2Traffic Protection
Practices 4–6: Protecting Your Data in Transit
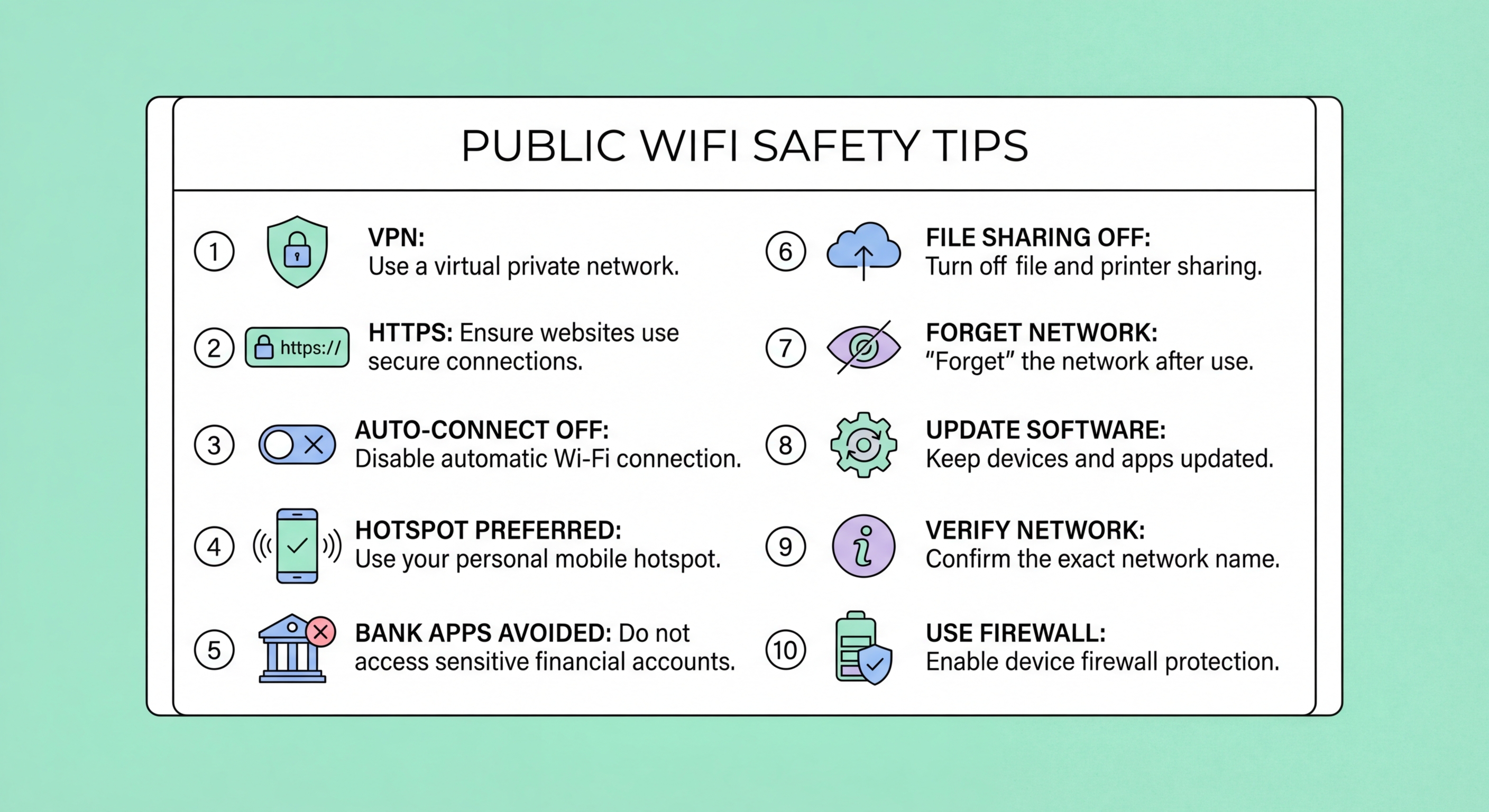
Practice 4: Verify HTTPS on every site you use. HTTPS encrypts the content of your web sessions, making them unreadable to network eavesdroppers even on an open WiFi network. Check the address bar for the padlock icon and "https://" at the start of every URL before entering any credentials or personal information. This is especially important on public WiFi because SSL stripping attacks can downgrade HTTPS to HTTP without obvious warning on some browsers. If a site you regularly access over HTTPS appears without the padlock, or shows an SSL certificate warning, disconnect immediately and switch to mobile data. Installing a browser extension like HTTPS Everywhere (available for Chrome and Firefox) forces HTTPS connections wherever available.
Practice 5: Never submit sensitive information without a VPN. Even on HTTPS-protected sites, the DNS query that resolves the domain name may be unencrypted and visible to network monitors, revealing which sites you visit. Form submissions, login credentials, and personal data should only be transmitted when your traffic is fully protected — meaning a VPN is active. Avoid logging into banking apps, accessing work email, submitting medical information, or making purchases on public WiFi without a VPN. If you must access these services without a VPN, switch to your mobile data connection. for Business Travellers: Protecting Corporate Data in Hong Kong">Hong Kong mobile data plans with 50GB or more monthly allowance make this a practical option throughout the MTR and urban areas where cellular coverage is reliable.
Practice 6: Use your mobile hotspot for high-sensitivity work. When you need to access genuinely sensitive information — company systems, financial accounts, medical records, legal documents — your phone's mobile hotspot is categorically safer than any public WiFi network. Mobile data connections are encrypted at the network level, not accessible to other users in the same location, and not susceptible to evil twin attacks, ARP spoofing, or MITM attacks that affect WiFi. Tether your laptop to your phone's hotspot for sensitive work in hotels, airports, and any location where you are unsure about the WiFi security. The battery and data consumption is modest for short work sessions.
- HTTPS always: Check the padlock before entering credentials or personal information on any site
- SSL warning = disconnect: Any certificate warning on a familiar site warrants immediate disconnection
- VPN for sensitive data: Never submit passwords, financial info, or work data without VPN active
- DNS encryption: VPN encrypts DNS queries that HTTPS alone does not protect
- Mobile hotspot: Use phone's mobile data connection for banking, work systems, and sensitive tasks
- Data allowance: Most HK mobile plans have generous data — switching to mobile data is practical
What HTTPS protects and what it doesn't on public WiFi →