3Complete Protection Setup
The Complete One-Time Setup for Ongoing Public WiFi Protection
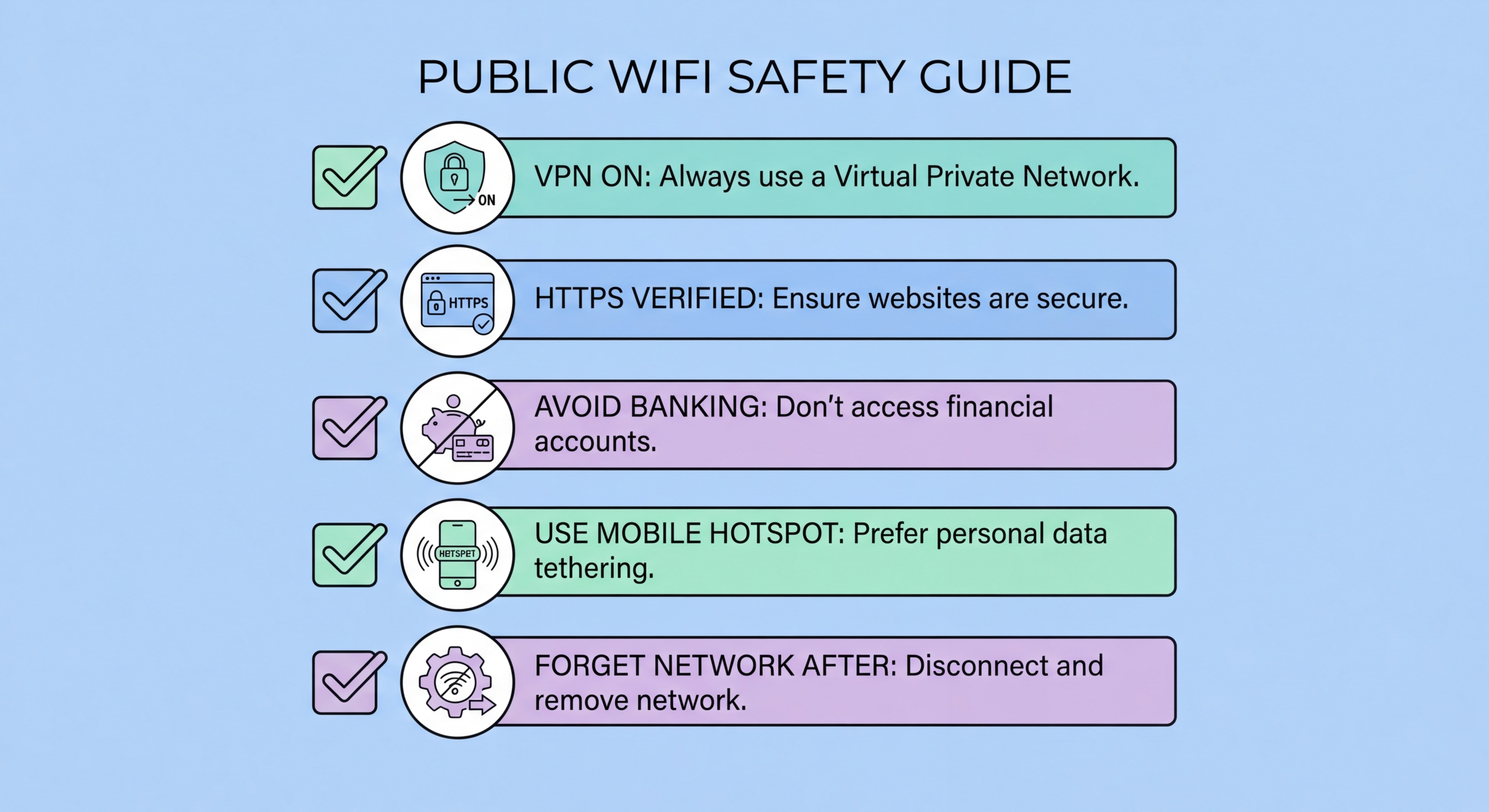
The following setup, completed once, provides ongoing automatic protection on every public WiFi connection without requiring manual action each time. Step 1: Install a quality VPN app (NordVPN, ExpressVPN, Mullvad, or ProtonVPN) and configure auto-connect for all networks except your home and office WiFi. Enable DNS leak protection and the kill switch in the VPN settings. Test with dnsleaktest.com to confirm no DNS leaks. Step 2: On your phone, go through all saved WiFi networks and disable auto-join for every public network (WiFi.HK, past hotel networks, café networks, airport networks). Delete networks from hotels and airports visited more than six months ago. Step 3: On your laptop, verify Windows Defender Firewall or macOS firewall is active. On Windows, ensure the network type is set to "Public" for all public networks. On macOS, enable Stealth Mode and disable all sharing services (File Sharing, Screen Sharing, Remote Login).
Step 4: Enable 2FA on your five highest-value accounts: primary email, banking apps, work Microsoft 365 or Google Workspace account, Apple ID or Google Account, and social media with real name/identity. Use an authenticator app (Google Authenticator, Microsoft Authenticator, or Authy) rather than SMS for these accounts — SMS 2FA is susceptible to SIM swap attacks and is weaker than TOTP-based authenticator apps. Download backup codes for each account and store them securely offline. Step 5: Install a password manager (1Password, Bitwarden, or Dashlane) if you don't already use one, and ensure all accounts you access on public WiFi use unique, strong passwords generated by the password manager. Enable the password manager's phishing protection features that prevent auto-fill on lookalike domains.
Step 6: Establish clear personal rules for sensitive activities. Banking apps: mobile data only, never public WiFi regardless of VPN status. Work email and corporate systems: VPN mandatory, mobile hotspot preferred for any high-sensitivity content. Financial authorisations and approvals: mobile data only. Software updates and installations: only from trusted networks at home or office, never prompted through a public network captive portal. Change passwords for any account after a public WiFi session where you experienced unexpected certificate warnings, unexpected portal requests, or any other suspicious network behaviour. This six-step setup takes approximately twenty minutes and provides layered protection that handles the complete threat surface of Hong Kong's public WiFi environment.
- Step 1: VPN with auto-connect, DNS leak protection, kill switch — test with dnsleaktest.com
- Step 2: Delete and disable auto-join for all public saved WiFi networks on phone and laptop
- Step 3: Firewall active, Windows "Public" network type, macOS Stealth Mode and sharing disabled
- Step 4: 2FA on top 5 accounts using authenticator app (not SMS) — store backup codes offline
- Step 5: Password manager with unique passwords for all public-WiFi-accessed accounts
- Step 6: Personal rules — banking on mobile data, VPN mandatory for work systems, no software installs
Detailed VPN setup guide for Step 1 →