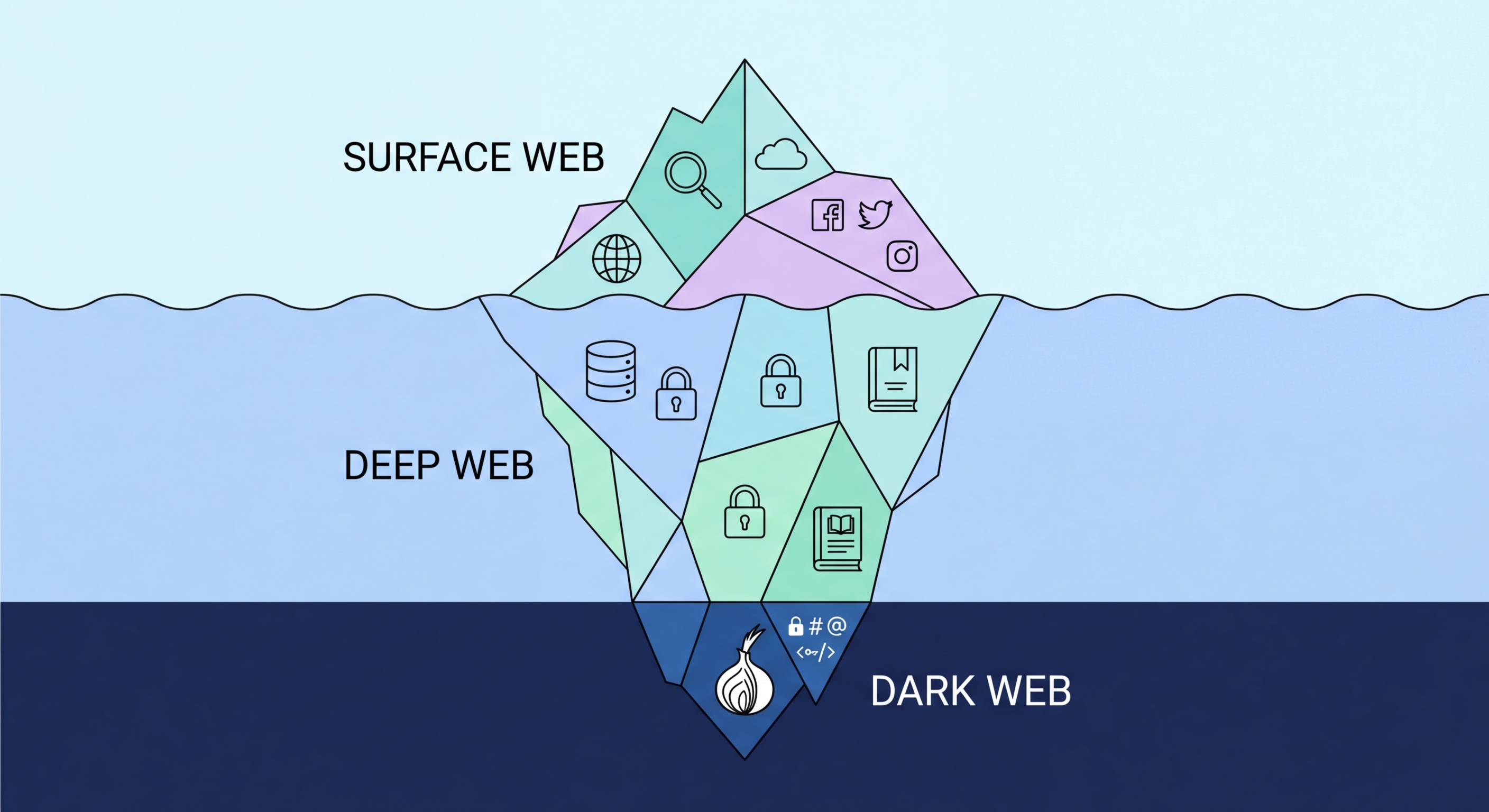
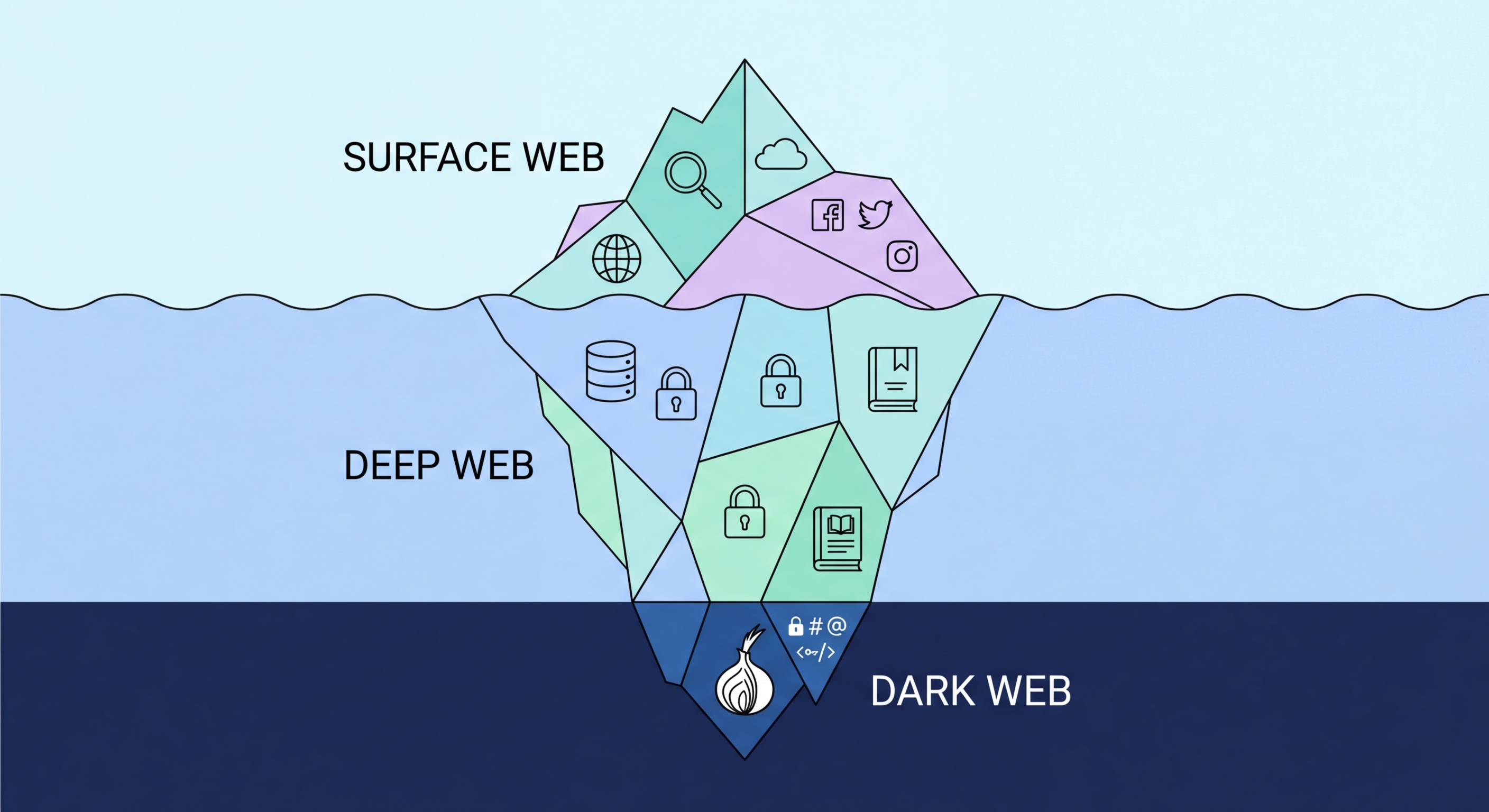
The internet can be divided into three layers. The surface web is what most people use daily — websites indexed by Google, Bing, and other search engines, accessible through a standard browser. The deep web is everything not indexed by search engines: online banking portals, private email, corporate intranets, academic databases behind paywalls, medical records systems, and any web content that requires authentication to access. The deep web is far larger than the surface web and is entirely normal and legal — your online banking session is technically "deep web." The to Check If Your Data Is on the Dark Web">dark web is a small subset of the deep web that requires specialised software and is specifically designed for anonymity.
The Data Breach? From Hack to Dark Web">dark web operates primarily through the Tor network (The Onion Router). Tor routes internet traffic through a series of three volunteer-operated relay nodes, encrypting the traffic at each relay. Each relay knows only the previous and next relay in the chain — not the origin and destination simultaneously. This layered encryption model (hence "onion") makes it very difficult to trace internet activity back to its source. Websites on the Tor network use .onion addresses — cryptographically generated domain names that are not registered through standard DNS and are only accessible through the Tor Browser or a Tor-compatible proxy.
