1What MDM Does
What Mobile Device Management Gives Your Business
Mobile Device Management (MDM) is a technology platform that allows IT departments to centrally manage, configure, monitor, and secure all mobile devices used within an organisation. For to Do If Your Phone Is Lost or Stolen in Hong Kong">Hong Kong businesses — where employees routinely use smartphones to access corporate email, customer data, financial systems, and internal applications — MDM transforms an uncontrolled security liability into a managed, auditable asset. A lost or stolen employee phone can result in a reportable data breach under Hong Kong's Privacy (Personal Data) Ordinance; with MDM, the response takes minutes rather than days.
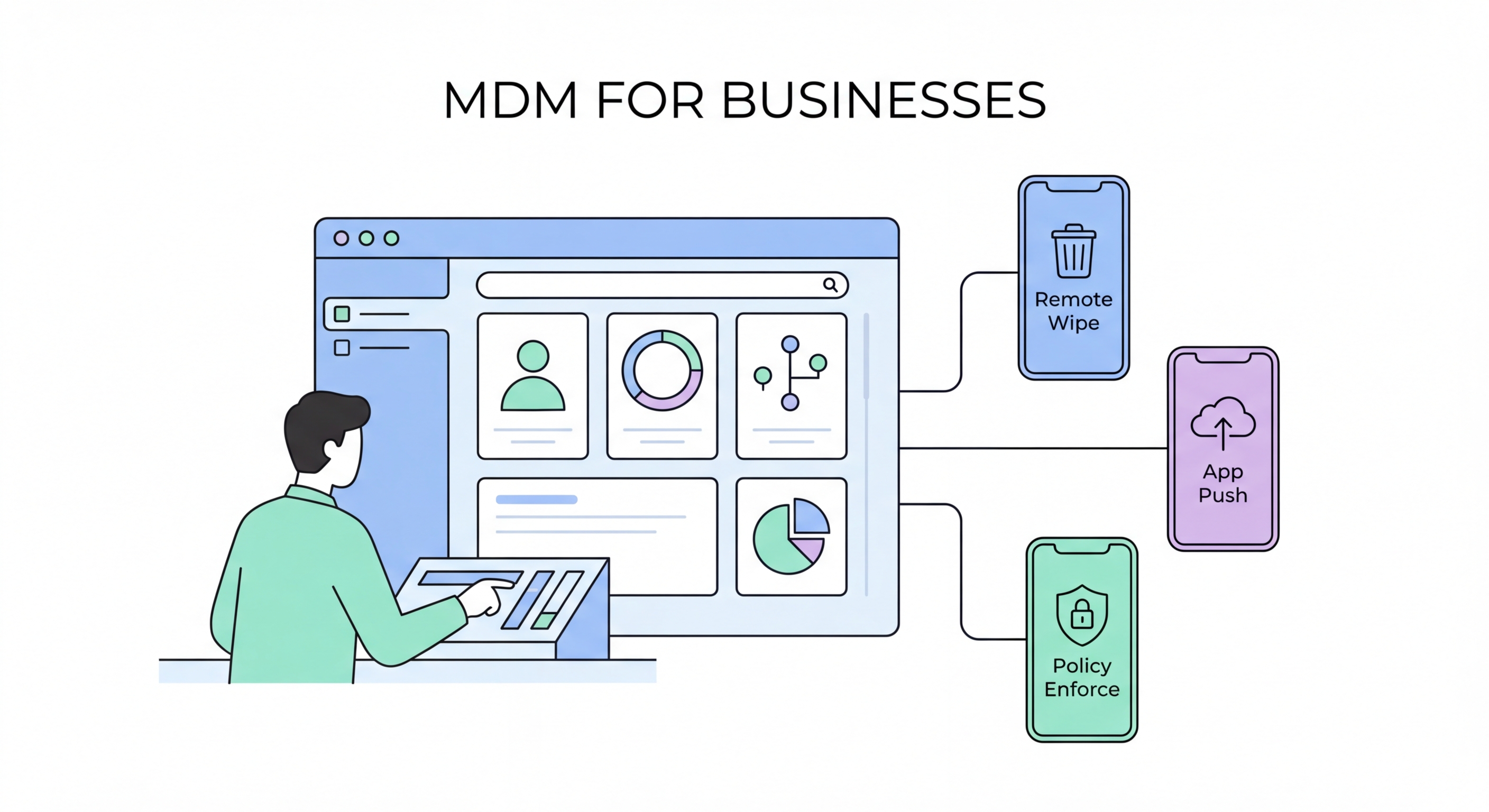
The core capabilities of an MDM platform include: device enrolment and inventory (knowing exactly which devices exist in your fleet); configuration enforcement (ensuring every device has minimum security standards — passcode complexity, encryption, VPN, etc.); app management (deploying, updating, and removing apps without user action); and remote actions (locking or wiping a lost device from a central console). Enterprise-grade MDM solutions also support conditional access — blocking a device from accessing corporate email or systems if it falls below security compliance requirements.
For Hong Kong financial services firms, law firms, healthcare providers, and other regulated industries, MDM is increasingly mandatory rather than optional. The Hong Kong Monetary Authority (HKMA) Cybersecurity Fortification Initiative 2.0 and various industry circulars explicitly address mobile device management as a control requirement. Having an MDM solution deployed not only improves security posture but also demonstrates regulatory compliance when subject to audit or examination.
- Centralised device inventory: Real-time visibility into every mobile device accessing corporate resources — make, model, OS version, compliance status.
- Policy enforcement: Automatically enforce minimum security standards — encryption, passcode complexity, OS update requirements, app whitelisting/blacklisting.
- Remote wipe: Instantly erase all corporate data from a lost or stolen device — or perform a full factory reset — from a central management console.
- App management: Push apps to devices silently, update them centrally, and remove them without user action — including when an employee leaves the company.
- Conditional access: Block non-compliant devices from accessing corporate email, SharePoint, Salesforce, and other systems until they meet security requirements.
- Regulatory compliance: MDM deployment supports HKMA CFI 2.0, PDPO data breach prevention obligations, and international standards including ISO 27001.
Android security settings for business users →