2What Phishing-Resistance Means
The Property That Makes FIDO2 Immune to Phishing
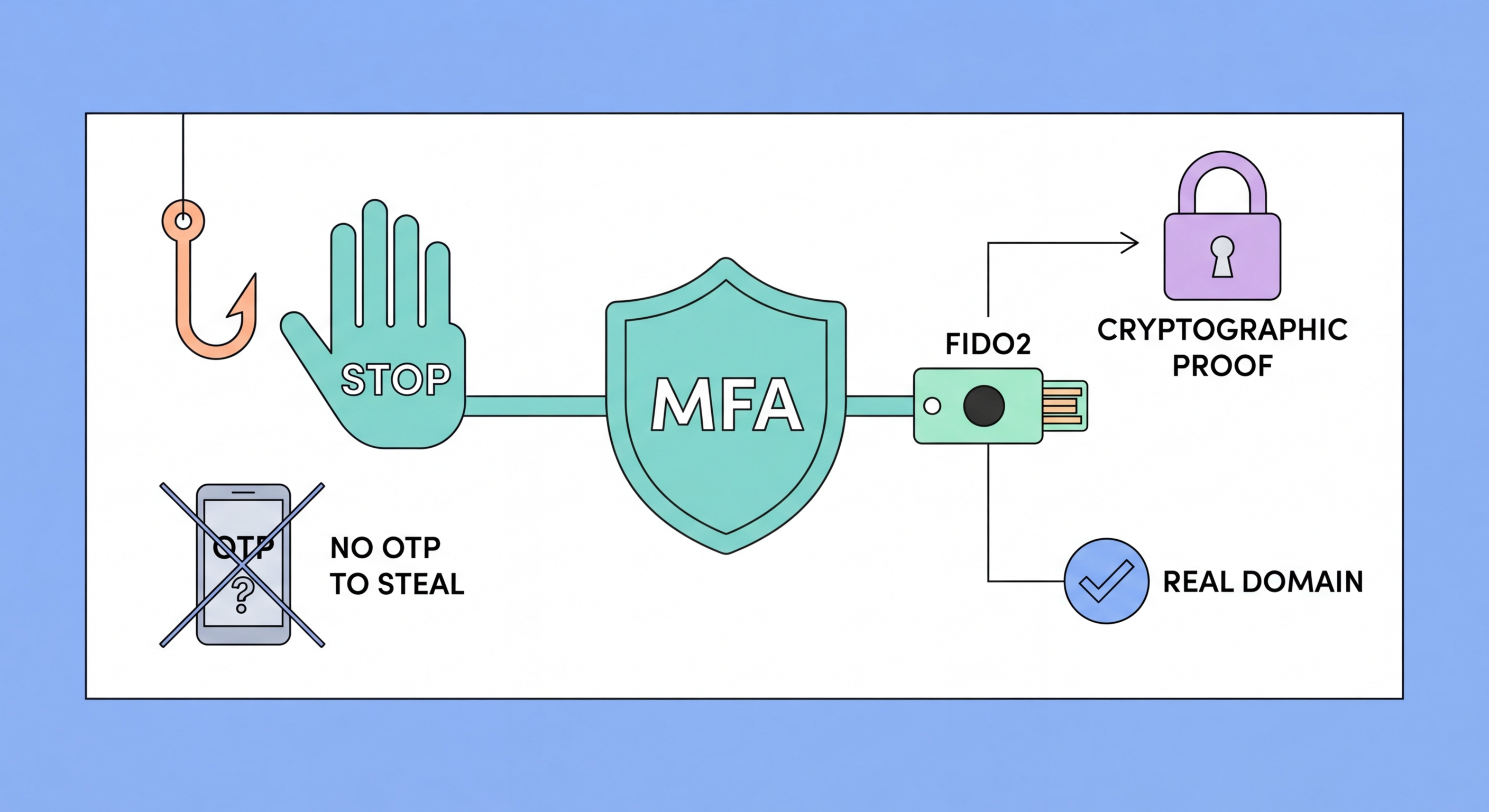
Phishing-resistant MFA is defined by a specific cryptographic property: the authentication is bound to the exact origin (domain) of the service being accessed, and this binding is enforced by the authenticator itself rather than by user vigilance. With FIDO2 (the standard used by hardware keys and passkeys), when you register with a service, the authenticator records the service's exact domain. At every subsequent authentication, the authenticator cryptographically verifies that the request is coming from that exact domain before performing the signing operation.
If a phishing site at g00gle.com (with zeros instead of "o"s) attempts to authenticate you using your Google passkey or hardware key, the authenticator checks its registration records, finds no match for g00gle.com, and refuses to authenticate. This is not a user interface check that can be bypassed by a convincing fake — it is a cryptographic operation that the device performs based on the exact bytes of the domain string, and it cannot be overridden or spoofed. No relay attack can work against FIDO2 because the authentication response is cryptographically specific to the exact domain and the specific challenge issued by that domain in that specific session.
The US government's Cybersecurity and Infrastructure Security Agency (CISA) published guidance specifically recommending phishing-resistant MFA — defined as FIDO2/WebAuthn hardware keys and passkeys — as the standard for federal agencies and critical infrastructure. CISA explicitly warned that TOTP codes, SMS codes, and push notifications do not meet the phishing-resistant definition, despite being better than no MFA. This guidance has been widely adopted by security professionals as the standard for high-risk environments, and is increasingly referenced in enterprise security policies globally.
- Origin binding: FIDO2 authentication is cryptographically bound to the exact domain of the service
- Device-enforced: The authenticator checks the domain — not the user, who can be deceived
- Phishing impossible: Even a pixel-perfect fake login page cannot receive a valid FIDO2 authentication
- Relay impossible: The response is specific to the challenge — cannot be relayed from a different session
- CISA standard: US government guidance defines phishing-resistant MFA as FIDO2/WebAuthn only
- Not phishing-resistant: TOTP, SMS, email codes, and push notifications are all excluded
See the technical details of FIDO2 domain binding in action →