What Is Two-Factor Authentication? The Complete Guide
Two-factor authentication adds a critical second layer of security to your accounts. Even if attackers steal your password, they cannot get in without the second factor — only you have.
Two-factor authentication adds a critical second layer of security to your accounts. Even if attackers steal your password, they cannot get in without the second factor — only you have.
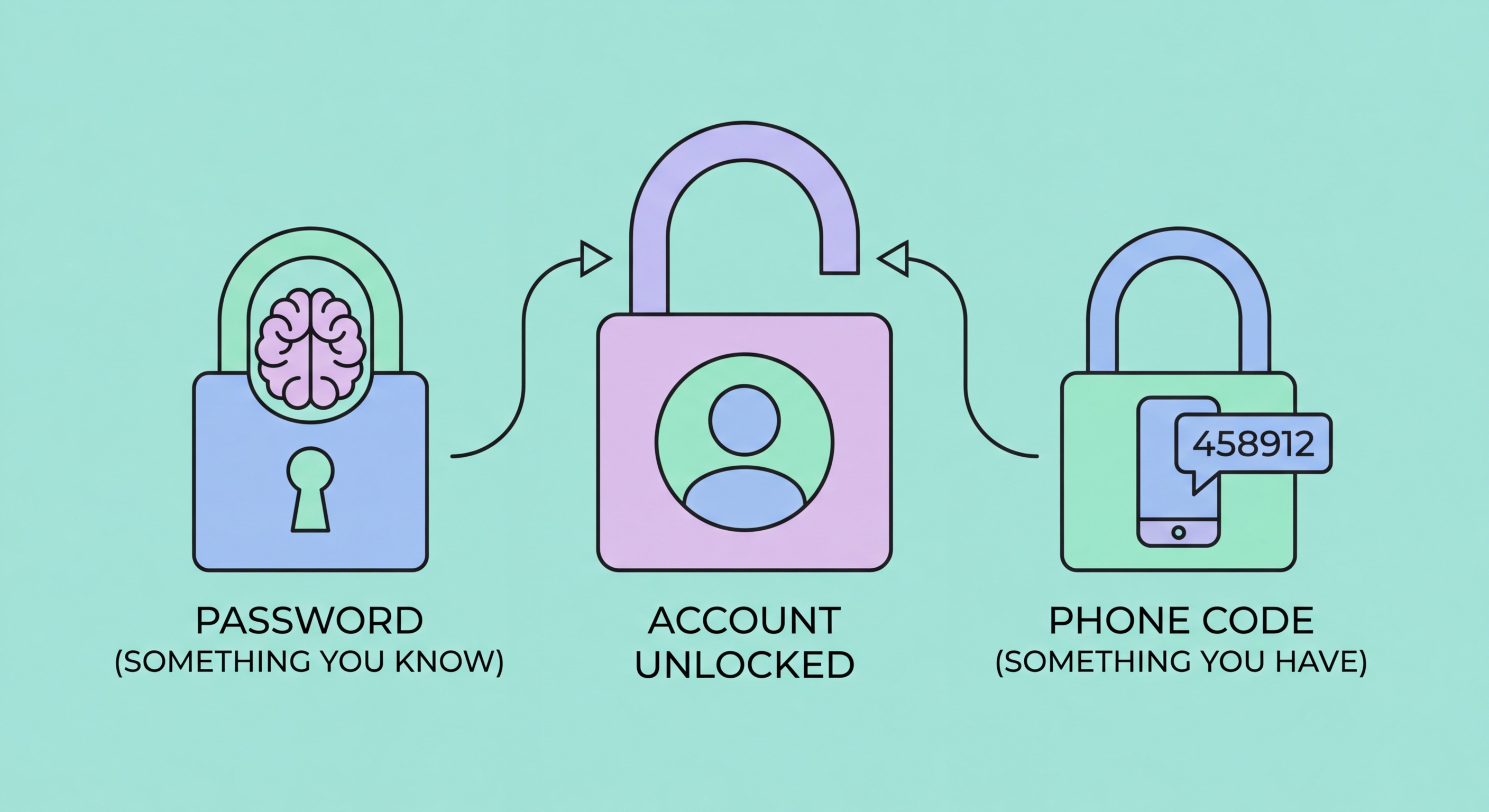
