Dark Web vs Deep Web: Understanding the Difference
The terms "dark web" and "deep web" are frequently confused. Here's the definitive breakdown of what each term means, with concrete examples relevant to Hong Kong internet users.
The terms "dark web" and "deep web" are frequently confused. Here's the definitive breakdown of what each term means, with concrete examples relevant to Hong Kong internet users.
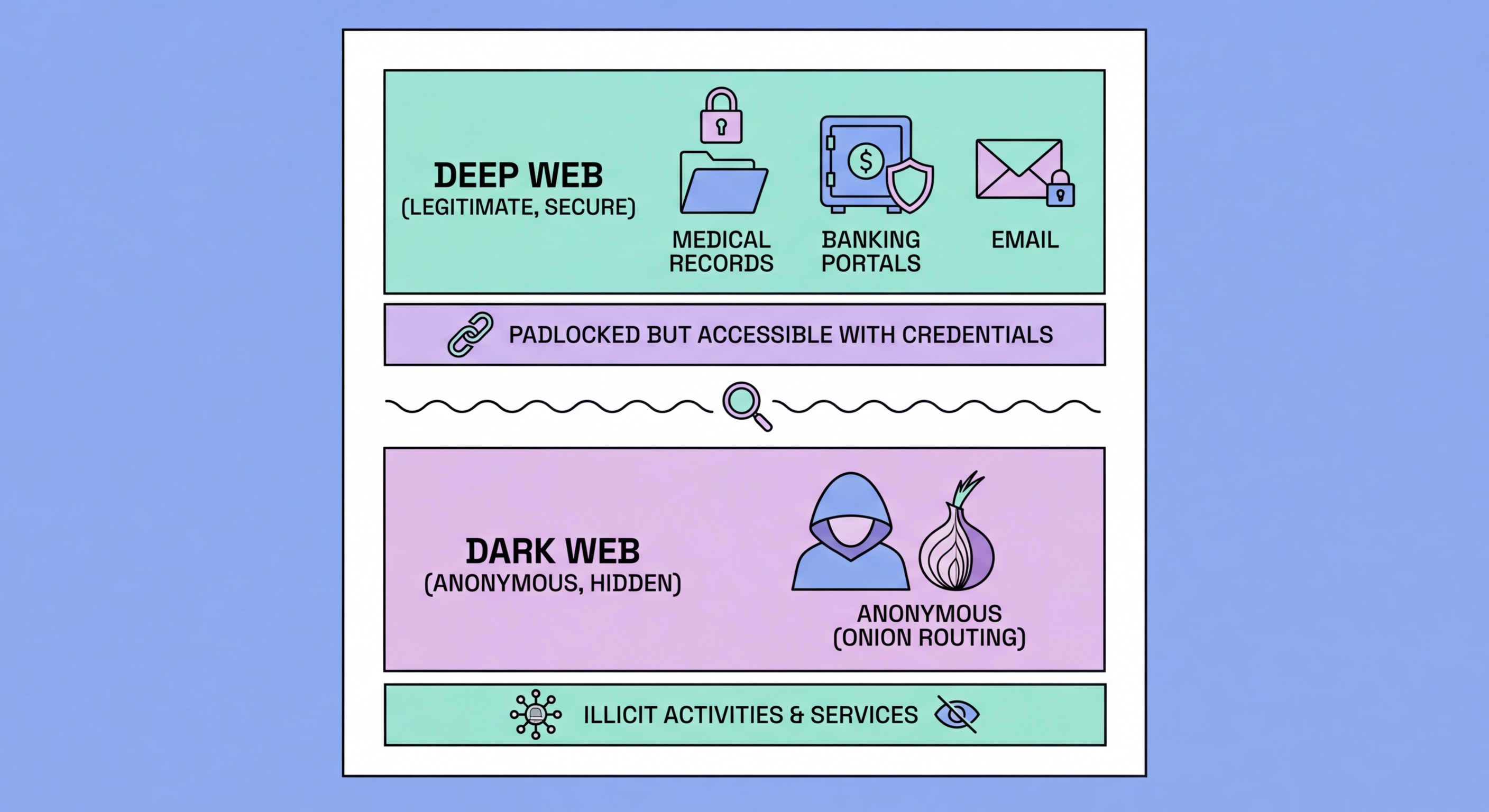
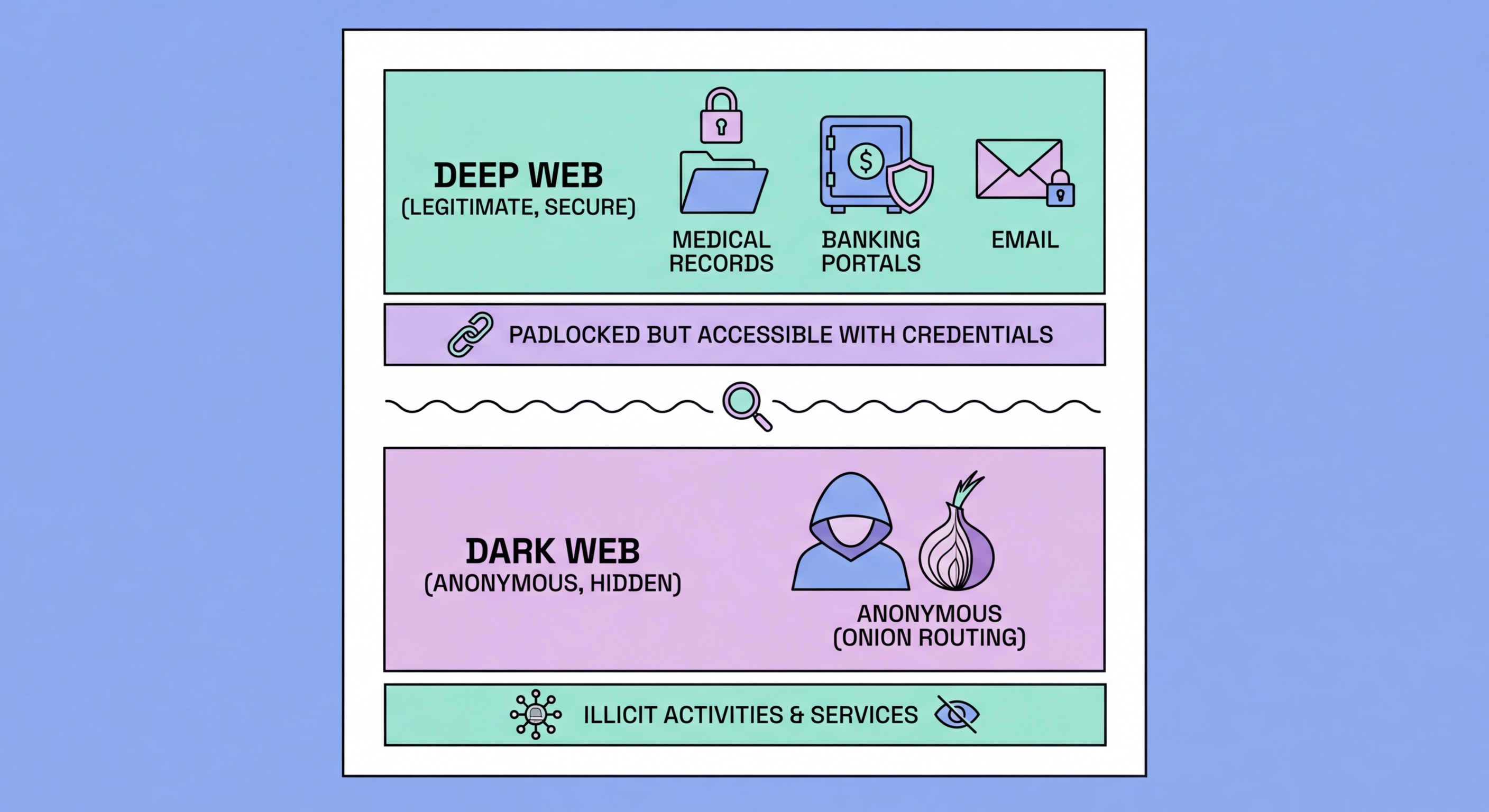
The deep web refers to all internet content that is not indexed by standard search engines like Google, Bing, or Yahoo. This includes anything behind a login screen, any content generated dynamically in response to a database query, any private communication, and any web content intentionally excluded from search engine indexing via robots.txt or similar mechanisms. The deep web is vast — estimates suggest it is 400-500 times larger than the surface web — and the overwhelming majority of it is entirely benign and legal.
