4Ongoing Prevention
Ongoing Prevention: Building Resilience After a Credential Breach
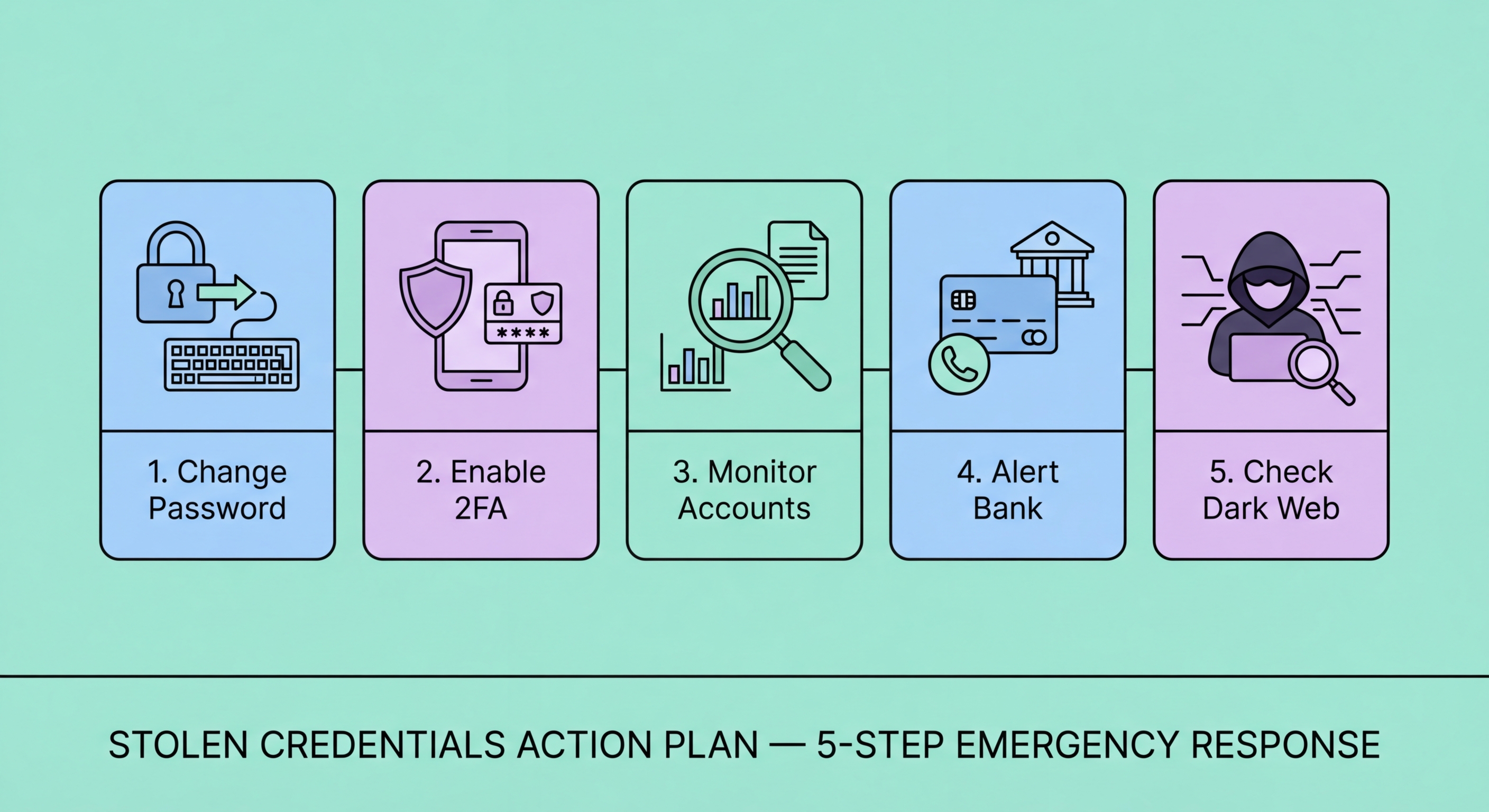
A credential breach is a strong signal that your overall security posture needs strengthening. Use the incident as a forcing function to implement security practices that should have been in place already. The most impactful change — by far — is to use a password manager with unique passwords for every account. If you are not currently using a password manager, install 1Password, Bitwarden, or iOS Passwords immediately and begin migrating all accounts to unique, manager-generated passwords. The password manager subscription (for paid options like 1Password, approximately HK$130-200/year) is one of the highest-return security investments available — a single credential breach exposing a reused password can cause losses of HK$50,000 or more from a banking account takeover.
Set up an ongoing dark web monitoring system if you haven't already. The minimum viable setup takes 15 minutes: register all email addresses at haveibeenpwned.com/NotifyMe for automatic breach notifications, enable breach monitoring in your password manager, and activate iOS or Google dark web monitoring for your primary email. For individuals who have experienced identity data (not just email/password) exposure, evaluate paid monitoring services that cover HKID numbers and phone numbers — both of which are primary identifiers in Hong Kong's identity system and both of which appear frequently in HK-targeted breach data. The investment in paid monitoring is much smaller than the cost of recovering from identity theft if early detection fails.
Strengthen your 2FA implementation systematically after the breach. Conduct a complete audit of all accounts where 2FA is available and not yet enabled — prioritising banking and investment accounts, email, cloud storage (Google Drive, iCloud, OneDrive), social media, and password manager. Where possible, upgrade from SMS-based 2FA to authenticator app 2FA or hardware security keys. SMS 2FA, while better than no 2FA, is vulnerable to SIM swap attacks — a growing fraud vector in Hong Kong. For the most critical accounts (primary email, banking, password manager), a hardware security key (YubiKey, Titan Key) provides the strongest available 2FA protection and is resistant to phishing, SIM swap, and remote attacks. After implementing comprehensive 2FA, your account security posture becomes substantially more resilient to credential theft even if future breaches expose passwords.
- Implement a password manager: The highest-impact security change available — 1Password, Bitwarden, or iOS Passwords with unique generated passwords for every account.
- Set up dark web monitoring: HIBP notifications (free) + password manager breach reports + consider paid monitoring for HKID/phone number coverage.
- Upgrade 2FA on all critical accounts: Authenticator app preferred over SMS; hardware security key (YubiKey) for highest-value accounts.
- Regular security hygiene: Monthly password manager breach report review; bi-annual TransUnion credit check; immediate action on all monitoring alerts.
- Reduce data exposure: Remove accounts from services you no longer use; minimise personal data shared with non-essential services — less data exposed means less damage in future breaches.
- Prepare for future incidents: Know your bank fraud line numbers (HSBC: 2233 3000, Hang Seng: 2198 7111), keep HKPF CSTCB (18222) in contacts, and document your account list for rapid incident response.
Build a comprehensive identity protection strategy for Hong Kong →