1Account Takeover
The First Priority: Credential Stuffing and Account Takeover
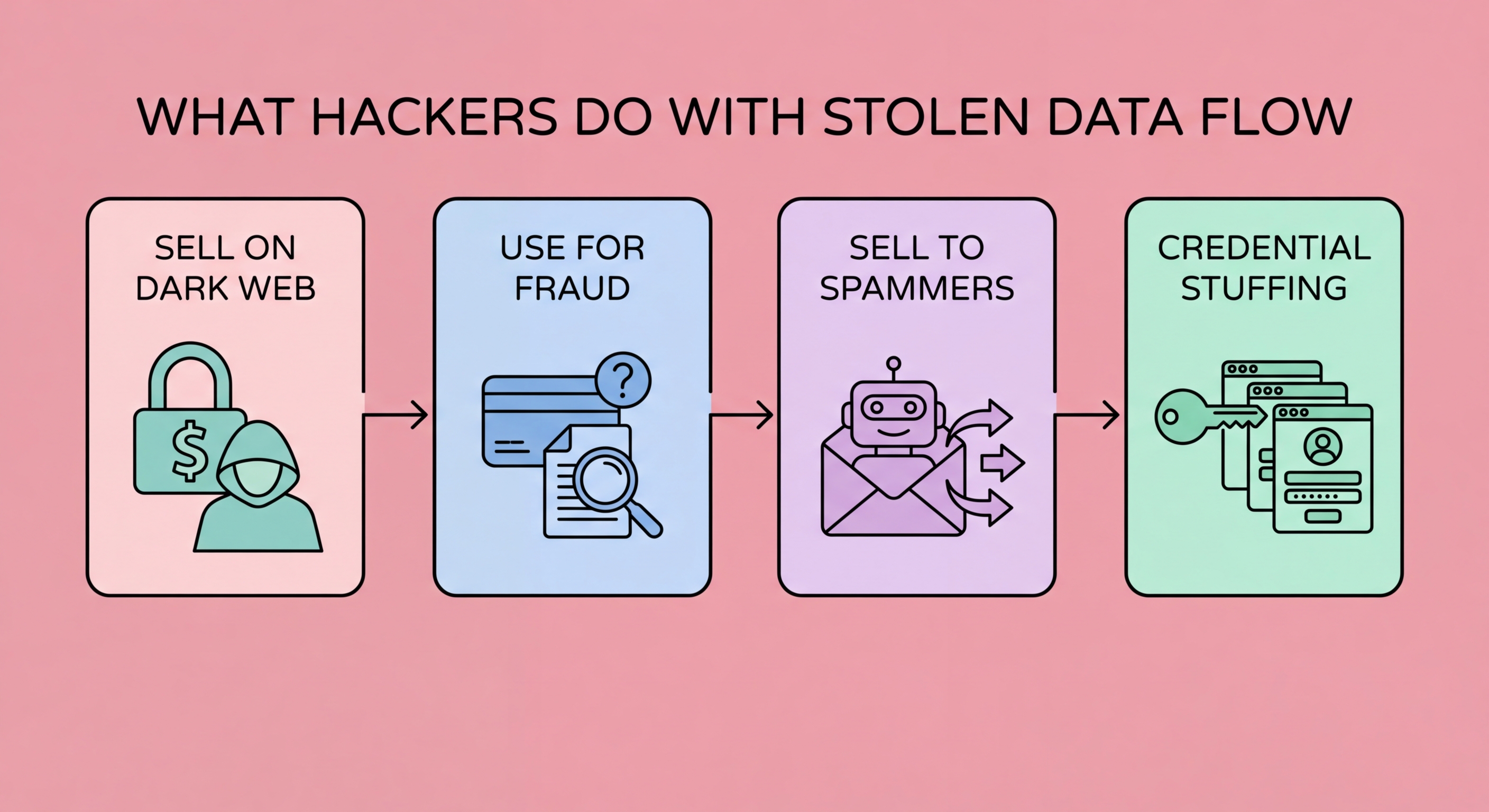
When a Data Breach?">data breach occurs and credentials are obtained, the fastest exploitation method is credential stuffing — the automated use of breached email/password combinations against high-value targets. Criminal groups maintain sophisticated automated tools that can test millions of credential pairs against banking sites, e-commerce platforms, email providers, and cryptocurrency exchanges within hours of a breach. The attack is effective because most people reuse passwords: a credential pair stolen from a low-security online store is immediately tested against HSBC, Hang Seng, PayMe, and every other high-value service that uses email as a username. Success rates for credential stuffing attacks range from 0.1% to 2% of tested credentials — seemingly low, but applied to a database of 10 million stolen credentials, even a 0.1% success rate yields 10,000 compromised accounts.
Account takeover of banking and financial accounts is the most immediately valuable outcome for criminals. Once inside a banking account, criminals work quickly: initiating FPS transfers to mule accounts, draining credit card balances through purchases at compliant merchants, changing contact details (email, to Spot and Avoid Attacks on Your Phone">Your Phone Number">phone number) to prevent security notifications from reaching the victim, and adding new beneficiaries for future transfers. The entire process from initial account access to fund extraction can take less than 30 minutes — the HKMA has noted that rapid transfer schemes give victims and banks very little time to intervene. Hong Kong's FPS (Faster Payment System) is a particular vector because transfers are near-instantaneous and, in fraud cases, are extremely difficult to reverse once processed.
Email account takeover is equally valuable — often more so — because email is the master key to all other accounts. Controlling a victim's email account allows criminals to initiate password resets for every service registered to that email address, access private correspondence that may contain account numbers, personal information, or business data, forward all incoming mail to monitor for security alerts, and impersonate the victim in communications with financial institutions. In Hong Kong, criminals who gain access to an email account can use it to contact the victim's bank directly — pretending to be the account holder requesting account changes, additional cards, or credit limit increases. This explains why protecting your email account with a unique, strong password and hardware 2FA should be the absolute top priority of any security strategy.
- Credential stuffing is immediate: Automated tools test breached credentials against high-value services within hours of a breach — password reuse makes this highly effective.
- Banking accounts are the top target: FPS transfers and credit card draining are the immediate objectives; account changes prevent victims receiving security alerts.
- Email is the master key: Email account control enables password resets for all linked services — protect it with unique password and hardware 2FA.
- Speed of exploitation: HKMA data shows fund extraction from breached banking accounts can occur within 30 minutes of initial access — rapid monitoring and alerts are essential.
- Cryptocurrency exchanges: HK-based crypto accounts (OSL, HashKey) are high-priority targets; cryptocurrencies are immediately movable and very difficult to recover.
- Defence: Unique passwords per service (eliminates credential stuffing effectiveness) and 2FA (blocks account access even with correct credentials).
Full action plan for responding to account takeover attacks →