2IRP Structure and Phases
Incident Response Plan Structure: The Six Phases
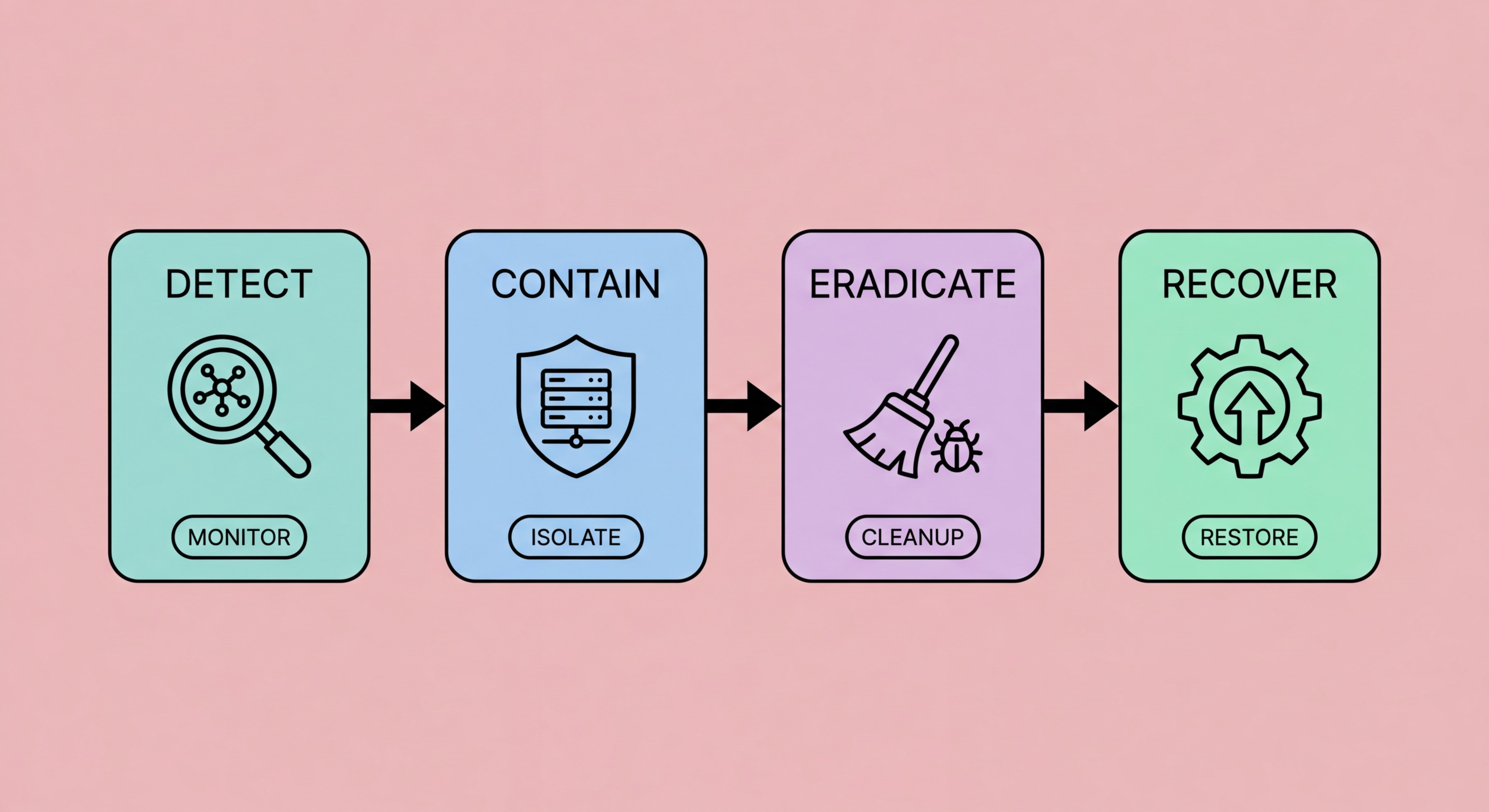
A well-structured incident response plan follows six phases: preparation, identification, containment, eradication, recovery, and lessons learned. Preparation occurs before any incident — it is the planning, training, and tooling that makes the subsequent phases effective. Identification is the detection and initial assessment of a potential incident — determining whether an anomaly represents an actual security incident, what type, and its apparent scope. Containment stops the incident from spreading while preserving evidence for investigation. Eradication removes the threat entirely. Recovery restores normal operations. Lessons learned captures what happened and improves future response.
For the identification phase, your IRP should define what constitutes a security incident for your organisation and establish clear escalation triggers. Potential incident indicators include: unusual system alerts from endpoint protection or SIEM, employee reports of suspicious emails or behaviour, unusual account activity flagged by cloud application monitoring, reports from customers or partners of suspicious communications claiming to be from your organisation, or external notification from HKPF CSTCB or your internet service provider. The IRP should specify who receives these reports, how they are assessed for severity, and the criteria for declaring a formal security incident that activates the full IRP response.
Containment strategy in your IRP should provide pre-approved action playbooks for the most likely incident types your business faces. Ransomware containment requires different immediate actions than a phishing credential harvest — ransomware requires rapid network isolation to prevent lateral spread, while credential compromise requires immediate password reset and session revocation. Having incident-type-specific playbooks that detail the sequence of containment actions, the systems and personnel involved, and the authority required for each action eliminates the need to design containment strategy from scratch during an active crisis. NIST SP 800-61 provides detailed guidance on incident response procedures that HK businesses can adapt for their context.
- Six-phase IRP framework: Preparation, identification, containment, eradication, recovery, and lessons learned — each phase requires specific pre-defined procedures
- Incident severity classification: Define severity levels (critical, high, medium, low) with clear criteria — severity determines response urgency, escalation path, and resource allocation
- Incident type playbooks: Create specific playbooks for ransomware, phishing, data breach, BEC fraud, and account takeover — each requires different containment actions
- Eradication completeness verification: The eradication phase must verify complete threat removal — partial eradication leaves backdoors that result in repeat incidents within weeks
- Recovery sequencing: Restore systems in priority order based on business criticality — define system criticality rankings in advance in your IRP
- Lessons learned process: Conduct a structured post-incident review within 2 weeks — capture timeline, root cause, what worked, what failed, and specific IRP improvements