How to Secure Your Smartphone: A Complete Guide
A step-by-step security hardening guide for iPhone and Android users in Hong Kong — from lock screen settings and app permissions to encrypted backups and VPN configuration.
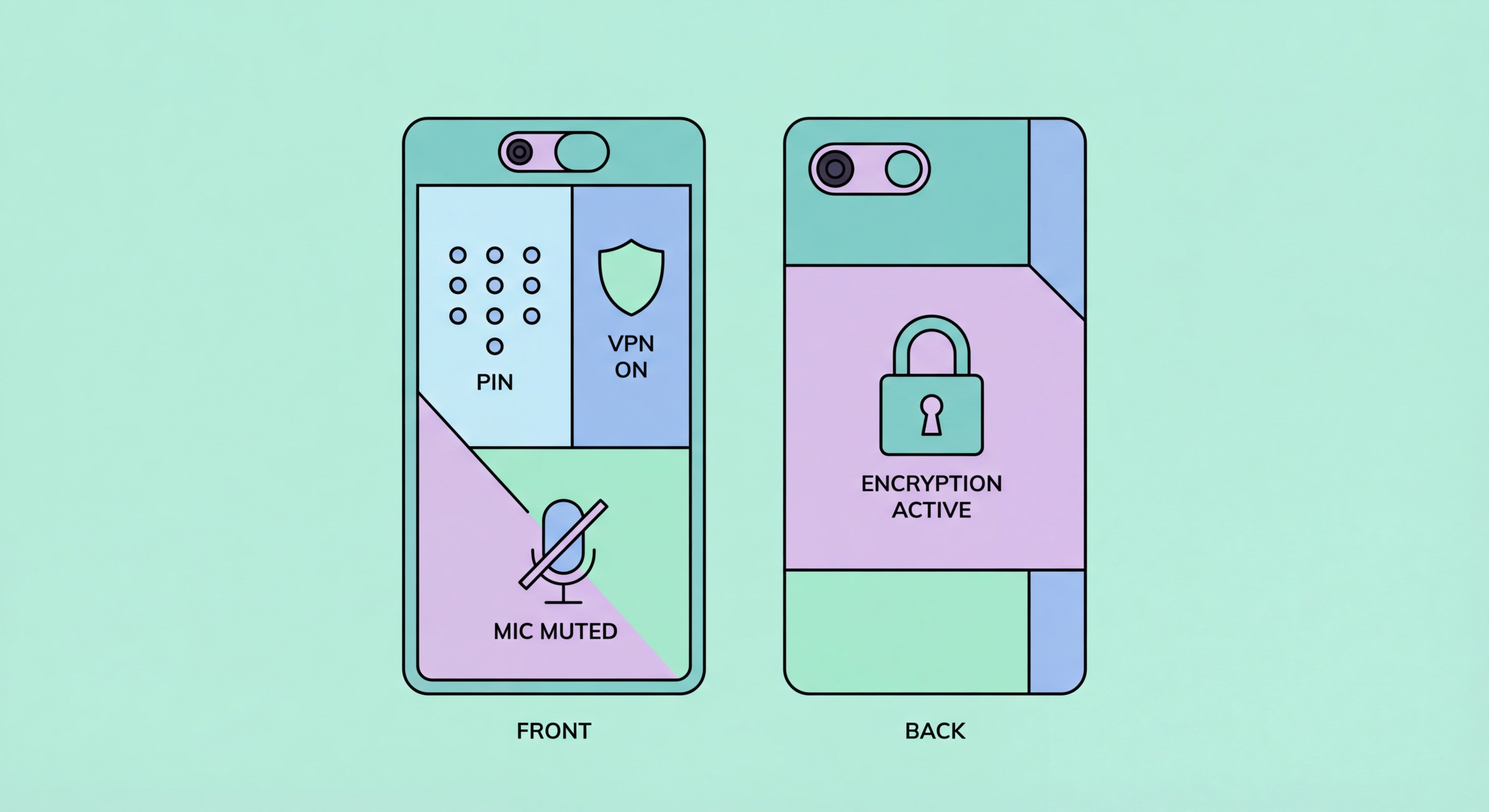
A step-by-step security hardening guide for iPhone and Android users in Hong Kong — from lock screen settings and app permissions to encrypted backups and VPN configuration.
