2What to Report and Preserve
What Information to Gather Before Reporting Phishing
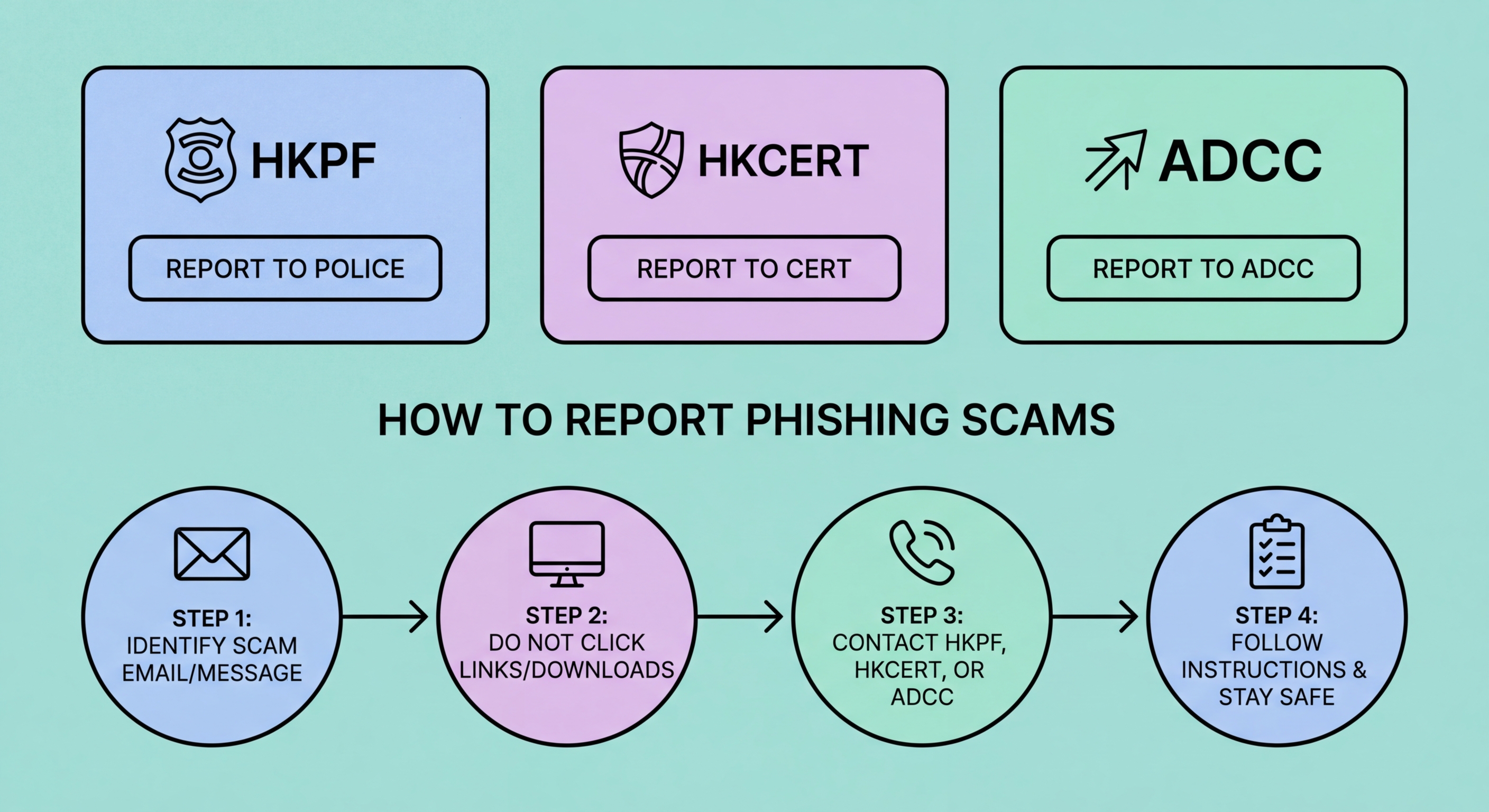
Effective phishing reporting requires preserving evidence before it disappears. Phishing websites are often taken down quickly — either by the attacker to avoid detection or by hosting providers acting on abuse reports — so screenshotting the fraudulent site and noting the full URL is important. For phishing emails, forward the original message including full email headers to HKCERT and to your email provider's abuse address — headers reveal the true sending infrastructure and are critical for technical investigation. Do not just forward the message body; the headers require accessing the "view source" or "show original" option in your email client.
For financial fraud, document all transaction details: the date and time of any transfers, the recipient account number and bank, the amount, the reference used, and any confirmation numbers. If the fraud involved a fraudulent website, preserve the URL and screenshots of any pages where you entered information. If it involved a phone call, note the number displayed (even knowing it may be spoofed), the time of the call, the language used, any case numbers or names mentioned, and the demands made. This documentation serves both the formal police report and any subsequent civil recovery action, and is required for insurance claims under cyber insurance policies.
For SMS phishing (smishing), forward the fraudulent SMS to your mobile carrier's spam reporting service before deleting it — PCCW/HKT, CSL, and SmarTone all provide SMS spam reporting channels. For WhatsApp scams, report the message within the app using the Report function (long-press the message → Report) and also take screenshots before doing so, as reporting may result in the message being removed from your view. For social media scams, use the platform's reporting mechanism for fraudulent accounts or posts in addition to formal reporting to HKPF — platform takedowns are often faster than formal investigation processes.
- Screenshot phishing sites immediately: Sites are taken down quickly — capture full URL and page content before it disappears
- Forward with full email headers: "Show original" in Gmail/Outlook — headers reveal true sending infrastructure
- Transaction documentation: All transfer details including recipient account, amount, date, time, and reference
- Phone call notes: Displayed number, time, case numbers, demands — even spoofed number has intelligence value
- SMS forwarding: Forward fraudulent SMS to carrier spam number before deleting
- Platform reporting: WhatsApp, Facebook, Instagram, LinkedIn — platform takedowns complement formal reporting
How to identify and document phishing evidence →