2Credential Hardening
Layer 2: Credential Hardening and Two-Factor Authentication
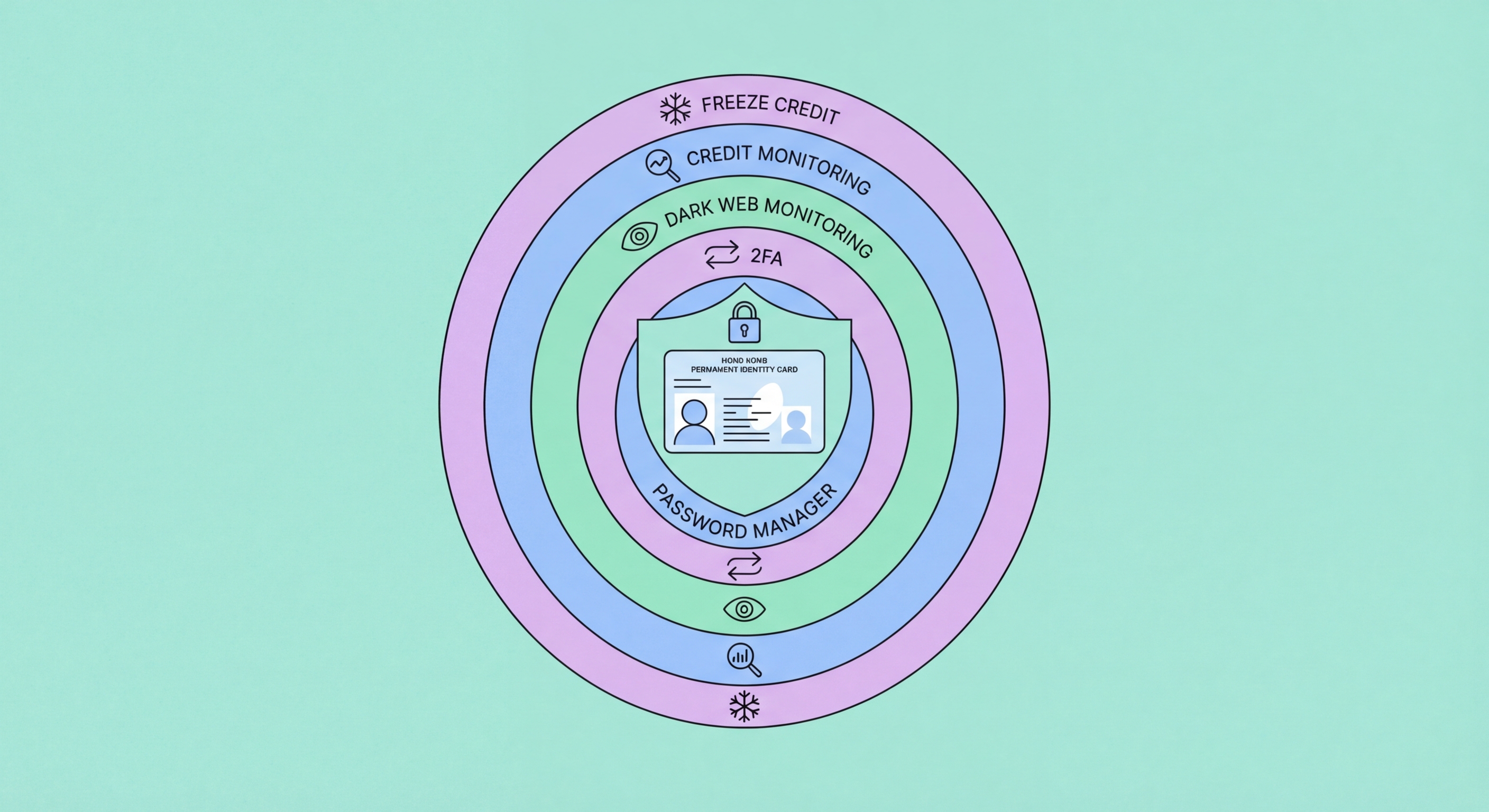
The free monitoring stack detects when your credentials are exposed; credential hardening makes the exposure meaningless. The two-part approach — unique passwords and two-factor authentication — closes the two most common account takeover pathways simultaneously. Unique passwords (generated and stored by a password manager) eliminate credential stuffing: a criminal who purchases a database of 10 million stolen passwords and tests them against your banking portal will fail on every account where you've used a unique, unreused password. Two-factor authentication (2FA) means that even a password that wasn't unique and was successfully used by a criminal still can't access your account without the second factor you hold physically. Together, these two controls provide defence-in-depth: you need both to fail for an account takeover to succeed.
Priority order for 2FA implementation matters — not every account carries the same risk. Begin with your primary email account: email is the password reset gateway for all other services, making it the highest-leverage attack target. Enable 2FA on your email using an authenticator app (Google Authenticator, Authy, or 1Password's built-in TOTP feature) rather than SMS OTP, since SMS is vulnerable to SIM swap attacks. Next, enable 2FA on your banking accounts — check your bank's app for available options; HSBC, Hang Seng, BOC, and DBS all offer 2FA options beyond SMS. Enable 2FA on your password manager account itself (this is critical — losing password manager access through a compromised 2FA method would be catastrophic). Then work through cloud storage (Google Drive, iCloud, OneDrive), social media (Instagram, Facebook, LinkedIn), and finally all remaining accounts in your password manager.
For the highest-risk accounts — primary email, password manager, banking, and investment accounts — hardware security keys (YubiKey, Google Titan Key) provide the strongest available 2FA protection. Hardware keys are phishing-resistant (they verify the domain of the site requesting authentication, refusing to authenticate on phishing sites), SIM-swap resistant (they require physical possession of the key), and remote-attack resistant (they require physical presence). A pair of hardware keys for your most critical accounts (approximately HK$600-1,200 for two keys — one primary, one backup) is one of the most cost-effective security investments available for high-risk individuals, particularly for those who have previously experienced account takeover or who hold significant financial assets. Passkeys — the next generation of phishing-resistant authentication built into iOS, Android, and macOS — provide similar protections and are becoming increasingly available on HK banking and financial services platforms.
- Unique passwords for every service: Password manager-generated, 20+ character random passwords eliminate credential stuffing as an attack vector.
- 2FA priority order: Primary email → password manager → banking → cloud storage → social media → everything else.
- Authenticator app over SMS: TOTP authenticator apps (Google Authenticator, Authy, 1Password) are not vulnerable to SIM swap attacks; use them wherever available.
- Hardware keys for highest-risk accounts: YubiKey or Google Titan Key for primary email, password manager, banking — phishing-resistant and SIM-swap-resistant.
- Passkeys where available: Apple/Google/Microsoft passkeys provide hardware-level security without the physical key — enable on all platforms that support them.
- Backup codes: Store 2FA backup codes for critical accounts in your password manager or a secure physical location — losing 2FA access to your email has catastrophic cascading effects.
What to do immediately when your credentials are compromised →