1How It Works
How a SIM Swap Attack Is Executed
A SIM swap attack begins with reconnaissance. Before contacting your mobile carrier, the attacker gathers personal information about you — date of birth, home address, HKID number if obtainable, account holder name, the last four digits of your credit card (sometimes visible in data breaches), and any account PINs or passwords associated with your carrier account. This information is collected from social media profiles, purchased data breach databases, phishing emails you may have responded to, or through preliminary phone calls to low-level carrier staff.
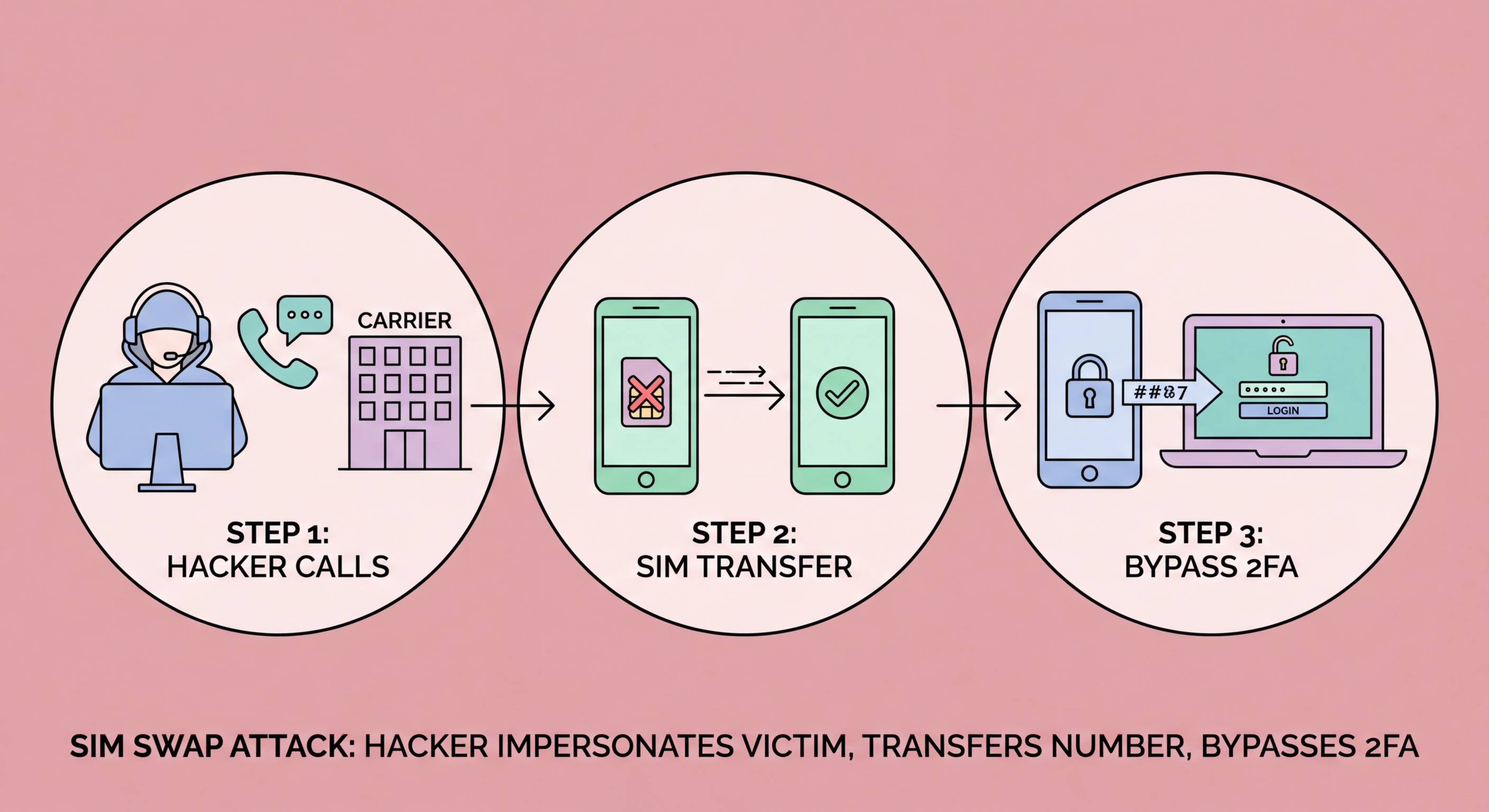
With sufficient personal information, the attacker contacts your carrier's customer service — by phone, online chat, or in person at a store — and claims to be you. They say they have a new SIM card and need to Transfer Your Authenticator App to a New Phone">to transfer your number to it, or claim their phone was lost or damaged and they need a replacement SIM. The customer service representative, following standard procedures, asks verification questions. The attacker provides the answers gathered during reconnaissance. If the representative accepts the verification, the number is transferred to the attacker's SIM within minutes.
The moment the transfer completes, your phone loses signal — all calls and texts now route to the attacker's device. The attacker immediately begins working through your accounts, starting with your email (by requesting a password reset to your now-controlled phone number). With email access, they reset passwords on banking apps, social media, crypto exchanges, and any other service linked to that email. The window between SIM transfer and account compromise can be as short as 10–15 minutes. You may not even notice your phone has lost signal until it is too late.
- Phase 1 — Reconnaissance: Gathering birthdate, address, ID numbers, and carrier account details
- Phase 2 — Social engineering: Calling or visiting carrier claiming to be account holder
- Phase 3 — Transfer: Convincing representative to move number to attacker's SIM
- Phase 4 — Account takeover: Using SMS codes to reset email, then cascading to all linked accounts
- Speed: Entire attack can complete in 15–30 minutes after successful SIM transfer
- Your signal: Your phone drops to "No Signal" when the transfer completes — the first warning sign
See why SIM swap is just one of several SMS 2FA weaknesses →