3Rogue Networks
Evil Twin Attacks and Rogue Access Points
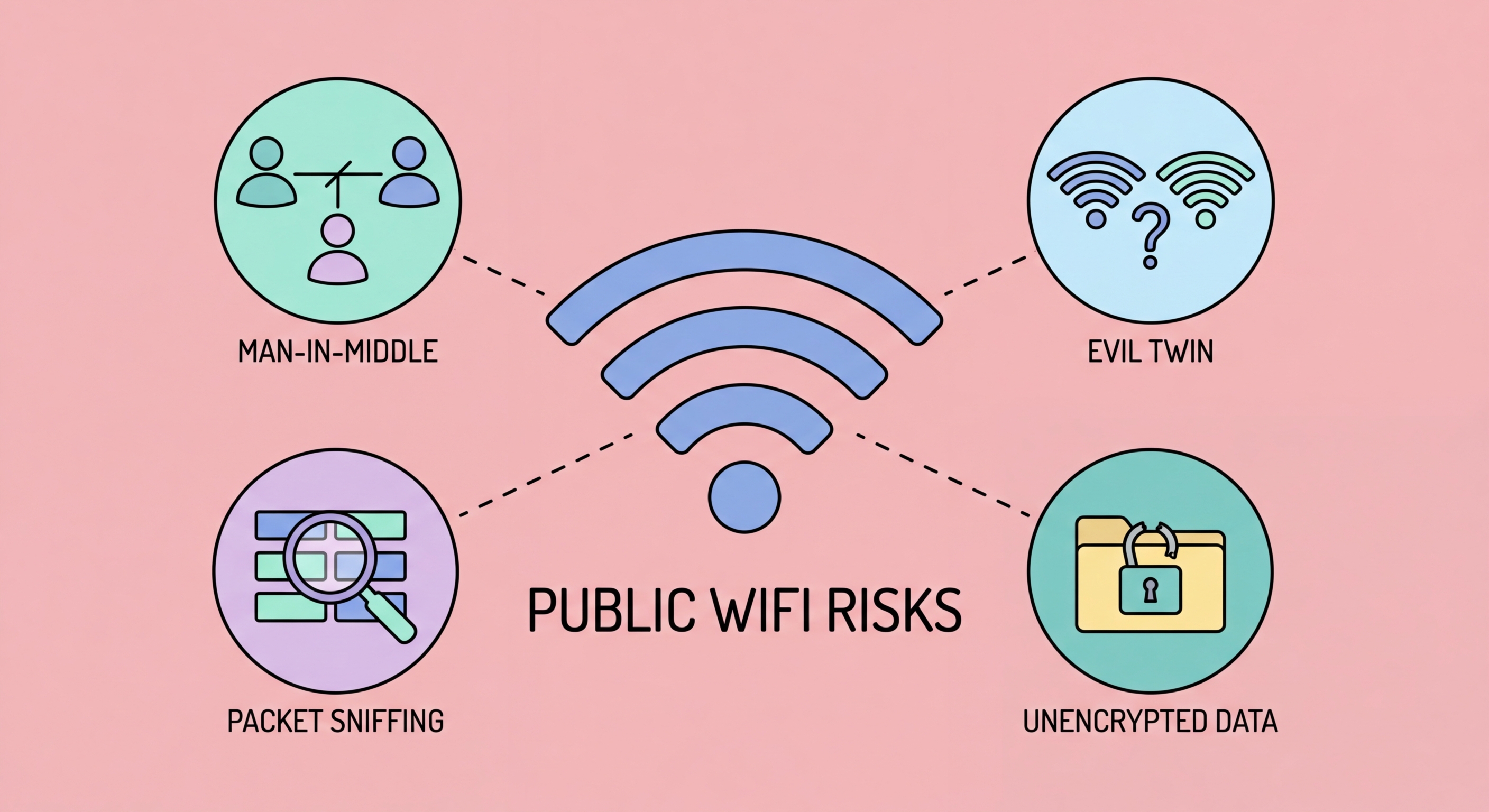
An evil twin attack creates a fake WiFi network that mimics a legitimate one. The attacker sets up a wireless access point broadcasting the same SSID (network name) as the legitimate network — for example, "CentralStation_WiFiHK" or "Pacific_Coffee_Free." If the attacker's signal is stronger than the legitimate network, nearby devices may automatically connect to the evil twin instead. If the device has previously connected to the real network, it may auto-reconnect to the evil twin without any user action, because it recognises the familiar network name.
Once you connect to an evil twin, the attacker controls your entire network connection. All your traffic — HTTPS or otherwise — passes through their equipment. While HTTPS protects the content of encrypted communications, the attacker can perform SSL stripping to prevent HTTPS upgrades, present fraudulent SSL certificates that trigger browser warnings (which many users ignore), and capture your DNS queries to see every site you attempt to visit. Evil twin attacks are particularly effective in high-traffic locations where legitimate free WiFi is expected: airports, MTR stations, hotels, and shopping malls in for Business Travellers: Protecting Corporate Data in Hong Kong">Hong Kong.
Rogue access points within corporate networks present a related but different threat. A rogue AP is an unauthorised wireless access point connected to a wired corporate network — potentially installed by a careless employee (a personal router brought to the office) or by a malicious insider. Rogue APs create wireless entry points into otherwise secure wired networks, bypassing all the network perimeter controls the organisation has implemented. For Hong Kong businesses, rogue AP detection (through wireless intrusion detection systems) is an important component of network security, particularly in open-plan office environments.
- Evil twin mechanism: Fake network with identical SSID — devices may auto-connect
- Stronger signal wins: Attackers use high-power antennas to override the legitimate network
- Auto-connect risk: Saved networks auto-connect — previously known SSIDs are particularly dangerous
- Total traffic control: All your traffic passes through the attacker's equipment
- High-risk locations: MTR, HKIA, hotel lobbies, and shopping malls are prime evil twin targets
- Defence: VPN eliminates the benefit of evil twin interception — all traffic is encrypted end-to-end
See the full guide to evil twin WiFi attacks →