3SSL Stripping
SSL Stripping: Defeating HTTPS on Public WiFi
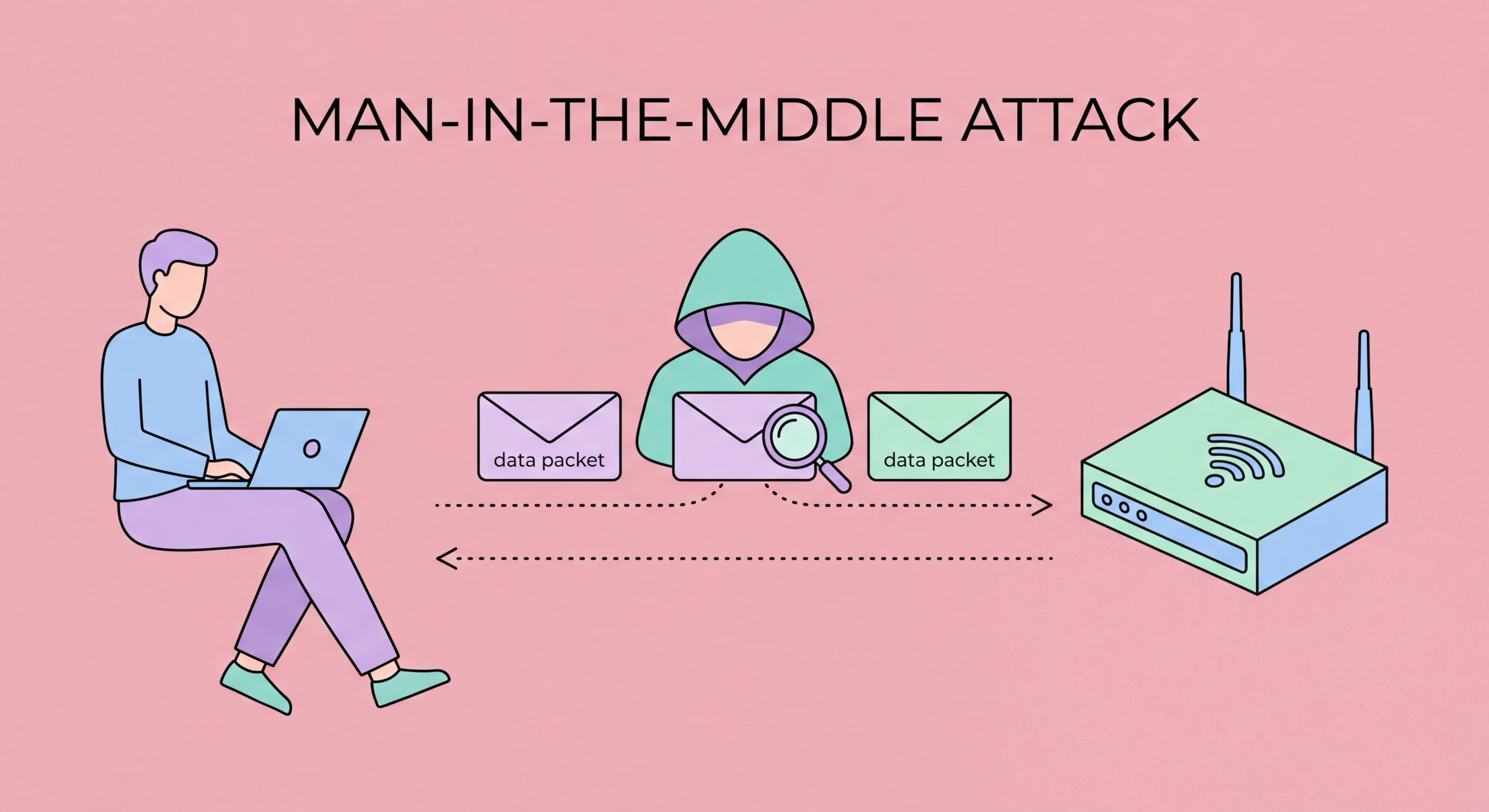
Once positioned as a man-in-the-middle, attackers frequently employ SSL stripping to defeat HTTPS protection. SSL stripping exploits the way many web browsers initially connect to websites. When you type "bank.com" into your browser, the initial connection often begins as HTTP (unencrypted) before redirecting to HTTPS. In an SSL stripping attack, the MITM intercepts the initial HTTP connection, establishes an HTTPS connection to the real server on your behalf, but serves you the website over HTTP — stripping away the encryption layer that would normally protect your connection.
From your perspective, the website functions normally — you can see all the content, log in, and interact with the site. But you are communicating with the attacker's proxy over HTTP, while the proxy communicates with the real server over HTTPS. Everything you type — including your username, password, credit card number, or any other sensitive data — is visible to the attacker in plaintext before being forwarded to the real server. Your browser may show "http://" instead of "https://" in the address bar, which is why security-conscious users always verify the protocol indicator, but many users do not check this habitually.
Modern browsers implement HSTS (HTTP Strict Transport Security), which helps mitigate SSL stripping. HSTS tells browsers to always use HTTPS for a specific domain — once a browser has visited a site with HSTS enabled, it will refuse to connect over HTTP and will not load the site if the HTTPS connection fails. Most major websites implement HSTS with long max-age periods. However, HSTS protection only works if you have previously visited the site over HTTPS with a clean connection — your first-ever visit to a site is still vulnerable to SSL stripping if it happens on a compromised network.
- Mechanism: Attacker intercepts initial HTTP connection, serves website over HTTP while connecting to server via HTTPS
- Victim experience: Website works normally — victim cannot tell the attack is happening
- Address bar tells: URL shows "http://" not "https://" — check the address bar carefully
- HSTS mitigation: Browsers refuse HTTP connections to HSTS-enabled domains after first HTTPS visit
- First-visit gap: HSTS cannot protect your first visit to a site if it occurs on a compromised network
- VPN eliminates: End-to-end encryption from device means SSL stripping cannot work
Understand what HTTPS actually protects on public WiFi →