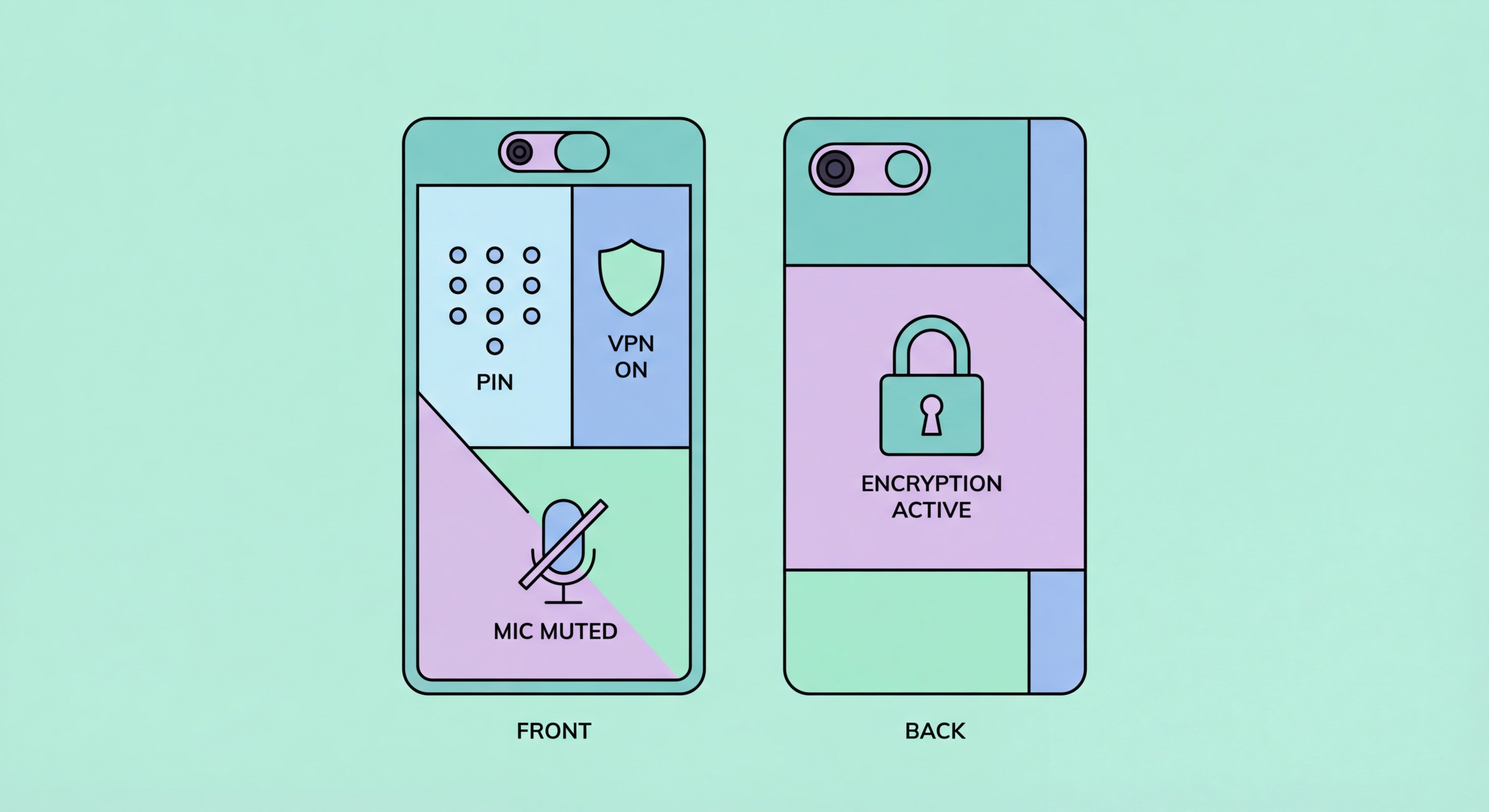
Your lock screen is the first barrier between a thief or snoop and everything on How to Spot and Avoid Attacks on Your Phone">your phone. A weak lock screen — a 4-digit PIN, a simple swipe pattern, or no lock at all — means that physical access to your device is sufficient to access all your data, including banking apps, messages, and stored passwords. Strengthening your lock screen is the single highest-impact security action you can take.