If you've ever logged into online banking at HSBC or Hang Seng, checked your MPF account balance, read a private email in Gmail, accessed a company intranet, used a hospital patient portal, or searched an academic database like JSTOR, you've been in the deep web. Your medical records, financial statements, private messages, and subscription content are all part of the deep web. The defining characteristic is simply that this content is not publicly indexed and cannot be found via a web search.
The deep web is not a place you navigate to — it's a category that describes content inaccessible without authentication or specific access rights. There's no single gateway or browser required; your normal browser accesses deep web content the moment you log into any authenticated service. The deep web is where most sensitive and valuable information on the internet resides precisely because it requires authentication to access — your bank statement is deep web content not because it's hidden for nefarious reasons, but because it requires you to prove your identity to access it.

The to Check If Your Data Is on the Dark Web">dark web is a small subset of the deep web that is specifically designed for anonymity and requires special software — predominantly the Tor Browser — to access. Unlike the broader deep web, which is simply content not indexed by search engines, the Data Breach? From Hack to Dark Web">dark web uses technical mechanisms to obscure both the identity of users and the location of servers. Dark web sites use .onion domains — generated cryptographically and resolvable only through the Tor network — rather than standard DNS-registered domains.
The key distinction from the broader deep web is intent and mechanism. The deep web is not indexed because it contains private authenticated content; the dark web is designed from the ground up to resist identification of both parties in any communication. Tor's onion routing — bouncing traffic through multiple encrypted relays — makes it very difficult to trace the origin of either a request or a server. This design makes the dark web suitable for legitimate activities that require strong anonymity (journalism, whistleblowing, political activism in repressive environments) but also attractive for criminal activities that benefit from the same anonymity.
The dark web does not require special knowledge to access — the Tor Browser, available free from torproject.org, works similarly to a regular browser and can be downloaded by anyone. However, navigating to dark web sites requires knowing their .onion addresses, as there is no Google equivalent for the dark web. Dark web directories and link aggregators exist but are themselves unofficial and not reliably comprehensive. Most people who are concerned about the dark web don't need to access it directly — they need to know if their data has ended up there, which can be checked through dark web monitoring services without accessing the dark web yourself.

The fundamental distinction is one of design intent. The deep web exists because not all content should be publicly searchable — authenticated, private, and proprietary content naturally resides here. The dark web was specifically engineered to provide strong anonymity. You don't choose to put content on the deep web — it's automatically deep web if it's not publicly indexed. Dark web content is deliberately placed there by operators who chose to use .onion hosting for its anonymity properties.
From a security and privacy perspective, the deep web holds the most valuable data for most individuals and organisations: banking credentials, personal data, medical records, business information, and communications. This is why deep web content is such a valuable target for cybercriminals — breaching a company's internal systems and accessing its deep web databases is far more lucrative than scraping its public website. The dark web, meanwhile, is where stolen deep web data ends up for sale after a breach.
For Hong Kong residents monitoring their digital security, the relevant question is not "what is on the deep web" (answer: your private data) but "has any of my deep web data leaked to the dark web" (answer: possibly, if any service you use has experienced a breach). Dark web monitoring services bridge this gap by scanning dark web markets and forums for your specific data — effectively checking whether your private authenticated information has been stolen and listed for sale by criminals.

Understanding this distinction clarifies the actual threat model for Hong Kong internet users. The threat is not that you personally visit the dark web (most people never do or need to) — the threat is that criminal actors use the dark web to trade data that was stolen from legitimate services you use. Your HKBC online banking is deep web content; if HKBC experienced a breach and your credentials were stolen, those credentials might then appear on a dark web marketplace. The dark web is the destination; your deep web data is the target.
This understanding also clarifies the limitations of "deep web" as a scare term used in some media reporting. When journalists write about content "found on the deep web," they usually mean the dark web or simply non-indexed content — deep web content that is legitimately private (your banking, email, etc.) is not concerning. The concerning category is specifically data that has leaked from private (deep web) systems to public criminal markets (dark web).
For a practical response: your deep web data is protected by the authentication systems and security practices of the services that hold it. You can improve this protection by using unique strong passwords (so a breach of one service doesn't expose others) and enabling 2FA (so stolen credentials alone can't be used). Your dark web exposure is monitored through services like HIBP. The combination of good credential hygiene and active dark web monitoring covers the two most important bases.
