4Action Plan
What Hong Kong Users Should Do Now to Stay Ahead
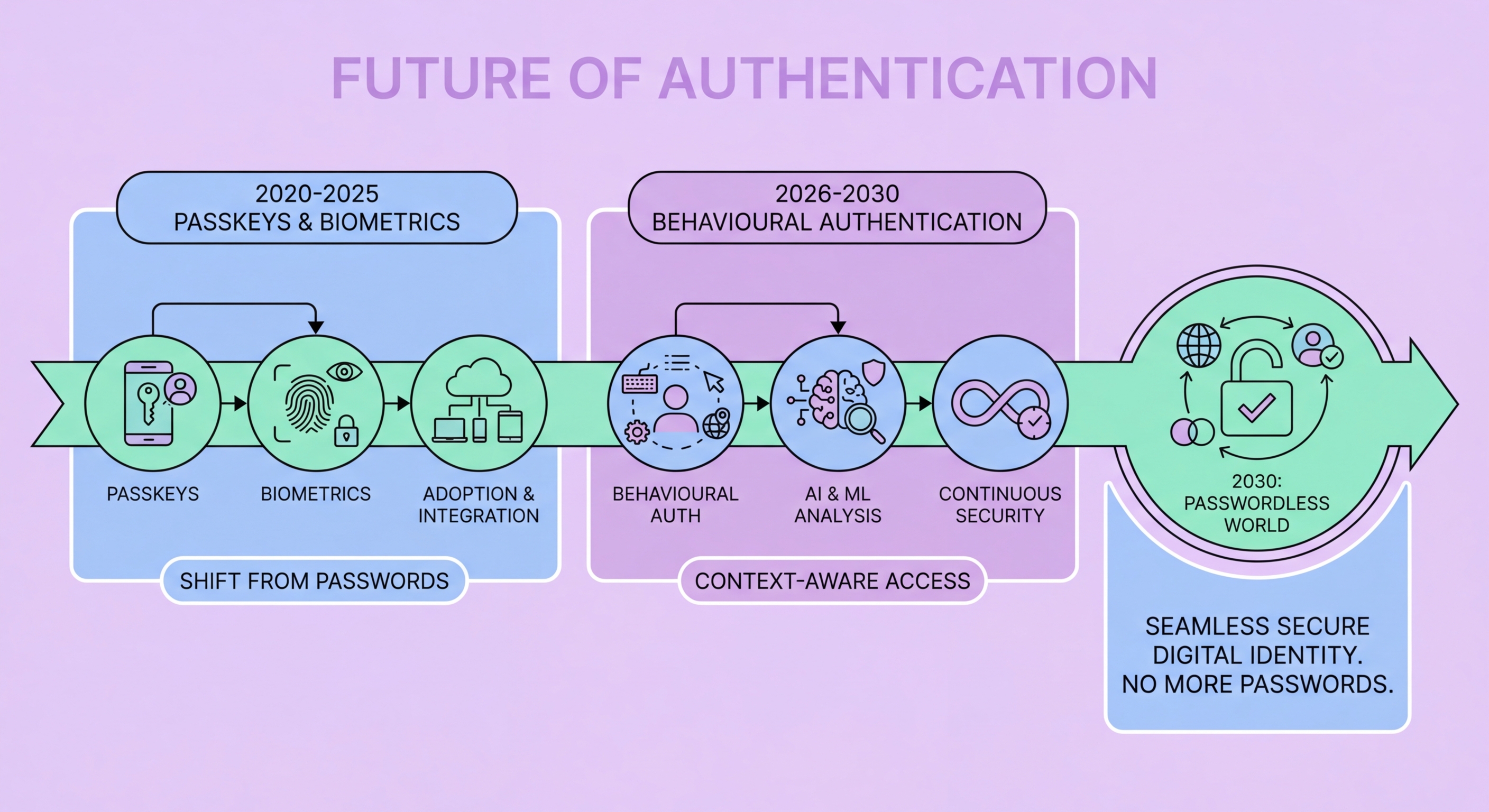
The authentication landscape is evolving rapidly, but the actions that prepare you for the future are the same ones that protect you best today. Start adopting passkeys now, while they are early but widely available. Create passkeys for Google, Apple, Microsoft, and any other service you use that supports them. This positions you ahead of the curve, trains you to use the authentication method that will dominate the next decade, and provides you with real, immediate security benefits today.
For services that do not yet support passkeys, upgrade from SMS to an authenticator app if you have not already. The authenticator app ecosystem is mature, works well, and provides dramatically better security than SMS without requiring new hardware. This step alone eliminates the most common attack vector for account takeover among ordinary Hong Kong internet users. If you manage high-value accounts — cryptocurrency, business email, or accounts with significant follower bases — add a hardware security key for FIDO2 phishing resistance on services that support it.
At the institutional level, Hong Kong businesses should be aware of HKMA's evolving guidance on strong authentication for financial services, track updates to the Cyber Resilience Assessment Framework, and begin planning the transition from authenticator app-based MFA to phishing-resistant MFA for privileged accounts. The technology is available today, the regulatory direction is clear, and early movers will be better positioned when phishing-resistant MFA becomes a hard requirement rather than a recommendation. The future of authentication in Hong Kong, as globally, belongs to biometric-backed cryptographic credentials — and that future is already here for those who choose to adopt it.
- Action 1: Create passkeys for Google, Apple, Microsoft, and other supported services today
- Action 2: Move all remaining accounts from SMS to an authenticator app (TOTP)
- Action 3: Add a hardware key for high-value accounts where passkeys aren't supported
- Action 4: Save backup codes and set up recovery contacts on all critical accounts
- Business Action: Monitor HKMA guidance and plan phishing-resistant MFA for privileged access
- Long-term: Track passkey support expansion — the list of supporting services grows monthly
Start with passkeys — the authentication future available right now →