The Tor network was originally developed by the US Naval Research Laboratory in the mid-1990s for secure government communications. It was later made open source and is now maintained by the non-profit Tor Project. This origin explains why the dark web is not inherently criminal — it was designed to protect legitimate privacy. Today, Tor is used by journalists communicating with confidential sources, human rights workers in repressive countries, corporate whistleblowers, security researchers, privacy advocates, and people in countries where internet access is heavily censored or monitored. However, it has also attracted criminal use precisely because of the anonymity it provides.

Media coverage of the dark web tends to focus exclusively on its most sensational criminal elements. The reality is more nuanced. Research consistently shows that a substantial portion of dark web traffic and sites are legitimate: SecureDrop installations used by major news organisations (The Guardian, Washington Post, BBC) for secure whistleblower communication; Tor-accessible versions of legitimate websites (Facebook, BBC, The New York Times all maintain .onion addresses); academic resources and privacy tools; and forums for security researchers and privacy advocates.
The criminal dark web does exist and is significant. The most relevant category for Hong Kong residents is the stolen data economy: marketplaces and forums where breach databases are sold and traded. These include credential databases (email/password combinations from major breaches), financial data (credit card numbers, CVV codes, banking credentials), personal identity data (name, address, HKID, passport), and corporate data (employee credentials, proprietary documents). Other significant criminal markets include drug trafficking, counterfeit currency and documents, and cybercrime-as-a-service offerings (malware, phishing kits, DDOS services).
Understanding what is specifically relevant to Hong Kong residents: the most directly harmful dark web content for HK users is the breach data economy, which directly threatens financial security and identity. The other criminal categories — drug markets, weapons, etc. — are relevant primarily as awareness context, not as direct threats to the average HK internet user. The practical implication is that dark web monitoring — specifically monitoring for your personal data in breach databases — is the most actionable defensive measure for the vast majority of HK residents.

Hong Kong's data environment creates specific dark web risks. The city's highly connected population uses numerous digital services — banking, e-commerce, government portals, health platforms, and loyalty programmes — each of which holds personal data that is a target for breaches. Major breaches affecting HK-registered users in recent years have included international platforms (Facebook, LinkedIn, Adobe), HK-specific e-commerce and retail services, and government-adjacent systems. Each breach that includes HK user data represents a potential contribution to the dark web's supply of HK personal data.
The Cantonese-speaking cybercriminal ecosystem maintains its own dark web forums and channels — distinct from the predominantly English-language major markets — where HK-specific breach data, identity documents, and locally relevant fraud tools are traded. This community has specific value for HK-targeted credential stuffing against HK banking and fintech apps, local identity fraud using HKID data, and targeted social engineering using combinations of personal data from local breaches. The HKPF's CSTCB has documented increasing sophistication in locally targeted cybercrime operations.
The practical implication for Hong Kong residents is that your risk of dark web data exposure is not limited to large international breaches. Local services, smaller e-commerce platforms, and businesses that may have weaker cybersecurity posture than major corporations have been targets. Anyone who has used Hong Kong e-commerce sites, local services, loyalty programmes, or digital platforms should actively monitor for their data on breach databases. The combination of HIBP monitoring, password manager breach alerts, and periodic manual checks covers the most important bases for most HK users.

You cannot prevent your data from being included in a breach at an organisation that holds it — that's outside your control. What you can control is: how much data you share, with whom; how unique and strong your passwords are; whether 2FA protects your accounts; and how quickly you respond when breach notifications arrive. These measures don't prevent dark web exposure but dramatically limit the damage that can result from it.
The most impactful defensive measures against dark web-based threats are: unique passwords for every account (so a breach of one service doesn't compromise others); dark web monitoring alerts set up for all your email addresses; authenticator app 2FA enabled on banking, email, and cloud storage accounts; and being prepared to act quickly when an alert arrives — changing passwords and contacting institutions the same day as a breach notification, not weeks later.
For proactive monitoring, HIBP's free email alerts, combined with built-in password manager breach detection (iOS Passwords app, 1Password Watchtower, Google Password Manager's breach alert) cover the most important monitoring bases at no cost. This baseline monitoring, practiced consistently, provides early warning for the majority of credential-based threats that Hong Kong residents face from dark web data exposure.
