1Forward vs Reverse
Reverse Proxy vs Forward Proxy: The Key Distinction
The terminology can be confusing: a forward proxy acts on behalf of clients (your device) to access servers on the internet, while a reverse proxy acts on behalf of servers to receive requests from clients on the internet. In a forward proxy setup, the proxy is configured on or near the client side, and clients explicitly or transparently route their requests through it. In a reverse proxy setup, the proxy is deployed on or near the server side, and clients have no idea — they think they're talking directly to the backend server.
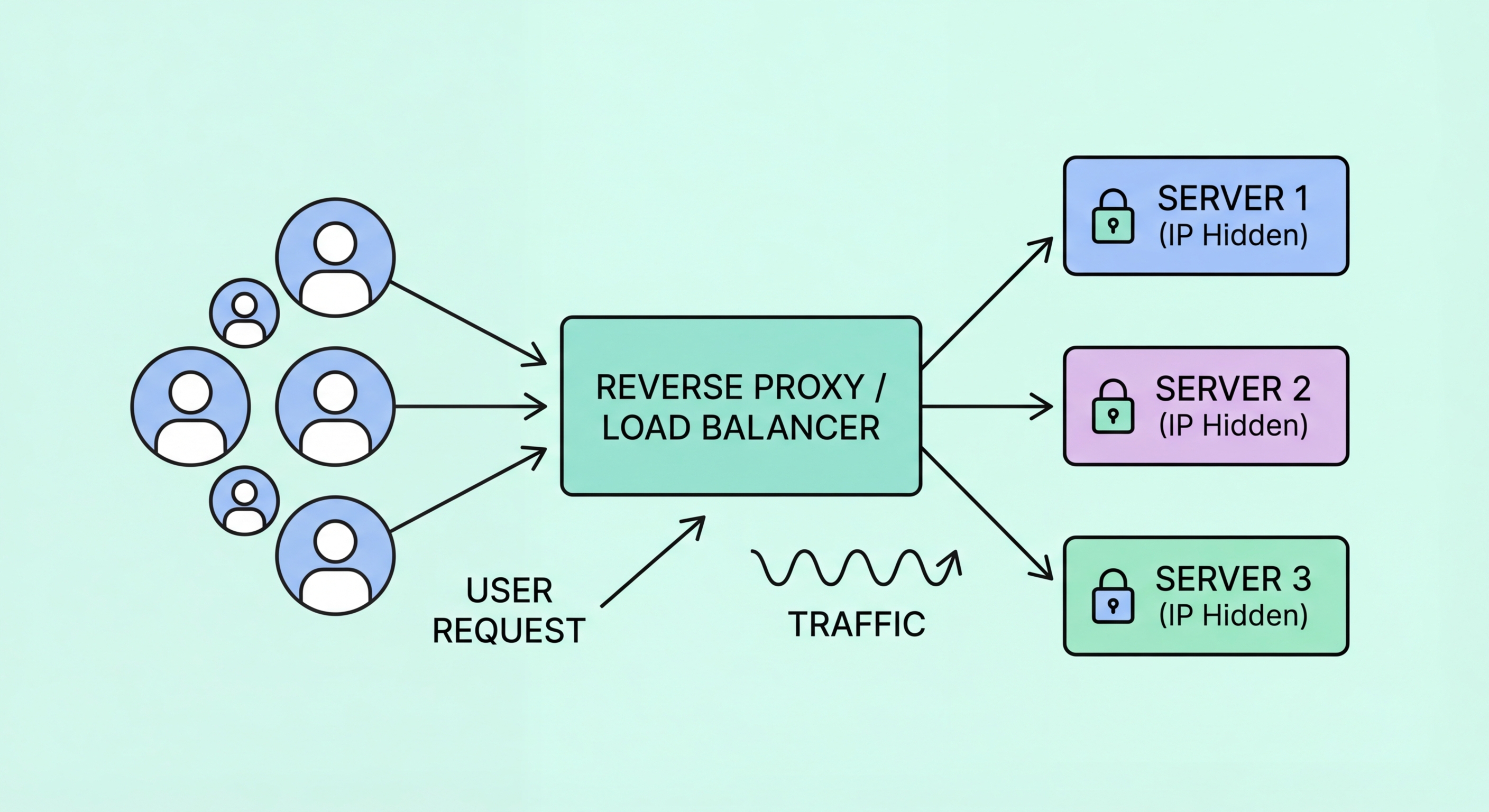
When you visit a popular website like any major e-commerce or news platform, your browser connects to an IP address that is almost certainly a reverse proxy (often a CDN node) rather than the actual web server. The reverse proxy receives your request, determines which backend server should handle it, forwards the request, receives the response, and returns it to your browser. The backend server's real IP address never appears in your browser — only the reverse proxy's IP is publicly exposed, protecting the origin server from direct internet exposure.
This architecture difference has profound implications. Forward proxies are typically deployed for the benefit of client-side privacy, access control, and traffic management. Reverse proxies are deployed for server-side benefits: protecting origin server identity, distributing traffic across multiple servers, caching content to reduce origin load, terminating TLS to offload encryption processing, and adding security layers like DDoS protection and WAF (Web Application Firewall) capabilities. The two technologies serve completely different purposes despite sharing the name "proxy."
- Forward Proxy: Acts on behalf of clients — configured at or near the client, accesses the internet for them.
- Reverse Proxy: Acts on behalf of servers — deployed at or near the server, receives requests from the internet.
- Client Visibility: In a reverse proxy setup, clients see only the proxy's IP — the backend server is hidden.
- Server Protection: Reverse proxies prevent direct exposure of origin server IPs to the public internet.
- CDN Architecture: Most CDNs function as reverse proxy networks at global scale, serving billions of requests daily.
- Purpose Difference: Forward proxies serve client privacy and access; reverse proxies serve server security and performance.