3App Stores and Malware
App Stores: Walled Garden vs Open Ecosystem
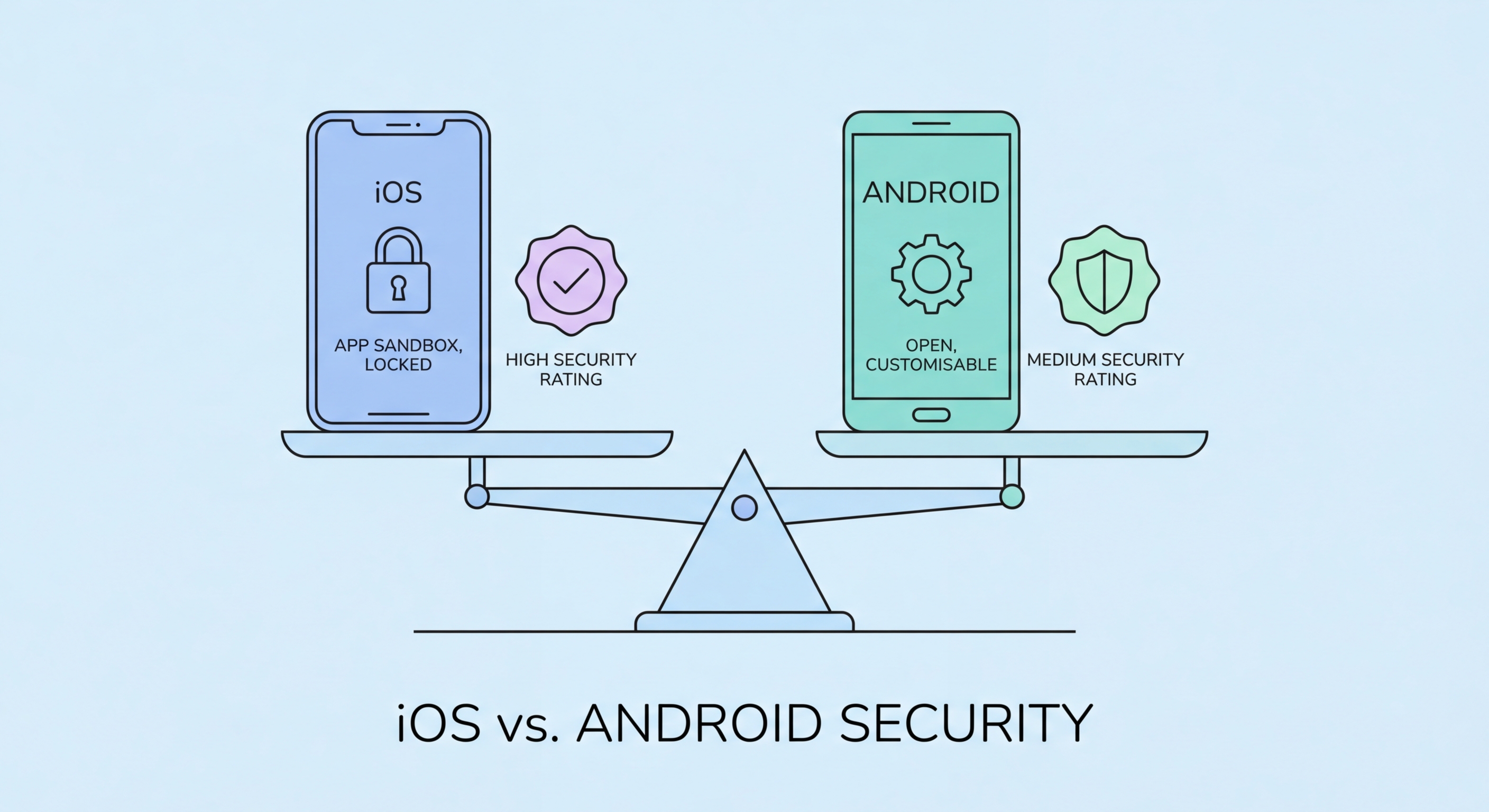
Apple's App Store is a closed ecosystem: every app must pass Apple's review process before reaching users, and developers cannot distribute iOS apps outside the App Store without explicit enterprise agreements or the new EU-mandated alternative marketplace provisions (which don't yet apply in Hong Kong). This gatekeeping significantly reduces the surface area for malware distribution, though it is not impenetrable — malicious apps have periodically slipped through Apple's review process, particularly through delayed or dormant malicious behaviour.
Android's open ecosystem is both its greatest strength for developers and its most significant security liability for mainstream users. While Google Play Protect scans over 100 billion apps per day and has become increasingly effective at detecting malware, users can also install apps from any APK file without going through the Play Store — a process called sideloading. This capability, combined with the widespread availability of pirated apps in WhatsApp groups and Telegram channels in Hong Kong, creates a substantial malware distribution channel that doesn't exist on iOS.
In 2026, the most significant app-based threats on both platforms involve not obvious malware but sophisticated apps that abuse legitimate permissions. Stalkerware — apps that appear to be parental controls or system utilities but secretly transmit location data, messages, and call logs — is a growing concern. On both platforms, carefully reviewing permissions, researching developers, and using official app stores exclusively remain the most effective defences.
- iOS sideloading restriction: Apps can only be installed through the App Store (outside the EU), eliminating the most common malware distribution channel.
- Google Play Protect: Android's built-in malware scanner checks installed apps and new downloads — keep it enabled and check its status regularly.
- Never sideload apps: On Android, never install APK files from WhatsApp groups, Telegram channels, or unofficial websites.
- App review manipulation: Both platforms have seen fake reviews used to boost malicious apps — check reviews critically for generic or non-specific language.
- Permissions at install: Legitimate apps request only the permissions they actually need; excessive permissions at install are a major red flag.
- Developer verification: Search for the developer's website and privacy policy before installing any app — legitimate developers always publish these.
Master app permissions on iOS and Android →