2Accessing Headers
How to View Full Email Headers in Gmail, Outlook, and Apple Mail
In Gmail on desktop, open the suspicious email and click the three-dot menu (More) in the top right corner of the message. Select "Show original" from the dropdown. This opens a new tab displaying the complete raw message including all headers. Gmail also provides a "Copy to clipboard" button on this page, and the view includes a summary at the top showing the SPF, DKIM, and DMARC results clearly highlighted — "PASS" in green or "FAIL" in red. This summary view is the quickest way to check authentication results in Gmail without reading the raw headers manually. Alternatively, use the "Message Header Analyzer" tool at toolbox.googleapps.com — paste the raw headers and receive a structured breakdown.
In Outlook on desktop (Windows), open the email and click "File" in the ribbon, then "Properties". The Internet headers are displayed in a text box at the bottom of the Properties window. In Outlook on the web (OWA), open the message, click the three-dot menu (More actions), and select "View message source" or "View message details" depending on your OWA version. In Apple Mail on macOS, open the message and select View → Message → All Headers from the menu bar. On iPhone or iPad, Apple Mail does not provide native header access — use a third-party email client like Outlook for iOS or access the message via webmail on a desktop browser where headers are accessible through the provider's interface.
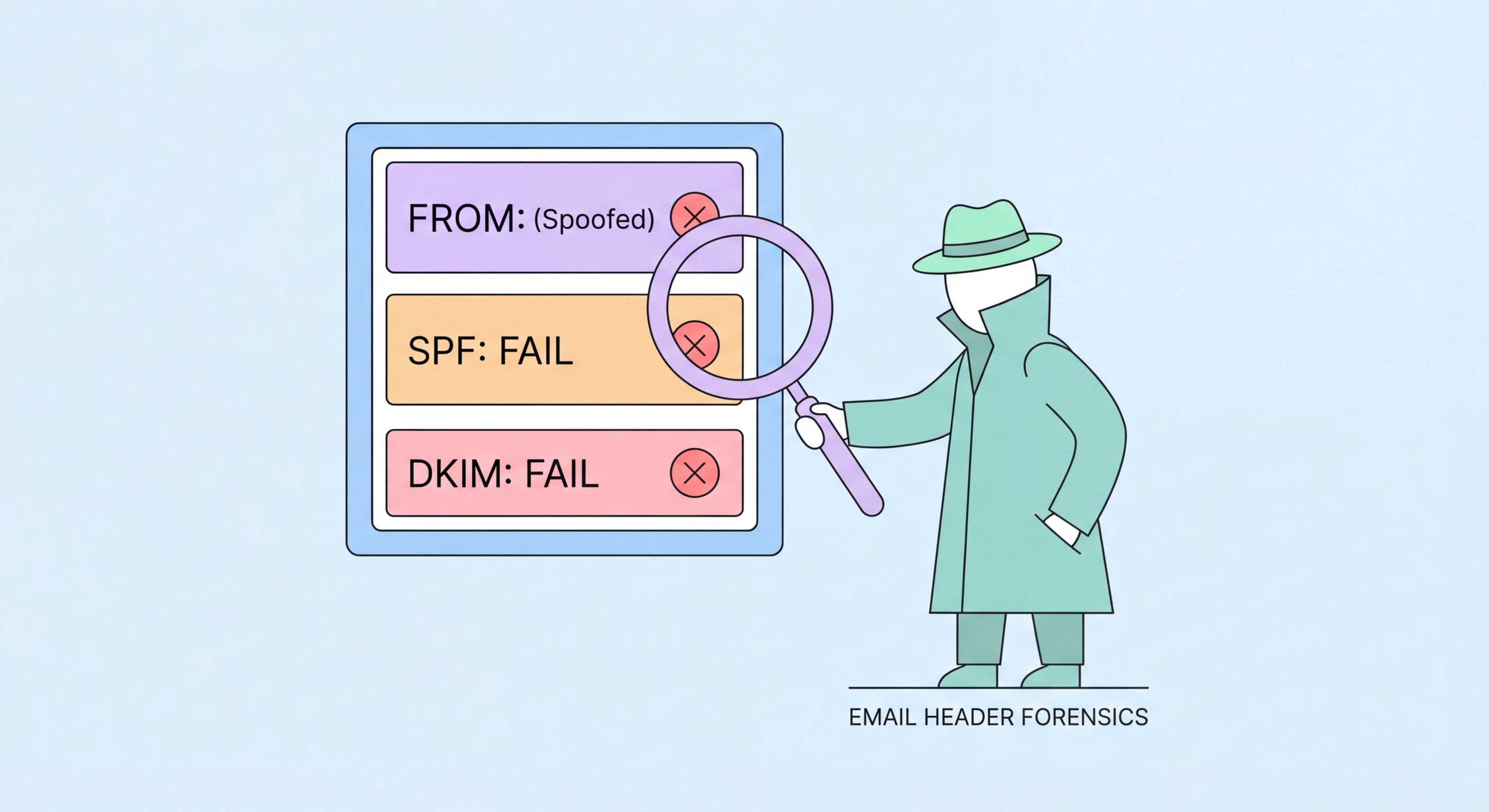
Once you have the raw headers, the key fields to examine are: "From:" (the claimed sender), "Return-Path:" (where delivery failure notices go — should match or be closely related to From domain for legitimate email), "Received:" headers (the chain of servers the message transited — read from bottom to top, the bottommost is the originating server), and "Authentication-Results:" (the SPF, DKIM, and DMARC results). For a message claiming to be from HSBC, the Received headers should show hsbc.com servers, and the Authentication-Results should show SPF=pass and DKIM=pass for the hsbc.com domain. Any discrepancy — a Received header from a random IP, an SPF fail, a DKIM fail — confirms the email is not genuinely from HSBC.
- Gmail: Three-dot menu → "Show original" — includes visual SPF/DKIM/DMARC pass/fail summary
- Outlook desktop: File → Properties → Internet headers text box
- Outlook web: Three-dot menu → "View message source" or "View message details"
- Apple Mail macOS: View → Message → All Headers
- Google Header Analyzer: toolbox.googleapps.com — paste raw headers for structured breakdown
- Key fields: From, Return-Path, Received (bottom to top), Authentication-Results
How to assess phishing risk before accessing headers →