1What Is Spear Phishing
What Makes Spear Phishing Different from Mass Phishing
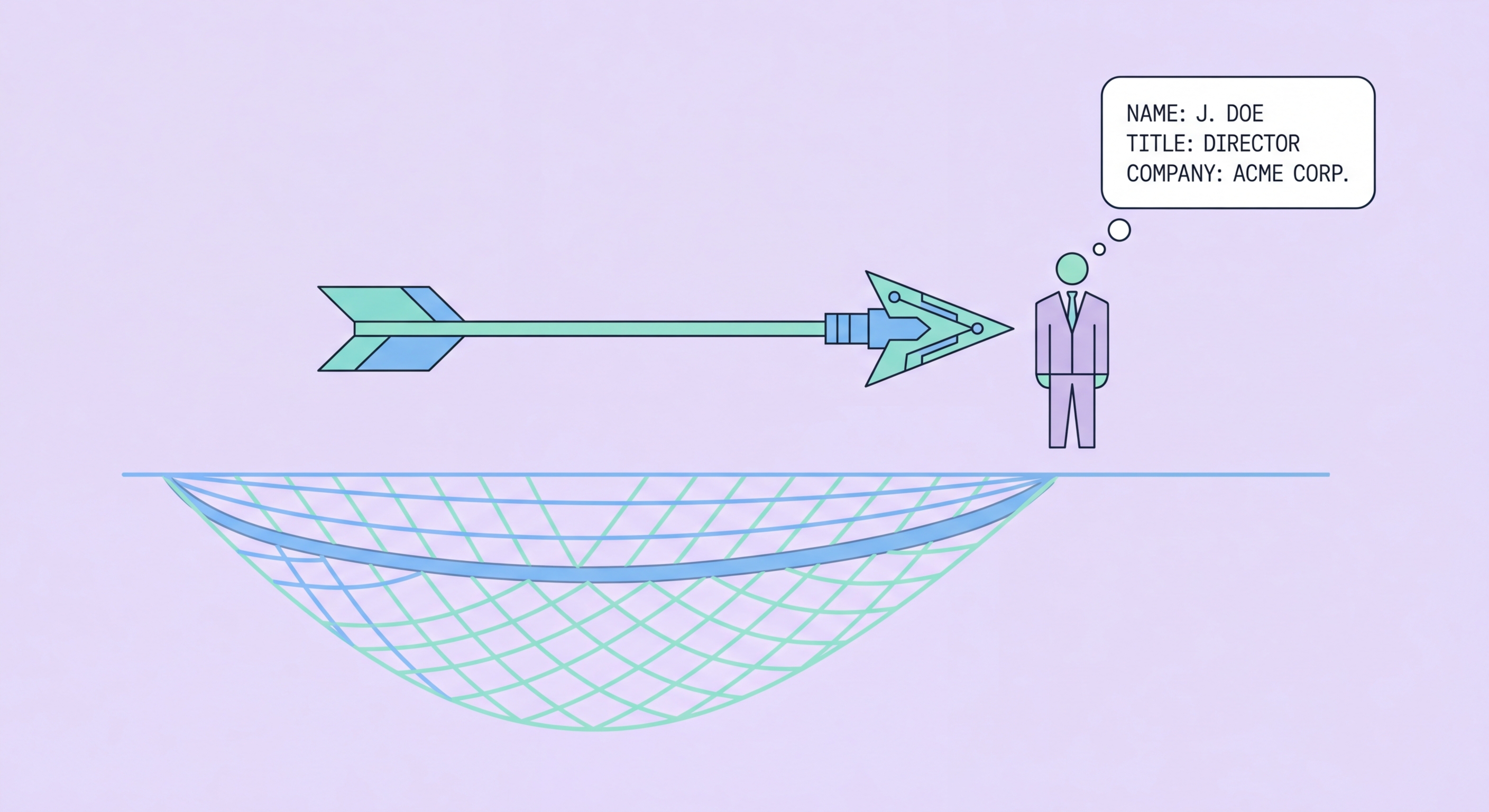
Mass phishing casts the widest possible net — millions of identical or near-identical messages, sent to harvested email addresses, hoping a small percentage will respond. Spear phishing is the opposite approach: a single message, carefully crafted for a specific individual, using personal details that would not appear in a generic phishing email. While mass phishing relies on scale, spear phishing relies on precision — and precision dramatically increases the probability that the target will believe the message is legitimate and act on it without scrutiny.
The research phase of a spear phishing attack can be extensive. Attackers compile information from LinkedIn (job title, employer, colleagues' names, professional history), company websites (organisational structure, publicly listed contact details, recent announcements), social media (personal interests, recent activities, family details, location), and data breach databases (email addresses, previous passwords, partial financial information). This intelligence is used to craft a message that references specific, accurate details about the target's professional and personal context — creating the impression that the sender genuinely knows the target and has a legitimate relationship with them.
The success rate of spear phishing is significantly higher than mass phishing. Security research consistently shows that personalised phishing messages achieve click-through rates several times higher than generic equivalents. The FBI's Internet Crime Complaint Center identifies spear phishing and its business variant (Hong Kong: Prevention Guide">Business Email Compromise) as the highest-value cybercrime category by financial loss globally. In Hong Kong, the HKPF Cyber Security and Technology Crime Bureau consistently reports spear phishing and BEC among the highest-value business fraud categories, with losses concentrated in finance, professional services, and real estate sectors where large-value transactions are routine.
- Targeted approach: One specific message for one specific individual — opposite of mass phishing's scatter approach
- Research-driven: LinkedIn, company website, social media, breach data used to personalise the attack
- Higher success rate: Personalised messages achieve much higher click rates than generic phishing
- Higher value targets: Executives, finance controllers, IT administrators — those with access to assets or systems
- HK sector exposure: Finance, professional services, real estate — high-value transaction environments
- BEC relationship: Business Email Compromise is spear phishing applied specifically to financial fraud in business contexts
How spear phishing fits into the broader phishing landscape →