VPN Logging Policies: No-Log VPNs Explained
A VPN's no-logs claim is its most important privacy promise — and the most frequently misrepresented. Here's how to tell genuine no-logs from marketing fiction.
A VPN's no-logs claim is its most important privacy promise — and the most frequently misrepresented. Here's how to tell genuine no-logs from marketing fiction.
VPN logs are records that a VPN provider's servers generate and potentially retain about your VPN usage. The concern is straightforward: when you use a VPN for privacy, the VPN server is the only intermediary that can link your real identity (through your connection to the VPN) with your online activities (through your traffic exiting the VPN server). If those logs are retained and accessible, any privacy benefit of the VPN is contingent on those logs never being exposed — through hacking, legal compulsion, or the provider's own data use.
The VPN industry's "no-logs" marketing has unfortunately become so widespread that it now appears on services ranging from genuinely privacy-respecting providers to apps that log extensively. The term itself is not standardised — different providers define "no logs" to mean radically different things. Some providers who claim "no logs" still collect connection timestamps, bandwidth usage data, IP addresses of connecting devices, and session duration information — data that, while not revealing the specific content of your browsing, can be used to link your VPN usage to your identity and specific time windows of activity.
The stakes are illustrated by real-world cases. IPVanish claimed a no-logs policy but cooperated with a 2016 US law enforcement investigation by providing connection logs — demonstrating that unverified claims offer no real protection. PureVPN similarly claimed no logs but provided data to the FBI in 2017. These cases reveal that a no-logs claim without independent verification is simply a marketing statement that you're betting your privacy on.
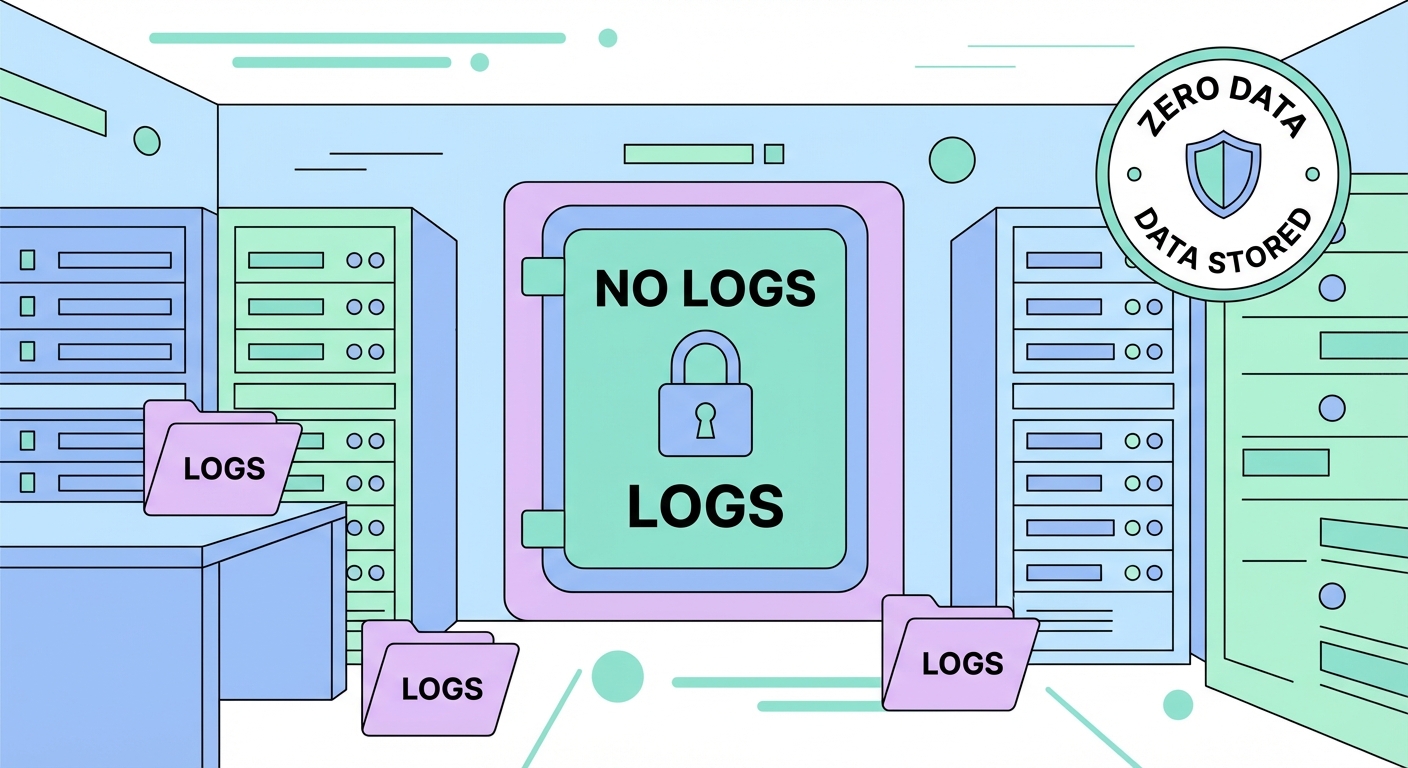
Understanding the difference between types of VPN logs helps you evaluate provider claims accurately. Activity logs are the most sensitive category — they record the specific websites you visit, your DNS queries, your search terms, and the content of unencrypted communications passing through the VPN server. Any VPN claiming a no-logs policy should unequivocally not retain activity logs. No reputable provider maintains these for consumer VPN services.