On iPhone, go to Settings → Face ID & Passcode (or Touch ID & Passcode) and change your passcode to an alphanumeric custom code of at least 8 characters. Disable Simple Passcode to unlock this option. Set "Require Passcode" to immediately — this ensures the passcode is required the moment the screen locks rather than after a grace period. On Android, go to Settings → Security → Screen Lock and choose "Password" rather than PIN or pattern, then configure your lock timer to 30 seconds or less.
Biometric authentication (Face ID, fingerprint) adds convenience without sacrificing security when configured correctly. Use biometrics as a secondary method that unlocks with your passcode as the underlying credential. Be aware that in to Do If Your Phone Is Lost or Stolen in Hong Kong">Hong Kong, as in most jurisdictions, law enforcement can potentially compel you to unlock a device with your face or fingerprint, but cannot compel you to reveal a passcode — this is relevant for users with elevated privacy concerns.

The majority of successful mobile attacks exploit known vulnerabilities that have already been patched in available updates. Users who delay or ignore updates are running known-vulnerable software that attackers actively target. Enabling automatic updates for both your operating system and installed apps is the simplest and most effective way to eliminate this entire category of risk.
On iPhone, enable automatic updates at Settings → General → Software Update → Automatic Updates. Turn on both "Download iOS Updates" and "Install iOS Updates" to ensure updates are installed overnight without any manual intervention. For apps, go to the App Store → Account → Settings and enable Automatic Downloads for App Updates. On Android, go to Settings → System → System Updates (varies by manufacturer) for OS updates, and enable automatic updates in the Play Store settings.
App auditing is a complementary practice. Over time, most users accumulate apps they no longer use — each one representing a potential vulnerability if it contains unpatched security flaws, and a surveillance risk if it retains permissions it was granted years ago. Schedule a quarterly review: open your app library, identify apps you haven't used in 30 days, and delete them. For apps you keep, review their permissions and revoke any that seem excessive for the app's function.

Network security on a smartphone encompasses your WiFi habits, VPN usage, Bluetooth configuration, and how you handle mobile data. Each of these represents a potential attack surface that, with modest configuration changes, can be significantly hardened. The most impactful single change most Hong Kong users can make to their network security is installing and using a reputable VPN on their mobile device.
For WiFi security, the key practices are: avoiding public WiFi without VPN protection; disabling auto-join for open networks; forgetting networks you no longer use (which prevents your phone from broadcasting probe requests that reveal your location history); and reviewing the list of saved WiFi networks periodically. On iPhone, go to Settings → WiFi and review your saved networks, removing any that are no longer needed. Disable "Ask to Join Networks" to prevent automatic prompts to connect to unknown networks.
Bluetooth is another often-overlooked attack surface. Classic Bluetooth vulnerabilities — including BLUEBUGGING and KNOB attacks — can allow nearby attackers to eavesdrop on or take control of Bluetooth-connected devices. Keep Bluetooth disabled when not actively using it. On both iOS and Android, never pair with unknown Bluetooth devices in public. Be particularly cautious about Bluetooth-connected headphones and speakers in public places — these can be vectors for audio interception.

A smartphone security strategy is incomplete without addressing what happens when the worst occurs: a lost or stolen device, a ransomware infection, or a catastrophic hardware failure. Regular, encrypted backups — combined with remote wipe capability — ensure that you can recover your data and deny it to adversaries regardless of what happens to the physical device.
iCloud Backup on iOS and Google One Backup on Android both provide automatic cloud backup of your device's content, apps, and settings. iCloud backups are end-to-end encrypted when "Advanced Data Protection" is enabled (iOS 16.2 and later) — this option should be enabled by every security-conscious iPhone user. It applies end-to-end encryption to iCloud Backup, Photos, Notes, and 20+ additional data categories, meaning Apple cannot access your backup data even under legal compulsion.
Enabling Find My iPhone (iOS) or Find My Device (Android) is essential for two reasons: it allows you to locate a misplaced device, and — critically — it allows you to remotely erase the device's contents if it's stolen. Test this capability before you need it: log into iCloud.com or Google's Find My Device portal and confirm your device appears and is reachable. Keep your Apple ID or Google account credentials in a secure password manager, as these are your keys to remote wipe functionality.
