4Provider Selection
Selecting a Business Proxy Provider for Hong Kong Operations
Business proxy procurement differs from individual consumer proxy selection in several important ways. Enterprise buyers should evaluate providers on service level agreements, data compliance certifications, API completeness, technical support quality, and financial stability — not just price and pool size. A proxy provider that becomes unavailable due to business failure or infrastructure problems can disrupt mission-critical data operations with significant business impact. Stick to established providers with multi-year track records, clear ownership structures, and responsive enterprise support channels.
Data compliance is increasingly important for Hong Kong businesses, particularly those in regulated sectors. The Personal Data (Privacy) Ordinance places obligations on organisations regarding how they collect and handle personal data. When using proxies to collect public web data, ensure your operations comply with applicable data protection regulations in both Hong Kong and the jurisdictions of the websites being scraped. Premium providers like Bright Data include legal compliance guidance and Terms of Service auditing in their enterprise packages — a significant advantage for regulated industries.
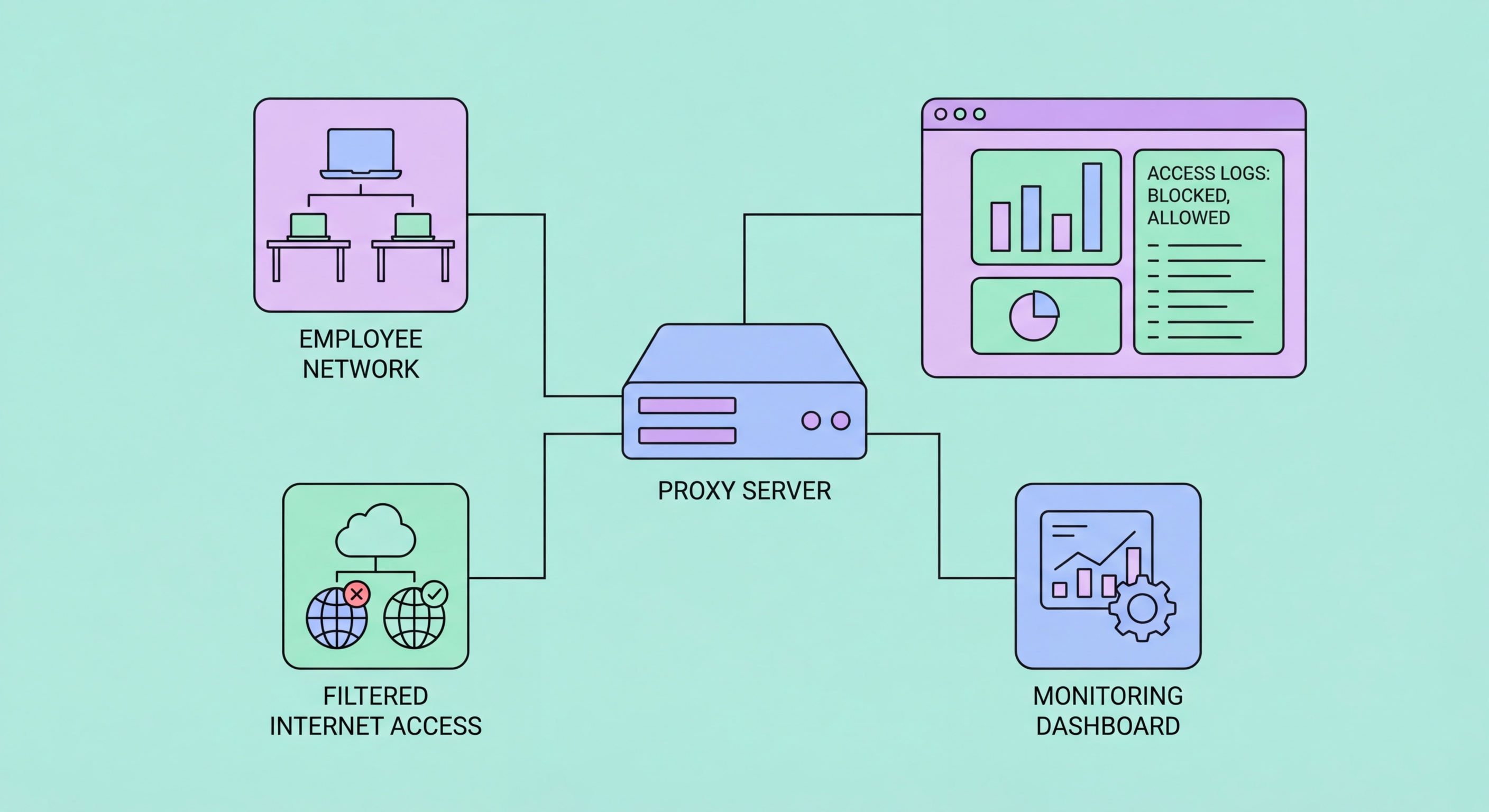
For corporate security proxy deployments (rather than data collection proxies), the evaluation criteria are different: integration with existing security infrastructure (SIEM, SOAM, endpoint security platforms), SSL inspection capabilities, threat intelligence feed integration, compliance reporting features, and support for the user directory (Active Directory, Azure AD, Okta) are the primary requirements. Enterprise security proxy vendors including Zscaler, Netskope, Cisco Secure Web Gateway (formerly Umbrella), and Palo Alto Networks Prisma Access are the leading options in this category, with local presence or partners in Hong Kong.
- SLA Requirements: Enterprise operations need uptime guarantees, support response times, and escalation paths.
- Data Compliance: Verify provider data handling practices comply with PDPO and applicable international regulations.
- API Completeness: Production data operations require full-featured APIs for rotation, geo-targeting, and session management.
- Security Proxy Vendors: Zscaler, Netskope, and Cisco Umbrella for corporate security proxy with HK presence/partners.
- Data Collection Leaders: Bright Data, Oxylabs, and Smartproxy for enterprise-scale business data collection needs.
- Volume Pricing: Negotiate enterprise pricing — list prices for residential proxies are negotiable at business scale.
Compare the best proxy providers for business →