Connection logs (also called metadata logs) are more nuanced. These record technical data about your VPN sessions: your real IP address when you connected, the VPN server IP you connected to, the timestamps of your connection and disconnection, and the total data volume of your session. Individually, each piece seems innocuous. Together, they can powerfully re-identify you: if an adversary knows you're suspected of an online activity that occurred at 14:32–15:47 on a specific date, connection logs showing you were connected to that VPN server during exactly that window link you to the activity, even without direct content logs.
The minimal-logging approach taken by privacy-focused providers retains only what's operationally necessary. Some providers retain only your subscription information (email, payment data) and the VPN IP address assigned to your current session (to enforce device limits) — and even this is volatile, not permanently stored. The gold standard is zero persistent storage: WireGuard's connection state is stored in RAM, is never written to disk, and is lost when the session ends or the server is restarted.
Independent security audits are the most reliable mechanism for verifying a VPN's no-logs claims. A comprehensive audit involves cybersecurity professionals — typically from firms like Cure53 (Germany), PricewaterhouseCoopers AG (Switzerland), Deloitte, or KPMG — reviewing the VPN provider's servers, source code, and internal policies to verify that no logging is occurring. Auditors can examine server configurations, running processes, log files (or their absence), and data retention policies against the provider's published claims.
Key audited no-logs VPNs as of 2026: ExpressVPN has been audited by Cure53, KPMG, and PwC; its TrustedServer RAM-only architecture was independently verified. NordVPN completed its first no-logs audit with PwC in 2018 and has conducted multiple audits since. Mullvad has been audited by Cure53. ProtonVPN has open-sourced all its client applications and has undergone independent audits. The most trustworthy approach is to look for providers who publish their full audit reports publicly — not just a summary or a badge claiming "audited."
Real-world server seizures are the ultimate test. ExpressVPN's servers were seized by Turkish authorities in 2017 during the investigation of the assassination of Russian ambassador Andrei Karlov — investigators found no user data because the servers used RAM-only infrastructure. NordVPN's server in Finland was breached in 2018; the attacker found no user data because of the no-logs policy. These real-world events, while concerning from a security perspective, actually demonstrated that the no-logs policies were genuinely implemented rather than just claimed.
