1What Is BEC
What Is Business Email Compromise and How Does It Target Hong Kong Businesses?
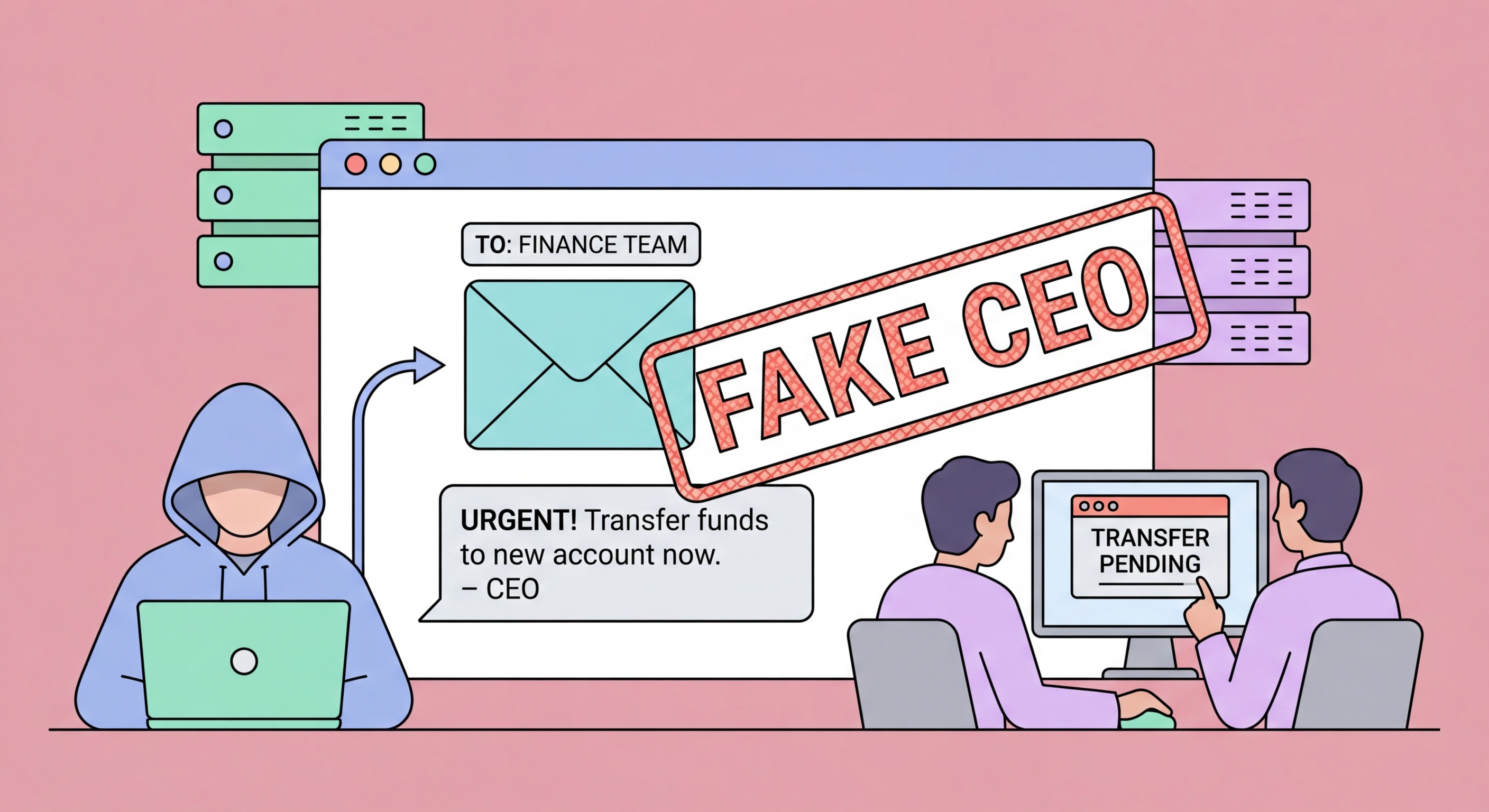
Business Email Compromise (BEC) is a category of fraud in which attackers impersonate trusted parties in a business email exchange to redirect payments or extract sensitive information. Unlike opportunistic mass phishing, BEC attacks are researched and targeted: attackers understand the target organisation's payment processes, supplier relationships, and internal approval chains before launching the attack. BEC consistently tops the FBI's Internet Crime Complaint Center reports as the highest-loss cybercrime category globally, and it is among the most significant cyber threats to Hong Hong Kong Businesses: Implementation Guide">for Hong Kong Online Banking: What You Need to Know">for Hong Kong Online Banking: A Complete Guide">for Hong Kong SMEs: Where to Start">for Hong Kong Businesses">Kong businesses, particularly those in finance, trading, real estate, and professional services where large-value transactions are routine.
BEC attacks exploit the assumption that an email from a known sender can be trusted. In reality, email sender addresses can be spoofed, email accounts can be compromised, and lookalike domains can be registered that differ from the genuine domain by a single character. A finance controller receiving what appears to be an email from their CEO, their bank, or their major supplier requesting a payment change has no reliable way to verify the sender through the email itself — only out-of-band verification (a phone call to a known number) provides real assurance. This fundamental weakness of email-based business processes is what BEC exploits.
Hong Kong's position as a regional financial hub makes its businesses particularly attractive targets. The city hosts a large number of multinational companies' regional treasury and finance functions, conducts significant cross-border transactions with mainland China and Southeast Asia, and has a business culture where email-based payment instructions from senior management are common. The combination of high-value transactions, cross-border complexity, and established email-based processes creates ideal conditions for BEC attackers who focus on financial targets with the largest potential payoffs.
- Targeted fraud: Researched, targeted attacks on specific payment processes — not mass phishing
- Email trust exploitation: Exploits the assumed trustworthiness of known sender email addresses
- Spoofing and compromise: Sender addresses spoofed or genuine accounts compromised — both enable convincing fraud
- Highest-loss category: BEC tops global cybercrime loss rankings consistently — large individual transactions make HK high-value
- HK exposure sectors: Finance, trading, real estate, professional services — large-value cross-border transactions
- Regional treasury risk: Multinational regional finance functions in HK are high-value BEC targets
How targeted spear phishing research enables BEC →