Tor vs Proxy vs VPN: Which Is Right for You?
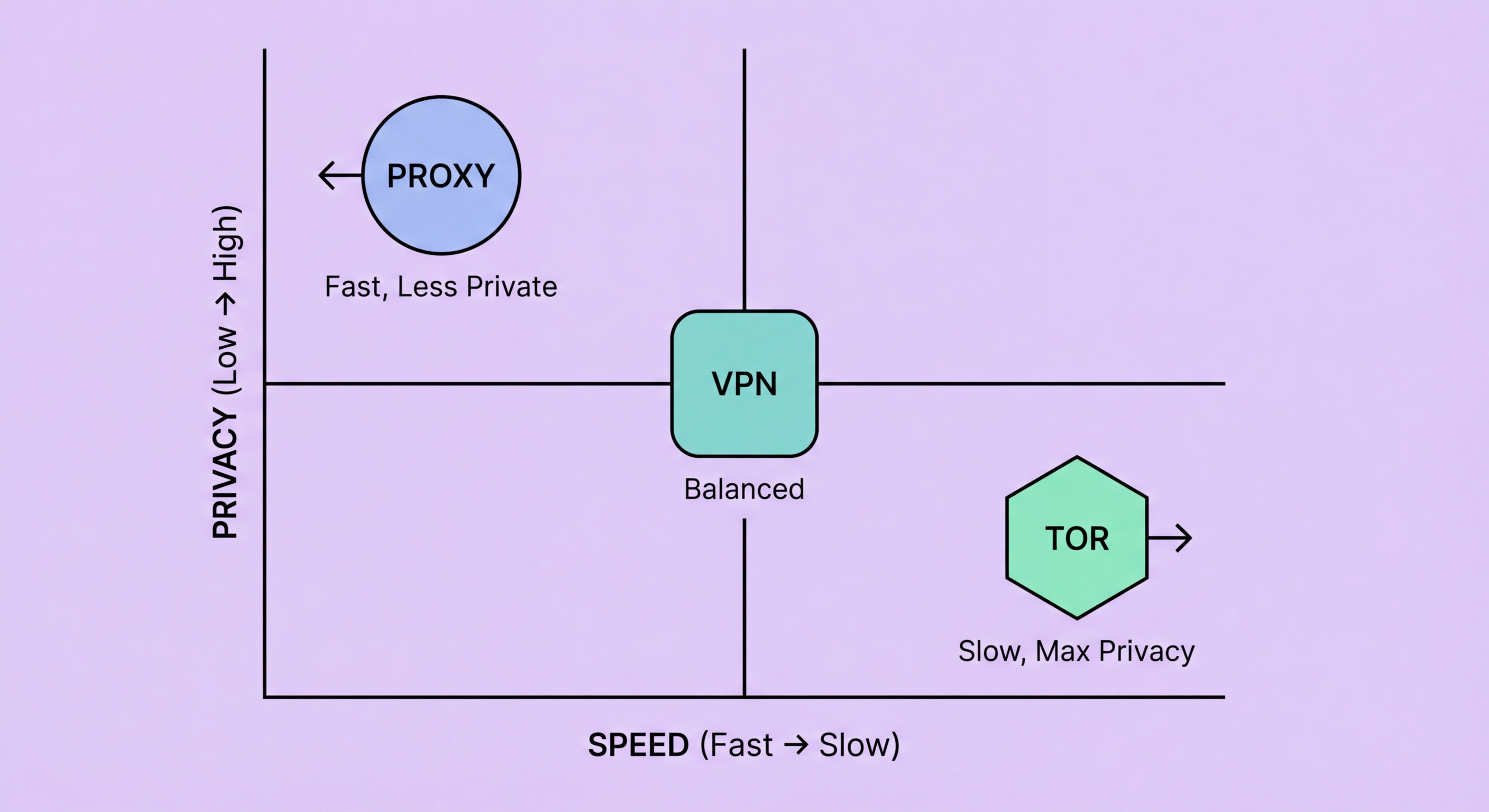
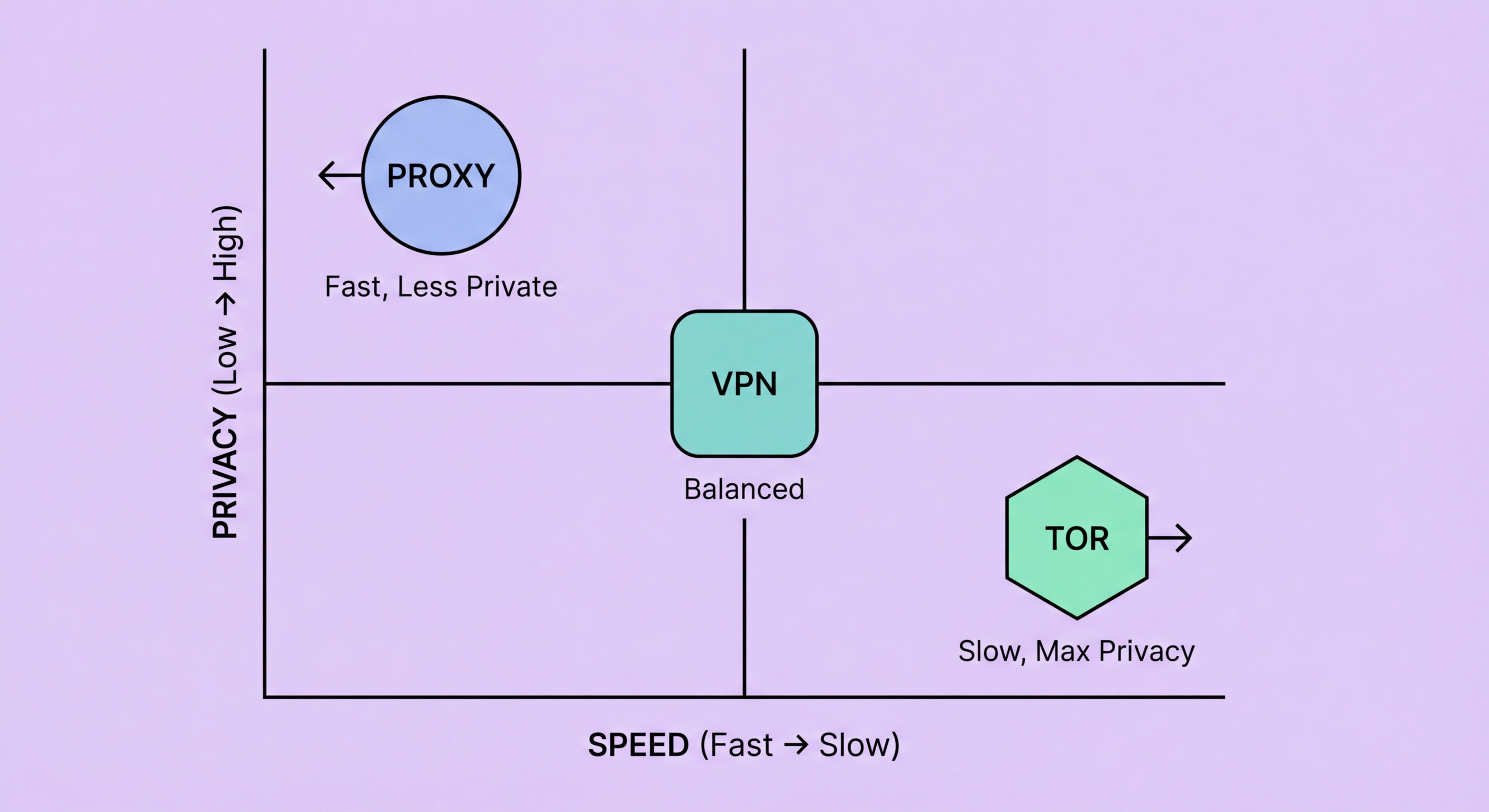
Three technologies that all route your traffic through intermediary servers — but with fundamentally different architectures, anonymity properties, speeds, and use cases. Here's the complete comparison.
Three technologies that all route your traffic through intermediary servers — but with fundamentally different architectures, anonymity properties, speeds, and use cases. Here's the complete comparison.
A proxy server routes your traffic through a single intermediary server. Your browser connects to the proxy, the proxy connects to the destination on your behalf, and the destination sees the proxy's IP. There is typically one point of trust (and failure): the proxy provider knows who you are (your client IP) and what you're doing (your request history). The destination knows nothing about your real identity unless the proxy reveals it via headers. This single-hop model is fast and simple but provides limited protection against an adversary who can observe traffic at the proxy or compel the proxy provider to disclose data.
A VPN also routes traffic through a single server, but adds a critical layer: end-to-end encryption between your device and the VPN server. All traffic from your device is encrypted in the VPN tunnel before leaving your machine, so your ISP, network administrator, and anyone monitoring the local network sees only encrypted data destined for the VPN server. At the VPN server, traffic is decrypted and forwarded to the destination. Like a proxy, the VPN provider is a single point of trust — they know your real IP and your traffic. However, the encryption provides strong protection against passive surveillance by network-level observers between you and the VPN server.
