1How It Works
How an Evil Twin Attack Is Set Up and Executed
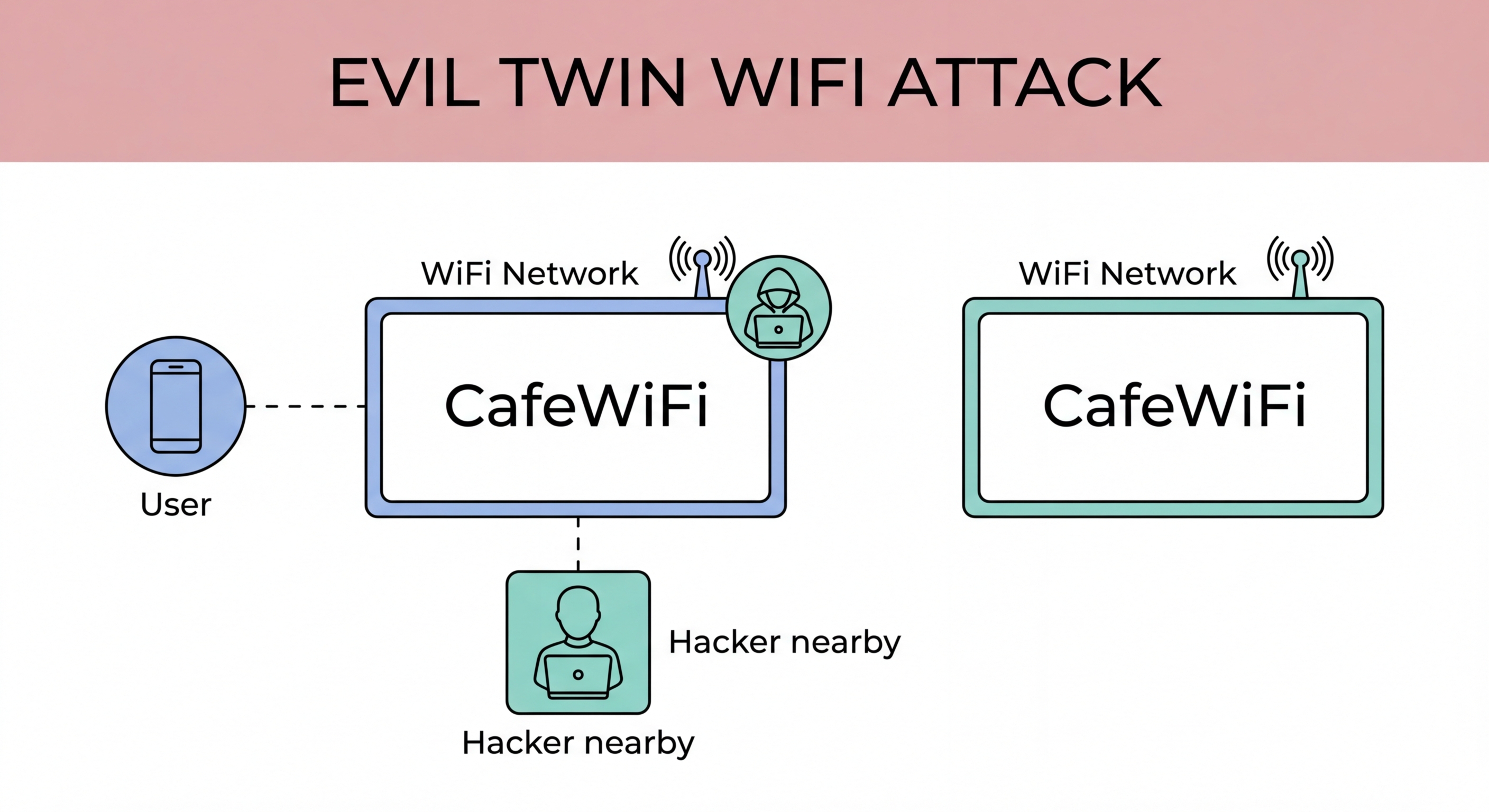
An evil twin attack requires the attacker to create a WiFi access point broadcasting the same SSID (network name) as a legitimate network. The attacker does thHong Kong?">is using a laptop with a WiFi adapter set to access point mode, or a purpose-built device like a WiFi Pineapple — a commercially available penetration testing device that automates evil twin attacks. The attacker connects to the internet via a separate connection (wired, cellular, or a second WiFi network) and routes all victim traffic through their device, providing internet access while capturing everything in transit.
The success of an evil twin attack depends on signal strength. When multiple access points broadcast the same SSID, a device will typically connect to the one with the strongest signal. In a busy MTR station, a hotel lobby, or an airport terminal, an attacker with a high-gain antenna can often overpower the legitimate network's signal, causing nearby devices to connect to the evil twin instead. Devices that have previously connected to that SSID — who have it saved in their "remembered networks" list — may connect automatically without any user action, as soon as they detect the familiar network name in range.
Once a victim connects to the evil twin, the attacker controls their entire internet connection. They can serve a convincing captive portal login page identical to the hotel's or coffee shop's real portal, collecting whatever credentials or personal information users submit. They can perform SSL stripping to defeat HTTPS protection and read all unencrypted or downgraded traffic. They can inject malicious scripts into HTTP websites to steal cookies from authenticated sessions. The attack is completely transparent to the victim — internet access works normally, and there is no visible indication that traffic is being intercepted.
- Setup: Laptop or WiFi Pineapple creates AP with identical SSID to legitimate network
- Signal strength: Higher-power attacker antenna outcompetes legitimate network signal
- Auto-connect risk: Saved networks connect automatically to strongest matching SSID
- Captive portal cloning: Fake login portal collects user credentials and registration data
- Full traffic control: All victim traffic flows through attacker's device
- No visible signs: Internet works normally — victim sees no indication of attack
See how MITM attacks are executed once the evil twin connection is made →