VPN for Business: Enterprise Security Guide
For Hong Kong businesses, VPNs are critical infrastructure — protecting corporate data, enabling secure remote access, and supporting PDPO data protection compliance.
For Hong Kong businesses, VPNs are critical infrastructure — protecting corporate data, enabling secure remote access, and supporting PDPO data protection compliance.
For businesses, VPNs serve a fundamentally different purpose than consumer use. While consumer VPNs primarily address privacy from ISPs and geo-restriction bypass, enterprise VPNs are critical security infrastructure that protects corporate assets, enables secure remote access to internal systems, and maintains compliance with data protection regulations. In Hong Kong's international business environment — where employees frequently travel between HK, mainland China, Southeast Asia, and beyond — enterprise VPN is table stakes, not a nice-to-have.
The security case is clear: without a VPN, remote access to corporate systems means either exposing those systems directly to the internet (requiring strict firewall management and creating a significant attack surface) or requiring employees to be physically present in the office. A VPN creates an authenticated, encrypted tunnel through which remote employees access internal resources — file servers, databases, ERP systems, intranet — exactly as if they were sitting in the office, without exposing those resources to unauthenticated internet traffic.
The business continuity case is equally compelling. Post-pandemic work patterns in It Protects and How to Use It">on Public WiFi: Why It's Essential in Hong Kong">Hong Kong have permanently increased expectations for remote work flexibility. Businesses without robust VPN infrastructure cannot support hybrid work arrangements without unacceptable security compromises. Additionally, businesses with mainland China operations require cross-border VPN connectivity — either through leased lines (expensive for SMEs) or business VPN solutions with China-compliant infrastructure — to maintain reliable communication between HK and mainland offices.
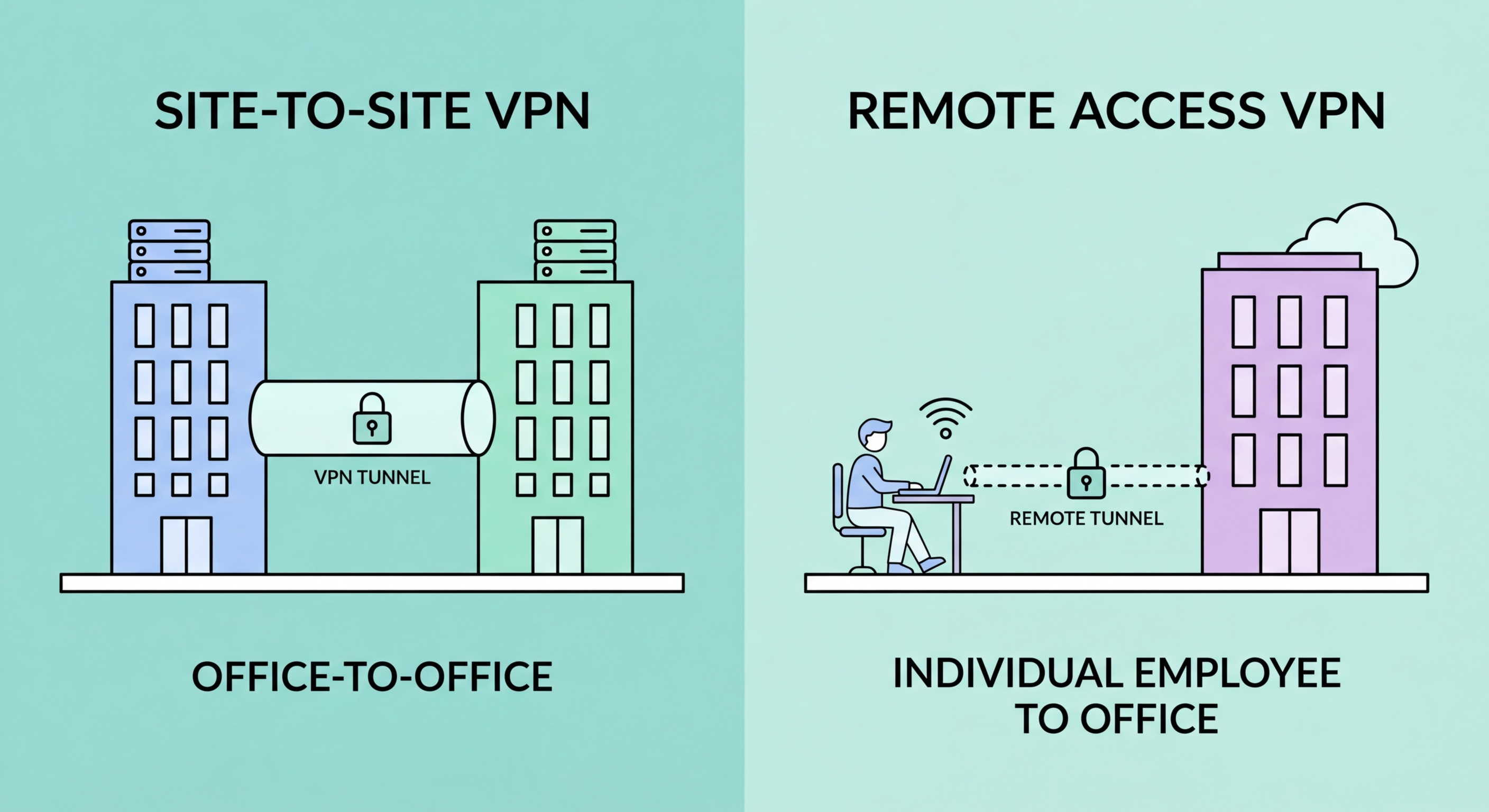
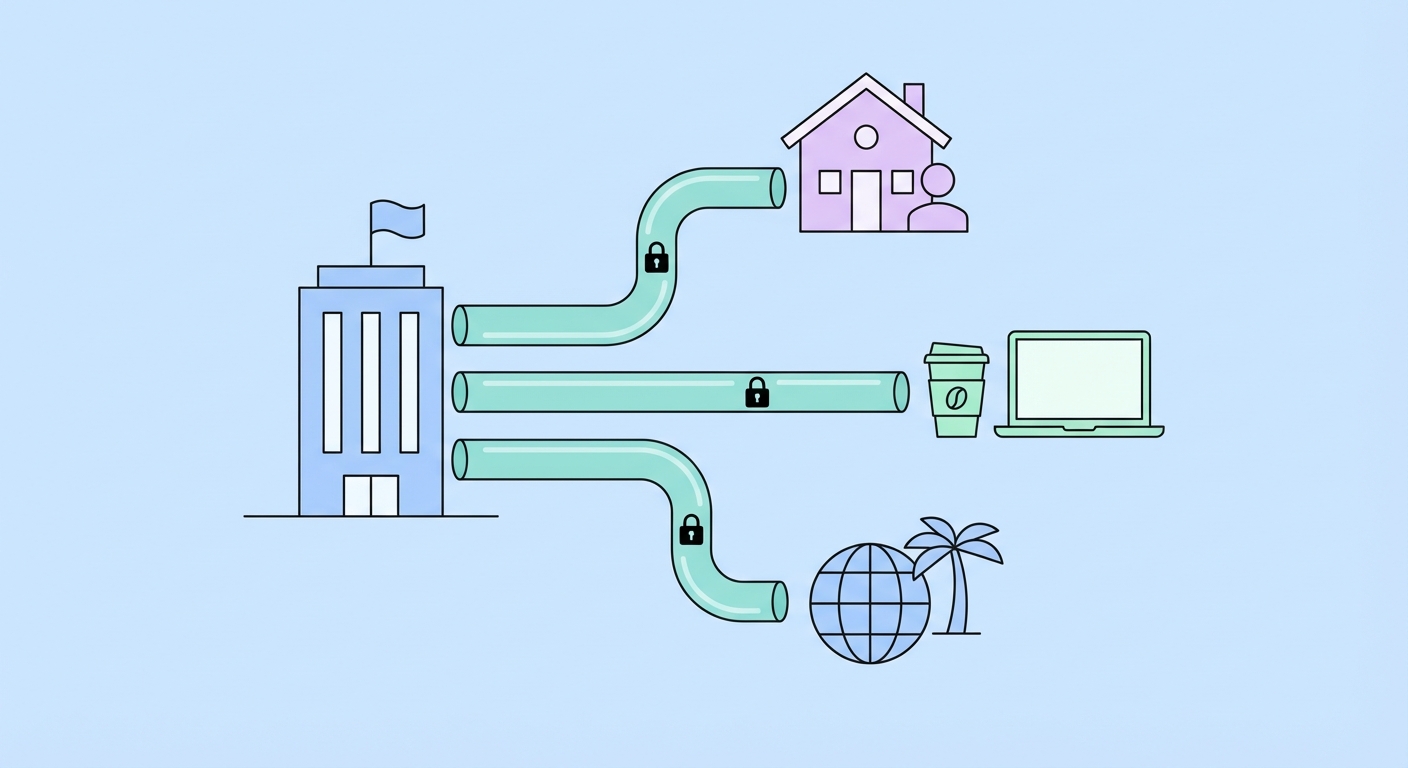
Enterprise VPNs divide into two architectural categories serving different business needs: site-to-site VPNs and remote access VPNs. Understanding the distinction — and when to use each — is essential for building appropriate network security infrastructure.
