VPN Protocols Explained: OpenVPN, WireGuard & More
The protocol you choose shapes your VPN's speed, security, and ability to bypass censorship. Here's everything you need to make the right call.
The protocol you choose shapes your VPN's speed, security, and ability to bypass censorship. Here's everything you need to make the right call.
A VPN protocol is the set of rules and procedures that governs how a VPN client and server establish their encrypted connection, maintain it, and transfer data through it. You can think of a protocol as the language that both ends of a VPN connection speak — if they're using the same protocol, they can communicate securely; if they're not, the Difference and the Connection">the connection fails.
Different protocols make fundamentally different engineering trade-offs. Some prioritise raw speed by using lighter encryption overhead — ideal for streaming 4K video or competitive gaming. Others prioritise stealth, disguising VPN traffic as ordinary HTTPS browsing to evade deep packet inspection (DPI) firewalls used in restrictive network environments. Still others prioritise broad device compatibility, working across older hardware and unusual network configurations.
The protocol choice also affects the encryption ciphers and key exchange mechanisms available. For example, WireGuard is hardcoded to use ChaCha20-Poly1305 for encryption and Curve25519 for key exchange — modern, audited algorithms with a clean security track record. OpenVPN supports a wide range of ciphers, which is both a strength (flexibility) and a weakness (misconfiguration risk). Understanding these trade-offs helps you choose the protocol that matches your specific threat model and use case.
WireGuard was released as a stable version in 2020 and has since been adopted by virtually every major VPN provider as their primary recommended protocol. Its design philosophy is radical simplicity: the entire codebase is approximately 4,000 lines of code, compared to OpenVPN's 70,000+ lines. This isn't just aesthetically elegant — a smaller codebase means fewer places for vulnerabilities to hide, and the entire protocol has been independently audited multiple times with exemplary results.
WireGuard's performance advantage comes from its use of state-of-the-art cryptographic primitives and its operation at the kernel level in Linux (where most VPN servers run). It uses ChaCha20 for symmetric encryption, Poly1305 for message authentication, Curve25519 for key exchange, BLAKE2 for hashing, and SipHash for hashtable keys — all modern, high-performance algorithms. In benchmark tests, WireGuard consistently achieves 2–4x the throughput of OpenVPN at equivalent hardware, with significantly lower latency.
One limitation of WireGuard is privacy-related: by default, WireGuard assigns static IP addresses to peers and stores connection timestamps on the server. Reputable VPN providers like Mullvad, NordVPN (using NordLynx), and ExpressVPN have addressed this by implementing proprietary solutions that generate ephemeral IP addresses, ensuring compliance with their no-logs policies. Always verify how your chosen VPN handles WireGuard's IP persistence before relying on it for sensitive use.

