3Risk Locations in Hong Kong
Where Juice Jacking Is Most Likely in Hong Kong
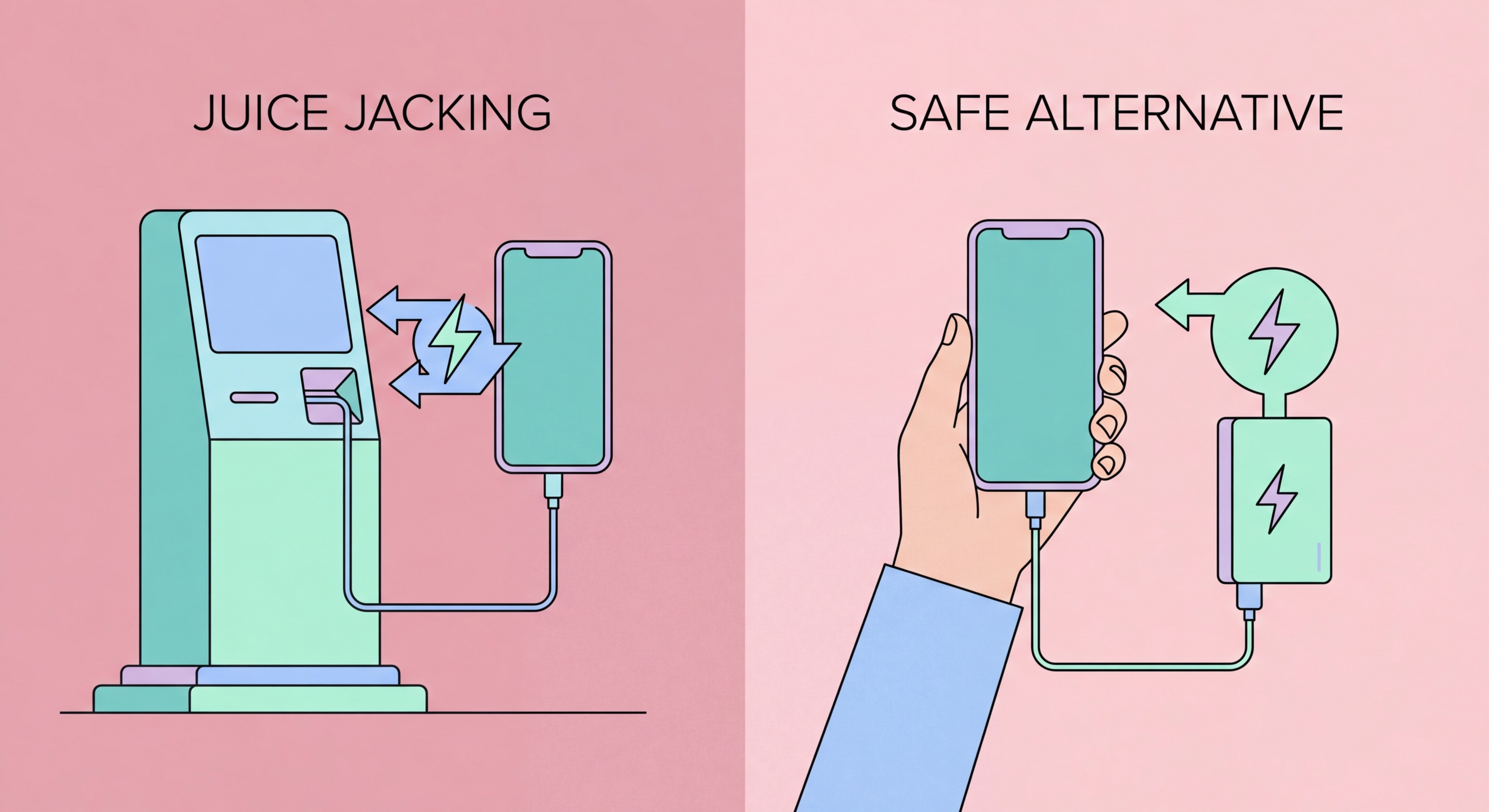
While no location is definitively confirmed to have active juice jacking stations in to Do If Your Phone Is Lost or Stolen in Hong Kong">Hong Kong, the environments that present the highest risk — based on attack feasibility, victim volume, and documented attack patterns globally — are international transit points, major shopping malls, and tourist areas. Hong Kong International Airport handles tens of millions of passengers annually and has numerous public USB charging stations in departure lounges, terminal connectors, and transit zones. Travellers are frequently low-battery and under time pressure, making them less likely to question public charging options.
MTR station charging facilities, available at various stations, are another environment to be cautious about. The MTR system handles approximately five million journeys per day, giving any compromised station extraordinary exposure to potential victims. While the MTR Corporation maintains its infrastructure, any publicly accessible USB port — whether installed by the venue or added unofficially — represents a potential attack surface. The same applies to charging stations in libraries, community centres, and government facilities that are accessible to the general public.
Hotel rooms present a subtler risk. Many modern hotel rooms include USB charging ports built into the bedside lamp, desk lamp, or power strip. These ports are part of the hotel's installed infrastructure and could theoretically be modified by someone with access to the room's electrical systems. Business travellers who frequently stay in different hotels and charge overnight should be particularly aware of this risk. The safest habit is to always use the standard wall power outlet with your own charger, or carry a power bank as the primary charging method.
- HKIA and cruise terminals: High passenger volume, multiple public USB charging stations in departure and arrival areas — highest risk of targeted installations.
- MTR charging stations: Millions of daily commuters using transit-area charging infrastructure make MTR stations attractive targets for juice jacking.
- Major shopping malls: Times Square, IFC Mall, Pacific Place, and Harbour City all have public charging areas that could be targeted in a high-traffic attack.
- Hotel USB ports: Built-in bedside USB ports in hotel rooms may be compromised — use wall power outlets and your own charger when possible.
- Co-working spaces: Public co-working spaces and business centres with communal USB ports are also medium-risk environments.
- Rental power banks: Third-party power bank rental services (common in mainland China) represent a specific risk — a rented power bank could contain offensive hardware.
Protect all your mobile connections with a VPN →