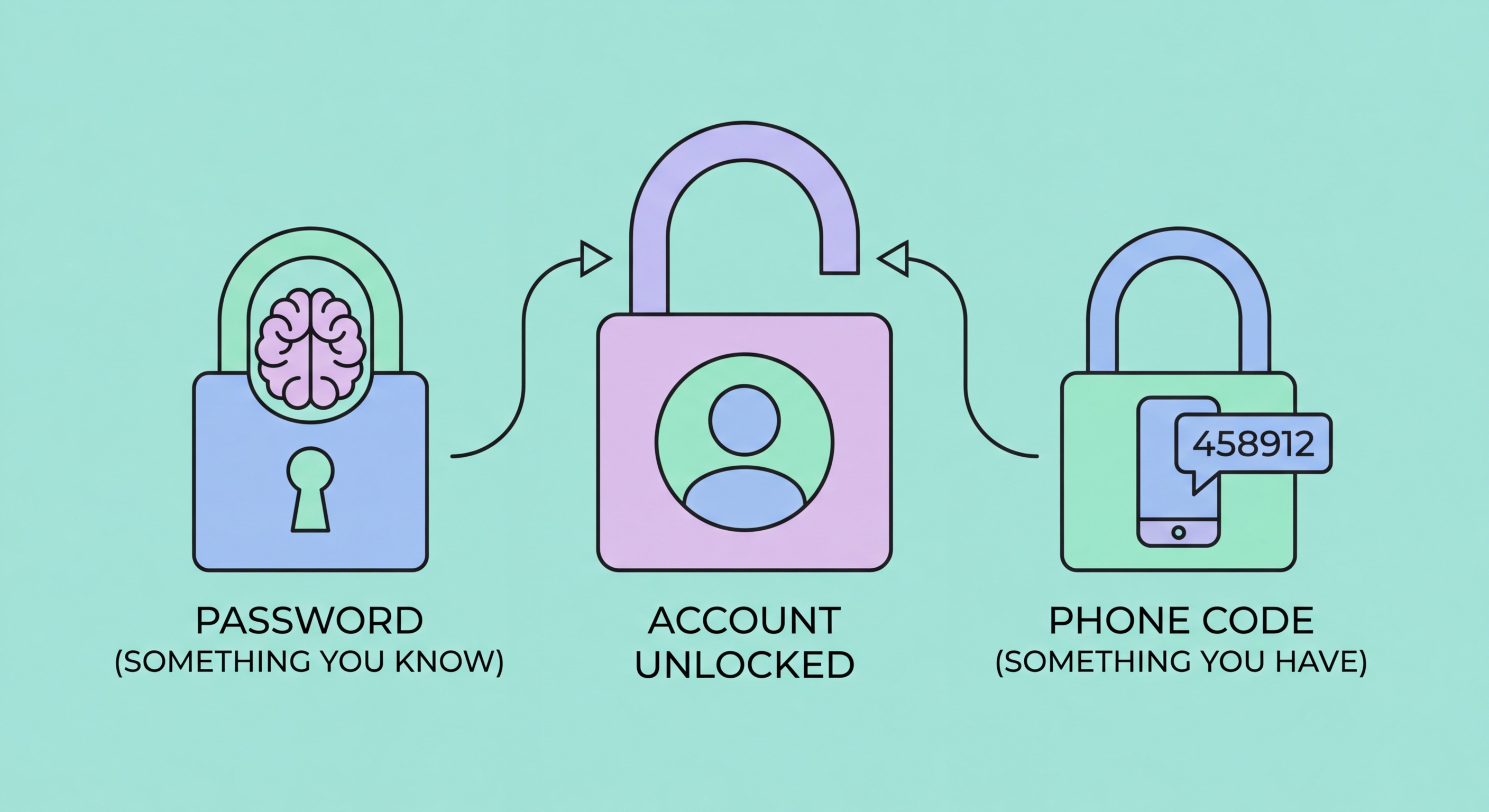
Two-factor authentication (2FA) is a security process that requires you to provide two separate and distinct forms of identification before you can access an account or system. The concept is built on the idea that any single verification method — including a password — can be compromised, but requiring two independent factors simultaneously makes unauthorised access exponentially more difficult.
