4Universal Best Practices
Universal Social Media Security Practices for Mobile
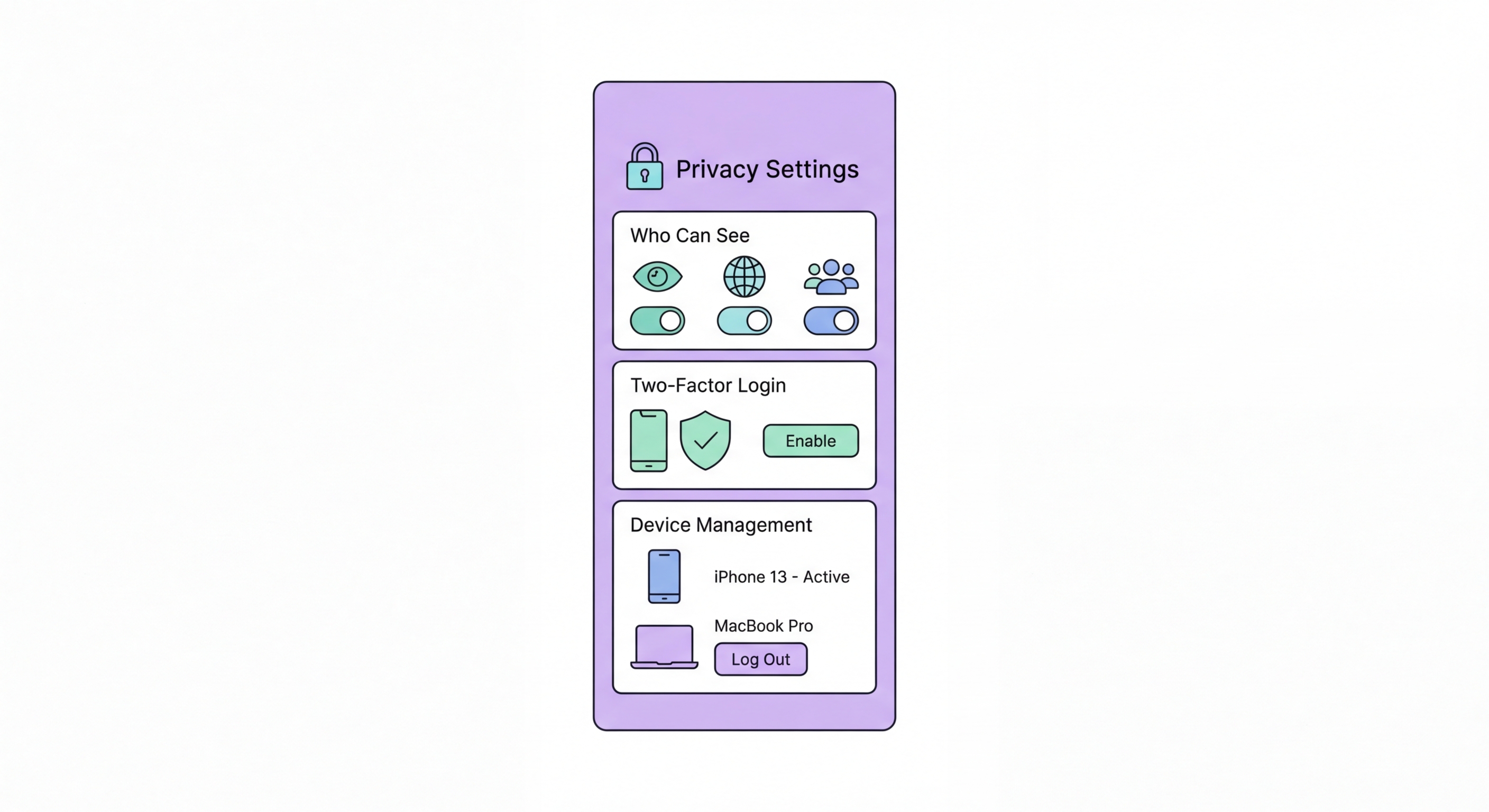
Beyond platform-specific settings, several security practices apply across all social media platforms and are particularly important for mobile users. Strong, unique passwords combined with authenticator app two-factor authentication are the foundation of social media account security. Social media account takeovers — where attackers hijack accounts to run scams, spread malware, or harass the account owner's contacts — are extremely common. An account protected by a strong unique password and TOTP 2FA is dramatically more resistant to takeover than one protected by a reused password and SMS 2FA.
Review what you share on social media from a social engineering risk perspective. Your social media posts collectively create a detailed profile that attackers can use to craft targeted phishing messages, password reset questions, and impersonation attacks. Posts revealing your home neighbourhood, workplace, regular schedule, upcoming travel, pets' names, family members' names, and vehicle details provide material for social engineering. This doesn't mean you must avoid posting about your life — but being mindful of high-value social engineering data (mother's maiden name, childhood pet, first school — common password reset questions) is sensible.
App permissions for social media on mobile should be reviewed and restricted. The most important permissions to deny or restrict: Location (deny precise location; use approximate only while using the app); Contacts (deny entirely unless using contacts for friend finding — this prevents your contacts from being uploaded to the platform); Microphone (grant only when actively recording audio content); Camera (grant only while using the app). On iOS, the App Privacy Report shows you exactly when Instagram, TikTok, and other social apps access your microphone and camera — review this after enabling it in Settings → Privacy & Security.
- Unique passwords per platform: Use a password manager (1Password, Bitwarden, or Apple Keychain) to generate and store unique strong passwords for every social media account.
- Authenticator app 2FA on all platforms: Every major social platform supports TOTP 2FA — enable it on all accounts, starting with your primary professional and personal accounts.
- Review app permissions quarterly: Check which social apps have access to your location, camera, microphone, and contacts in device Privacy settings — revoke what isn't needed.
- Mind what you share: Be aware of social engineering data in your posts — details that could be used to answer security questions, guess passwords, or craft targeted phishing.
- Third-party app access: Go to each platform's settings and review connected apps ("Login with Facebook/Google" connections) — revoke access from apps you no longer use.
- Monitor active sessions: All major social platforms show where you're logged in — review monthly and immediately revoke any unrecognised sessions.
Set up authenticator app 2FA on all your accounts →