2What HTTPS Misses
What HTTPS Does Not Protect on Public WiFi
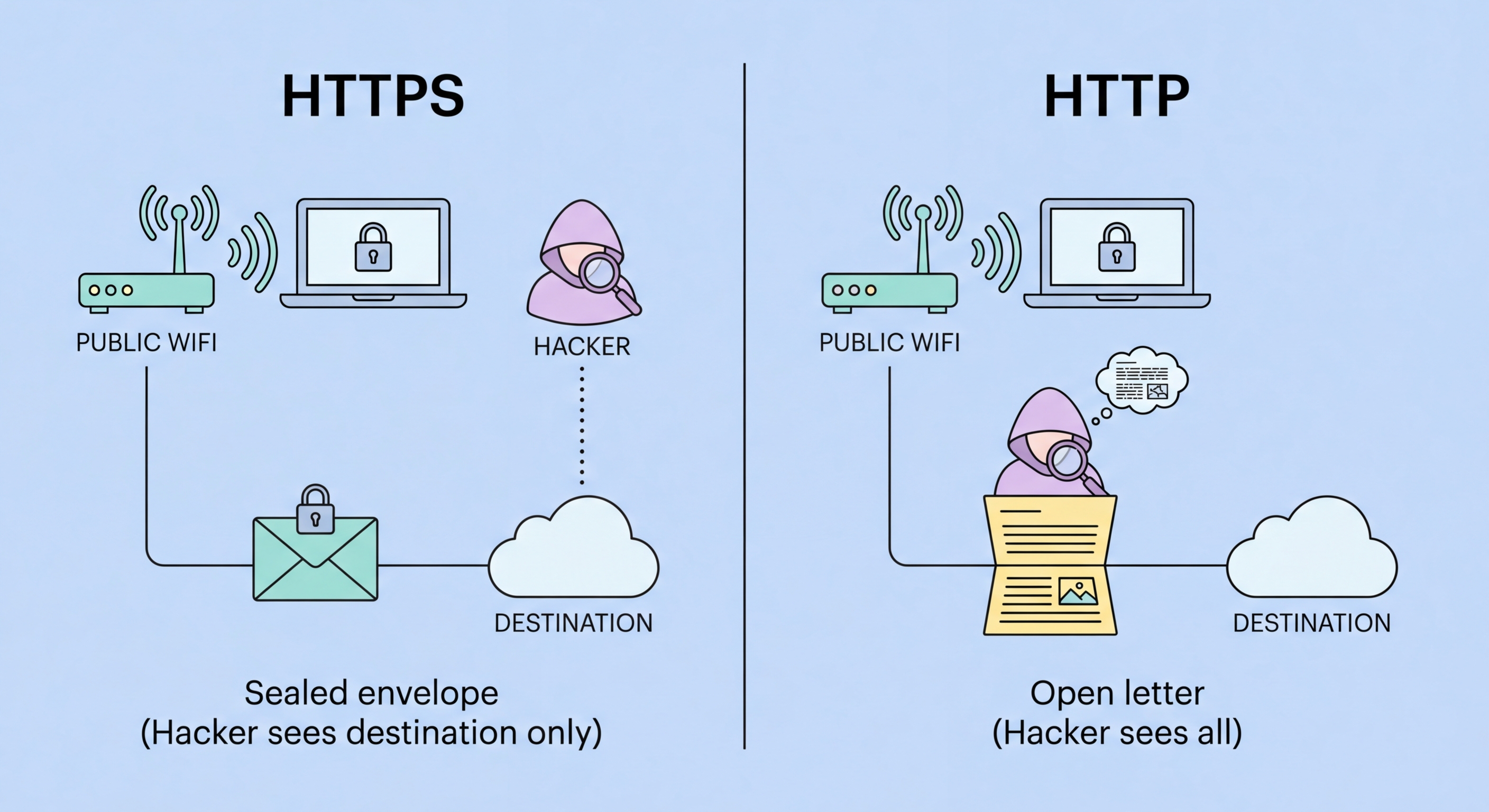
HTTPS has important gaps that leave information visible to network monitors even when all your web traffic uses HTTPS. The most significant gap is DNS. When you type a web address into your browser, your device first sends a DNS query to resolve the domain name (e.g., "hsbc.com.hk") to an IP address. By default, this DNS query is sent in plaintext — unencrypted — over the network. A network monitor on your public WiFi connection can see every DNS query your device sends, which reveals every website you visit, even though the content of your HTTPS sessions is encrypted. This metadata can be quite revealing: DNS queries to banking sites, medical information sites, legal services, or sensitive personal services disclose your activities even without seeing the content.
Traffic metadata is a second gap. Even with HTTPS, an attacker can observe: the IP addresses you connect to (which often map to specific services), the timing and size of data transfers (which can reveal what type of content you are accessing), and how frequently you communicate with specific servers. This metadata analysis, called traffic analysis, is used by sophisticated adversaries to infer user behaviour and identify targets even when content is encrypted. For most users, DNS query visibility is the more practically relevant concern — a network monitor logging your DNS queries builds a detailed picture of your internet activity without needing to decrypt any content.
A VPN addresses both gaps. When a VPN is active, DNS queries are routed through the encrypted VPN tunnel to the VPN provider's DNS servers (or a specified privacy-focused DNS service), making them invisible to the WiFi network. Traffic metadata — IP addresses, timing, and data volumes — is also obscured because all traffic flows through the VPN server before reaching its destination; the network monitor sees only traffic to and from the VPN server, not the actual destinations. Modern VPN apps include DNS leak protection by default, which prevents DNS queries from escaping the VPN tunnel even if the VPN connection drops momentarily. Verify this is enabled in your VPN app's settings: look for "DNS leak protection" or "Private DNS" in the security settings.
- DNS queries: By default, DNS is plaintext — every domain you visit is visible to network monitors
- Traffic metadata: IP addresses, timing, and data volumes visible even with HTTPS content encrypted
- Visited sites: DNS query logs reveal your browsing behaviour even without content decryption
- VPN closes DNS gap: VPN routes DNS through encrypted tunnel — queries hidden from WiFi network
- DNS over HTTPS (DoH): Browser-level DoH encrypts DNS but only for browser traffic — VPN covers all apps
- DNS leak protection: Verify this is enabled in your VPN app settings
What DNS leaks are and how to prevent them on public WiFi →