The three recognised categories of authentication factors are: something you know (a password, PIN, or security question), something you have (a smartphone, hardware token, or smart card), and something you are (a fingerprint, face scan, or other biometric). Two-factor authentication combines any two of these categories. The most common implementation pairs a password (something you know) with a code from to Spot and Avoid Attacks on Your Phone">your phone (something you have).
The term is often used interchangeably with "two-step verification" and falls under the broader category of multi-factor authentication (MFA). While technically distinct — 2FA specifically means exactly two factors, whereas MFA can mean two or more — in practice the terms describe the same experience for most users. What matters most is that you are adding a meaningful second barrier between attackers and your accounts.

Passwords are fundamentally broken as a sole security mechanism. Every year, billions of account credentials are leaked through data breaches at major companies — from LinkedIn to Facebook to Adobe. These databases of stolen usernames and passwords are sold on dark web markets and used in automated "credential stuffing" attacks that try leaked credentials across thousands of websites simultaneously. If you reuse passwords — and studies show most people do — a breach of one service can cascade into account takeovers across your entire digital life.
Even strong, unique passwords are vulnerable to phishing attacks, where criminals create convincing fake login pages to steal your credentials directly. Sophisticated phishing pages now operate in real-time, instantly using your credentials to log in to the real service while showing you a fake error message. Without 2FA, there is nothing to stop this attack. With 2FA using an authenticator app, the attacker would also need access to your phone at the same moment — a dramatically harder challenge.
In Hong Kong specifically, cyberattacks have targeted banking customers, business email accounts, and government service portals. The Hong Kong Computer Emergency Response Team Coordination Centre (HKCERT) regularly reports on credential theft campaigns targeting HK residents. Enabling 2FA is the single most effective defensive step the average person can take — Microsoft research found that 2FA blocks over 99.9% of automated account compromise attacks.

SMS-based 2FA sends a one-time code to your mobile phone via text message. It's the most widely deployed form of 2FA and the easiest to set up. However, it has well-documented weaknesses: SMS messages can be intercepted through SS7 protocol vulnerabilities, and attackers can transfer your phone number to a device they control through SIM swapping — a social engineering attack that exploits telecoms customer service processes. SMS 2FA is better than no 2FA, but should be upgraded when possible.
Authenticator app 2FA uses the Time-based One-Time Password (TOTP) standard to generate six-digit codes that change every 30 seconds. These codes are generated entirely on your device using a shared secret established when you scan the setup QR code — they never travel through the phone network. This means no SIM swap attack can intercept them. Apps like Google Authenticator, Authy, and Microsoft Authenticator all use this standard and are interoperable with thousands of services.
Hardware security keys represent the gold standard of 2FA. Physical devices like YubiKey connect via USB or NFC and use public-key cryptography to authenticate you. Because the key cryptographically verifies that the website you're logging into is the genuine site, they are completely phishing-resistant — even if you're tricked into visiting a fake login page, the key will refuse to authenticate. Passkeys are an emerging software implementation of similar cryptographic principles, built into operating systems and browsers for a seamless experience.

The most effective approach to adopting 2FA is to prioritise by account value and attack surface. Your email account is the highest priority: because virtually every other service allows password resets by email, whoever controls your inbox effectively controls all your accounts. Enable 2FA on your primary email address first, then your mobile banking apps, then social media and shopping accounts.
When setting up 2FA, always download and safely store your backup codes before completing the process. These are emergency one-time codes that allow you to regain access if you lose your phone or authenticator app. Store them in a password manager, a secure notes app, or printed in a physically secure location. Losing access to your 2FA device without backup codes can result in permanent account lockout.
For Hong Kong users, it is also worth calling your mobile carrier (SmarTone, CMHK, 3HK, or CSL) to add a SIM lock PIN to your account. This prevents a criminal from walking into a carrier store and transferring your number to a new SIM, which is the mechanism behind SIM swap attacks. This carrier-level protection complements your 2FA setup and closes a critical gap in SMS-based authentication.