Tor (The Onion Router) uses a fundamentally different architecture: onion routing through a circuit of three volunteer-operated relay nodes. Each layer of encryption is peeled away at each hop like layers of an onion. The entry node (guard) knows your real IP but not the destination. The middle node knows neither your IP nor the destination. The exit node knows the destination but not your real IP. No single node has complete information about both the sender and the destination. This separation of knowledge provides dramatically stronger anonymity than single-hop architectures, at the cost of significant performance reduction due to the multi-hop routing and volunteer infrastructure limitations.

Tor provides the strongest anonymity of the three technologies for most threat models. Its multi-hop architecture means that even if one relay is compromised or monitored, the adversary gains incomplete information — either your real IP (from the entry node) or the destination (from the exit node) but not both simultaneously. This property makes Tor genuinely resistant to traffic correlation attacks by single-entity adversaries. Intelligence agencies with the ability to monitor a large fraction of Tor relays globally have demonstrated some capability to deanonymise Tor users through traffic correlation, but Tor remains the strongest available tool for ordinary users facing adversaries who can't perform global traffic analysis.
A no-logs VPN from a reputable provider in a privacy-friendly jurisdiction provides strong practical anonymity for everyday use cases. The VPN provider is the single point of trust — if they truly maintain no logs and cannot be compelled to identify you, then your anonymity is protected. The risk is that VPN provider claims are difficult to verify definitively. Independent audits of provider infrastructure and past cases where providers have (or haven't) complied with law enforcement requests provide evidence of trustworthiness, but not guarantees. VPNs protect effectively against ISP surveillance, corporate network monitoring, and passive traffic interception — the threat models most relevant to typical Hong Kong internet users.
Proxies provide the weakest anonymity of the three. They typically don't encrypt traffic, meaning both the proxy provider and network observers have full visibility. Even elite proxies that remove all IP-identifying headers still require trust in the proxy operator. Free proxies actively monetise the user data they collect. Paid proxy services from reputable providers offer reasonable protection against destination-server-level tracking, but they're not appropriate for high-stakes anonymity requirements. Proxies are more accurately tools for IP substitution and access control than tools for anonymity in a meaningful privacy sense.

Speed is where proxies have a clear advantage. A datacenter proxy server adds minimal latency (2–10ms) and has essentially no throughput impact since there's no encryption processing. For bandwidth-intensive applications — high-speed data collection, large file transfers, 4K video streaming — proxies impose the least performance penalty of the three options. The faster performance makes proxies practical for applications where high volume and low latency matter more than anonymity.
VPNs with modern protocols like WireGuard add modest latency (10–30ms on well-connected servers) and reduce throughput by 5–15% due to encryption overhead. This performance impact is imperceptible for most everyday activities — browsing, streaming video, video calls, and messaging apps work seamlessly through a quality VPN with negligible noticeable degradation. The performance improvement of WireGuard over older protocols like OpenVPN has largely closed the practical speed gap between VPN and no-VPN browsing for users on high-speed connections.
Tor is significantly slower — typically 5–10x slower than a direct connection, with page load times measured in seconds rather than milliseconds for complex modern websites with many embedded resources. The multi-hop architecture, volunteer-operated relay bandwidth limitations, and onion encryption layers all contribute to this performance overhead. Tor is entirely practical for text-based browsing, whistleblowing platform submissions, and privacy-critical communications — but it's inappropriate for high-bandwidth activities like streaming video, gaming, or large-scale data collection. Tor Browser is the only recommended way to use Tor for general browsing — it includes anti-fingerprinting protections that standard browsers using Tor don't provide.

The choice between Tor, VPN, and proxy should be driven entirely by your threat model — the specific risks you're protecting against and the adversary you're protecting against. for Hong Kong SMEs: Where to Start">For Hong Kong users facing everyday privacy concerns — ISP data collection, corporate WiFi monitoring, tracking by advertising networks, and basic geographic access needs — a quality no-logs VPN is the right choice. It provides comprehensive device-level protection with minimal usability impact, is easy to use, and protects against all the threats that most users actually face in daily life.
For journalists, activists, human rights workers, or anyone whose anonymity must withstand sophisticated technical investigation, Tor (or a combination of Tor over VPN for additional entry node protection) is the appropriate choice. The performance limitations are the price of stronger anonymity, and this trade-off is appropriate for high-risk contexts. Tor Browser includes browser fingerprint normalisation that neither proxies nor VPNs provide — a critical protection for users facing well-resourced adversaries who use cross-session correlation to deanonymise users over time.
Proxies are the right choice when your requirement is scalable IP substitution rather than anonymity — web scraping, automated data collection, geographic access testing, and application-specific routing. They're also appropriate for personal use cases where you need browser-level geographic access without affecting other device traffic. The key is being clear about what you're protecting against: proxies provide IP concealment at the destination level, not protection against network surveillance or a determined adversary with access to the proxy provider's data.