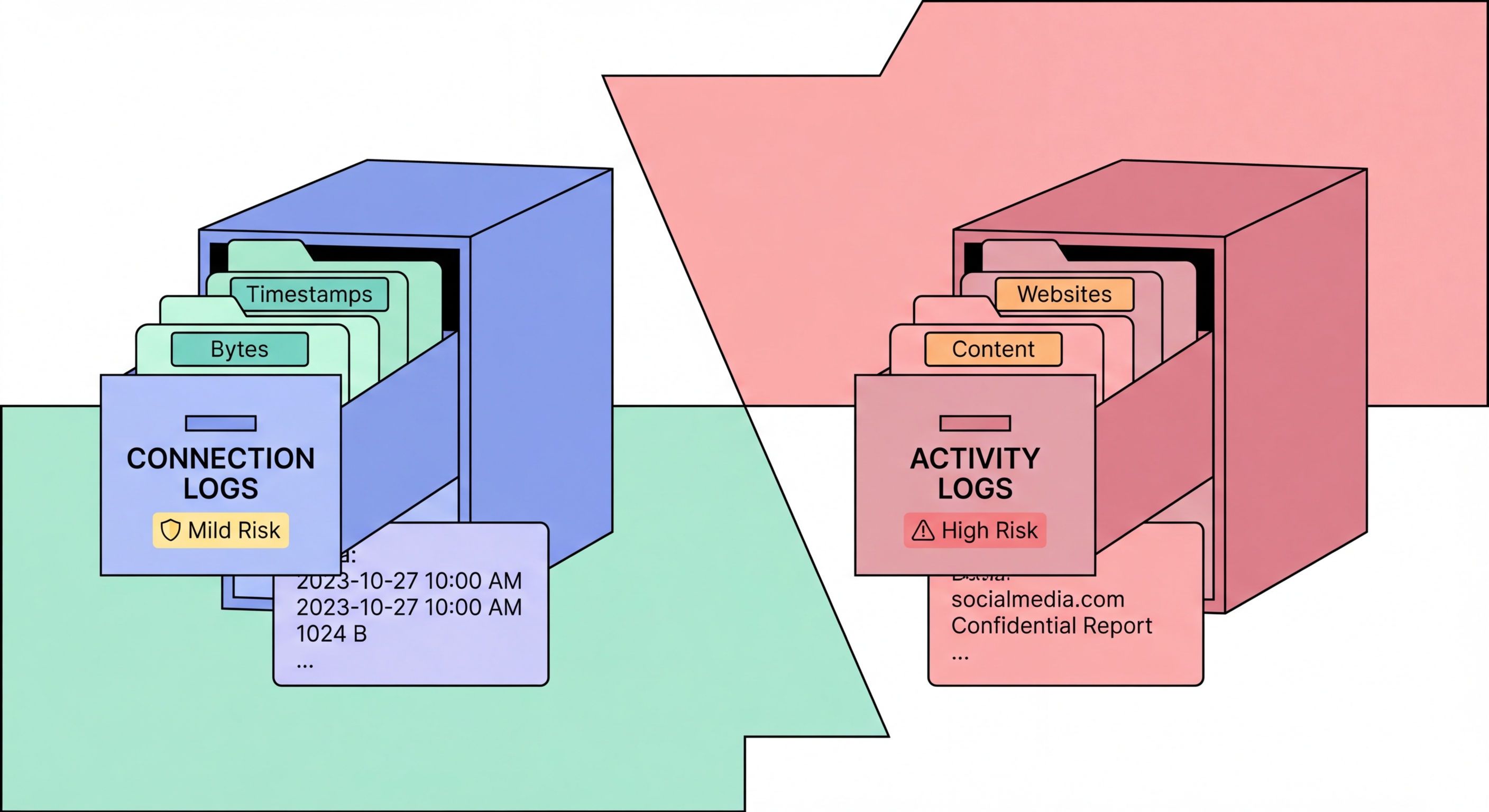
The intelligence-sharing alliances known as Five Eyes, Nine Eyes, and Fourteen Eyes represent formal arrangements for sharing signals intelligence between member countries' intelligence agencies. The Five Eyes alliance (FVEY) — US, UK, Canada, Australia, New Zealand — shares intelligence under the UKUSA Agreement, originally established during World War II and formalised in the Cold War era. Member country intelligence agencies routinely share collected communications data, and in some cases have cooperated to circumvent domestic surveillance restrictions by having allied agencies collect data on their own citizens.
For VPN users, jurisdiction in a Five Eyes country means the VPN provider is subject to the laws of that country, including potential National Security Letters (US) or similar secret data demands that come with gag orders preventing disclosure to users. An NSL can compel a US VPN provider to collect and surrender user data secretly — with no ability to inform users or even publicly acknowledge the order. This is why privacy advocates generally recommend VPN providers headquartered outside Five Eyes jurisdiction. The Nine Eyes extends this to France, Netherlands, Denmark, and Norway; the Fourteen Eyes further adds Germany, Belgium, Italy, Sweden, and Spain.
In practice, jurisdiction is one factor among several — not an absolute determinant of trustworthiness. A VPN in Panama with poor security practices and no audit history is less trustworthy than a VPN in the US with a proven no-logs policy, multiple independent audits, RAM-only infrastructure, and a track record of resisting legal requests. Switzerland (ProtonVPN) has particularly strong privacy laws that limit data disclosure to Swiss court orders — a meaningful advantage over Five Eyes jurisdictions. The British Virgin Islands (ExpressVPN, Surfshark) has no data retention requirements and no intelligence-sharing treaties with major powers.