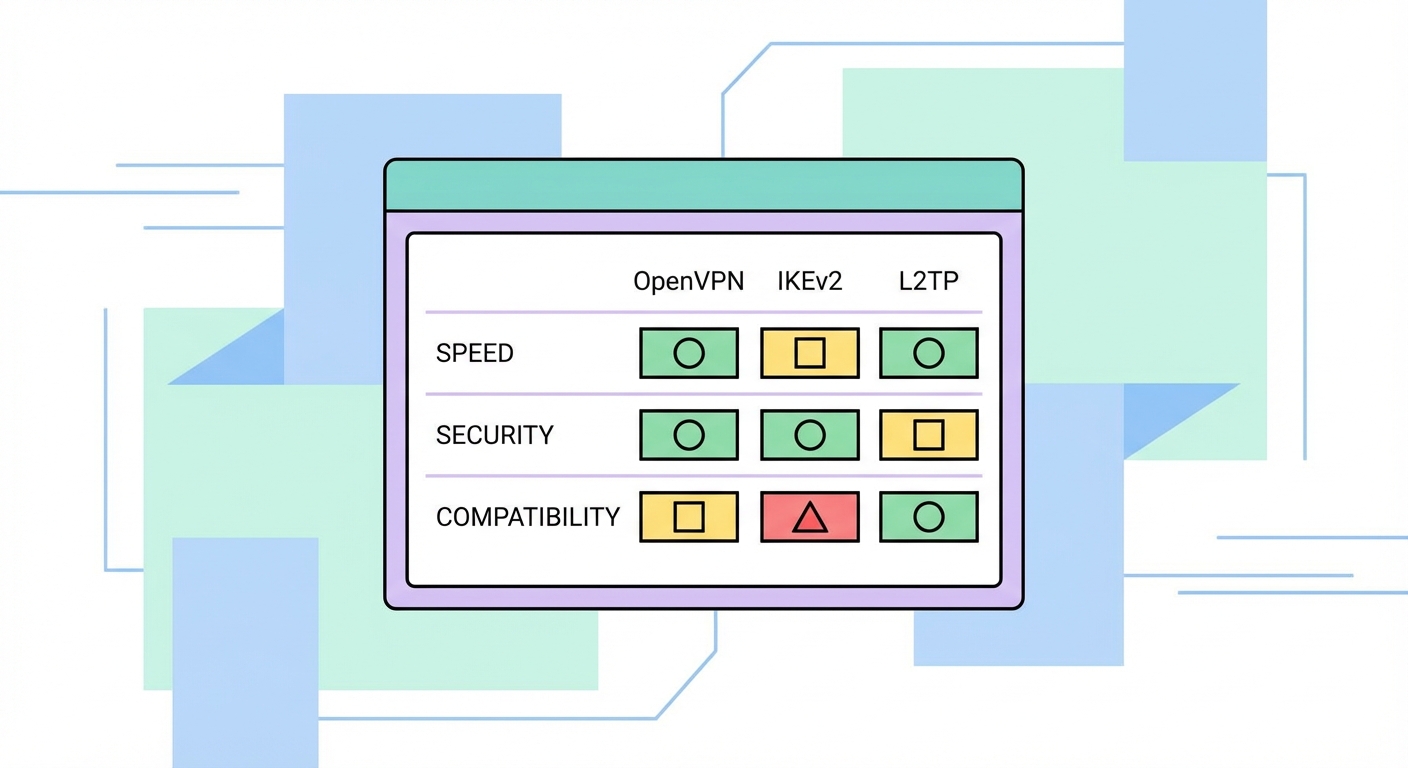
OpenVPN remains the most widely trusted protocol after WireGuard. It's open-source, independently audited, and supports both UDP (faster) and TCP (more reliable on restricted networks) transport modes. Running OpenVPN over TCP port 443 makes the VPN traffic virtually indistinguishable from normal HTTPS browsing — a critical feature for users in censorship-heavy environments. However, OpenVPN's flexibility comes at a cost: it's more complex to configure correctly, and misconfiguration can introduce vulnerabilities.
IKEv2/IPSec is developed by Microsoft and Cisco and is natively supported on Windows, macOS, iOS, and Android without requiring third-party software. Its killer feature is MOBIKE (IKEv2 Mobility and Multihoming Protocol), which allows seamless handoff between network interfaces. When your iPhone switches from your home WiFi to 5G on the MTR, IKEv2 reconnects the VPN automatically without dropping your session. This makes it the best protocol for mobile-first users. Cryptographically, IKEv2 is solid — using AES-256 and SHA-2, with Perfect Forward Secrecy via Diffie-Hellman groups.
L2TP/IPSec was once a popular choice but is now considered legacy. Its security depends entirely on the IPSec layer — L2TP itself provides no encryption. More concerning, documents leaked by Edward Snowden suggested the NSA may have worked with the IETF to weaken IPSec's cryptographic standards. Whether or not you find that credible, there are better alternatives available, and L2TP should not be used for high-stakes privacy needs. PPTP is even older and definitively broken — its RC4-based MPPE encryption was cracked years ago.
For most users in It Protects and How to Use It">on Public WiFi: Why It's Essential in Hong Kong">Hong Kong under normal circumstances, WireGuard is the clear first choice. It's the fastest, most modern, and has an excellent security track record. Every major VPN provider now supports WireGuard or a proprietary implementation of it (like NordVPN's NordLynx or ExpressVPN's Lightway). Set your VPN app to "Auto" or select WireGuard explicitly, and you'll get the best balance of speed and security for everyday browsing, streaming, and remote work.
If you're travelling to mainland China or operating in another heavily filtered network environment where VPN traffic is actively blocked, switch to OpenVPN over TCP port 443 with obfuscation enabled. Some providers offer additional stealth protocols like Shadowsocks, V2Ray integration, or their own obfuscation layers (NordVPN's Obfuscated Servers, ExpressVPN's Lightway with obfuscation). These protocols specifically disguise VPN traffic as normal HTTPS to evade deep packet inspection at the network level.
For mobile users who frequently switch between WiFi and mobile data, IKEv2 is a strong alternative to WireGuard — it handles network transitions more gracefully on some older iOS and Android versions. If your VPN provider offers "auto" protocol selection, this feature usually picks the optimal protocol for your current network conditions automatically, which is the simplest approach for non-technical users.