1Core Psychological Triggers
The Core Psychological Triggers Exploited by Social Engineering
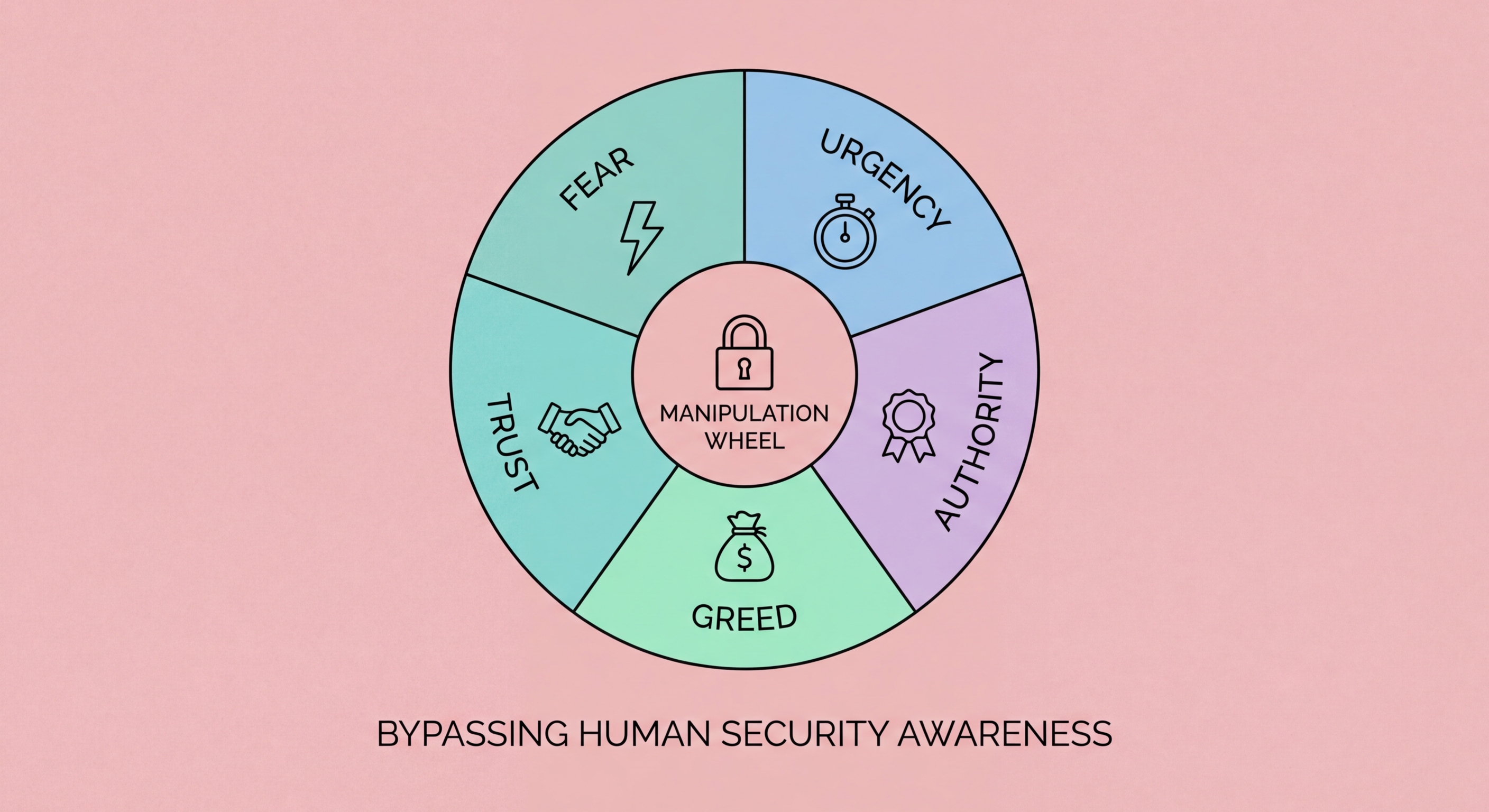
Social engineering attacks exploit documented psychological principles rather than technical vulnerabilities. Robert Cialdini's research on influence identified six principles — authority, social proof, scarcity, reciprocity, commitment, and liking — that reliably influence human decision-making in ways that can be exploited by attackers. Phishing campaigns are not random: they are designed around specific psychological triggers that are known to drive compliance before careful reflection can intervene. Understanding which triggers are being activated in a message is a more reliable detection method than looking for technical red flags, because the psychological manipulation is the invariant element even when all technical indicators are obscured.
Authority is the most frequently exploited trigger in phishing. People are conditioned to comply with apparent authority figures — government officials, police, senior managers, financial institutions — even when the request is unusual. The HKPF conducts thousands of cases annually where victims transferred large sums to apparent "mainland police" or "ICAC investigators" specifically because the authority framing bypassed their normal scepticism. Authority bias is particularly strong in Hong Kong's cultural context, where deference to institutional authority and hierarchical seniority is well-established. Scammers exploit this consciously, framing messages with official language, case numbers, and institutional branding to trigger compliance before the victim has time to question the legitimacy of the source.
Urgency and scarcity work by narrowing the decision-making window. "Your account will be closed in 24 hours", "this offer expires tonight", "act now to prevent arrest" — these formulations are not accidental. Under time pressure, people rely on heuristic shortcuts rather than deliberate analysis, making them more susceptible to manipulation. The urgency is almost always artificial: genuine financial institutions do not close accounts within hours of an email notification, and genuine law enforcement does not arrest people because they failed to respond to a phone call quickly enough. Recognising urgency as a manipulation technique — rather than as evidence that the situation is genuinely urgent — is one of the most valuable phishing-resistance habits to develop.
- Authority bias: Compliance with apparent authority figures — police, government, senior management — before questioning legitimacy
- Urgency manipulation: Artificially compressed decision window prevents careful analysis — "act now or lose access"
- Scarcity framing: "Last chance", "expires tonight" — drives action before reflection by simulating scarcity
- HK cultural context: Deference to institutional authority makes authority-based phishing particularly effective in HK
- Heuristic reliance: Time pressure forces reliance on mental shortcuts rather than deliberate reasoning
- Recognise the trigger: Noticing "I feel urgency right now" is itself a signal to slow down, not speed up
How authority bias powers vishing calls in Hong Kong →