A site-to-site VPN creates a permanent encrypted tunnel between two or more fixed locations — for example, between a business's Hong Kong headquarters and its Shenzhen office. Traffic between the two sites travels through this tunnel automatically, without any action required from end users. From the employee's perspective, resources in the remote office appear as accessible as local resources. Site-to-site VPNs are managed at the router/firewall level (using enterprise equipment like Cisco ASA, Fortinet, Palo Alto, or pfSense) and require VPN-capable routers at each endpoint. For businesses with multiple offices across HK, China, and APAC, site-to-site VPNs create a unified private network infrastructure without the cost of dedicated leased lines.
A remote access VPN (also called client-to-site VPN) allows individual users — remote workers, travelling employees, or third-party contractors — to connect to the corporate network from any location using a VPN client installed on their device. Solutions in this category include Cisco AnyConnect (industry standard for large enterprises), Palo Alto GlobalProtect, Pulse Secure, and the open-source OpenVPN Access Server (suitable for SMEs). Remote access VPNs authenticate users individually (typically with AD/LDAP credentials plus MFA) and can be configured with granular access control policies — sales employees access CRM but not financial systems, for example.

Hong Kong's Personal Data (Privacy) Ordinance (PDPO, Cap. 486) establishes six Data Protection Principles (DPPs) that govern how organisations collect, store, process, and protect personal data. VPN implementation directly supports compliance with Data Protection Principle 4 (DPP4 — Data Security), which requires data users to take all practicable steps to protect personal data against unauthorised or accidental access, processing, erasure, loss, or use.
When employees handle personal data while working remotely — processing customer records, HR data, client financial information, or any other personal data covered by PDPO — that data is transmitted over internet connections. Without encryption, personal data transmitted over home WiFi, mobile networks, or public hotspots is potentially exposed to interception. A VPN encrypts this data in transit, directly satisfying the "practicable steps" requirement of DPP4 for data transmitted outside the corporate network. Security regulators increasingly view encrypted remote access (VPN) as a minimum standard for organisations handling personal data.
Beyond DPP4, VPN implementation supports PDPO compliance in other ways: access control (remote access VPNs authenticate users before granting system access, supporting the principle of access limitation), audit trails (VPN connection logs provide evidence of who accessed what systems and when, supporting incident investigation and regulatory reporting), and data transfer security (VPNs protect personal data transferred between HK and mainland China operations, relevant to PDPO's provisions on cross-border data transfer).

Business VPN selection involves different criteria than consumer VPN selection. While speed and privacy are important, enterprise requirements also include: scalability (can the solution grow from 10 to 500 users?), centralized management (IT admin portal for user provisioning, policy enforcement, access control), MFA integration (RADIUS, SAML, Azure AD), detailed access logging for compliance and incident response, SLA guarantees for uptime, and vendor support levels appropriate for business-critical infrastructure.
For large enterprises (100+ users), industry-standard solutions include Cisco AnyConnect (dominant in Fortune 500 enterprises; expensive licensing but extensive feature set), Palo Alto GlobalProtect (integrated with Palo Alto NGFW; excellent security policy granularity), and Pulse Secure. These solutions integrate with existing enterprise directory services (Active Directory, LDAP) and support advanced features like split tunnelling policies enforced by IT, network access control (NAC), and host compliance checking (verifying devices have current antivirus/patches before granting VPN access).
For SMEs in Hong Kong (5–100 users), more cost-effective options include: OpenVPN Access Server (open-source with a commercial management portal; excellent value with strong security), WireGuard with commercial management overlays (Tailscale, Netmaker, or Headscale provide enterprise-friendly management on top of WireGuard), and business-tier consumer VPN solutions (NordVPN Teams/NordLayer, Perimeter 81, Twingate). These SME-focused solutions provide central management portals, user provisioning, and access logging without the complexity and cost of enterprise solutions.