3macOS Configuration
macOS Firewall and Stealth Mode Configuration
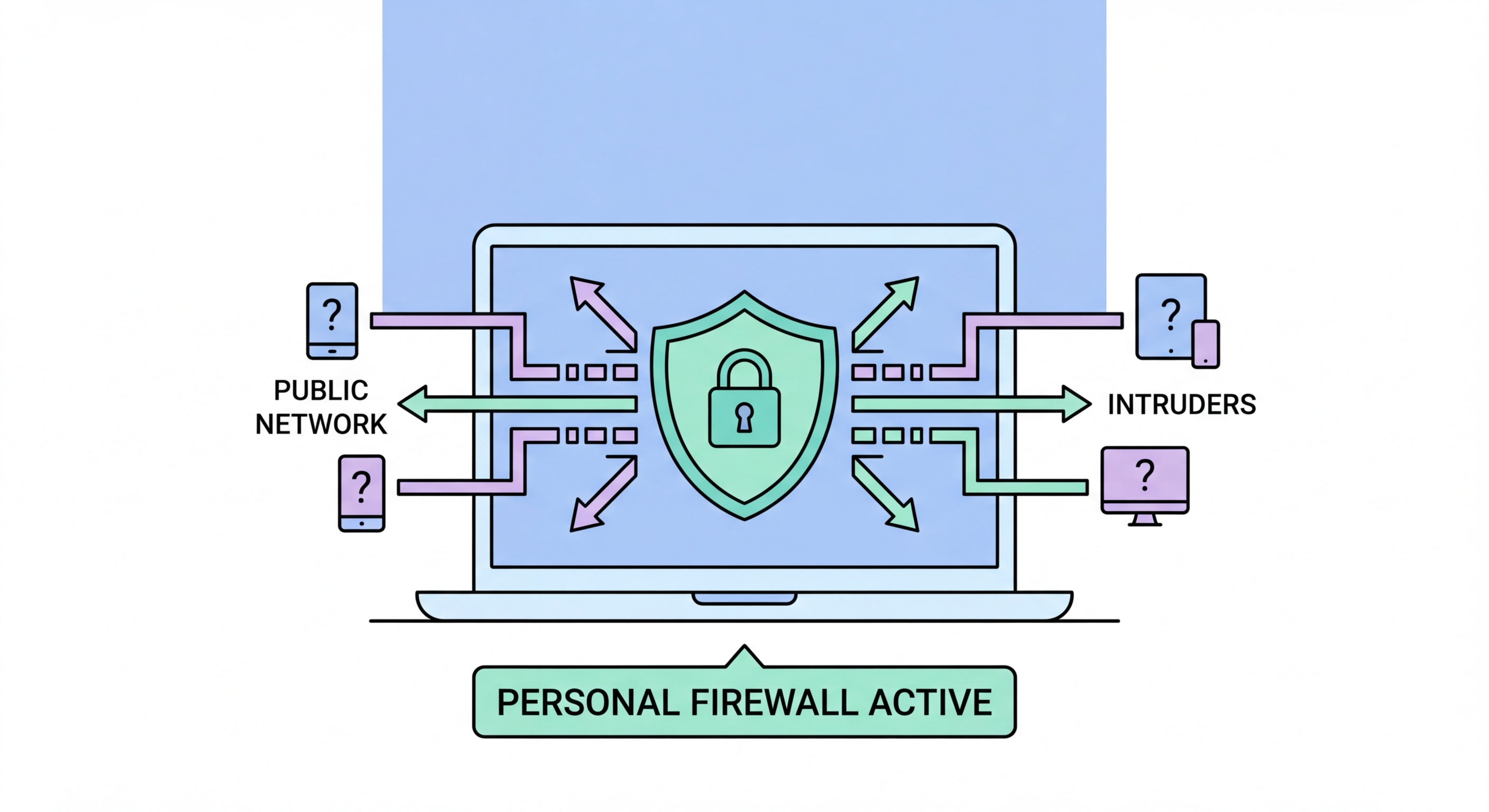
macOS includes a built-in application firewall that controls which applications are allowed to accept incoming connections. Unlike Windows Defender Firewall, macOS does not have separate network profiles for home vs. public networks — the firewall settings apply uniformly. However, macOS separates the firewall from the sharing settings, so configuring public WiFi security on macOS requires addressing both. To enable the firewall: System Settings → Network → Firewall → toggle on. Once enabled, click "Firewall Options" to review and configure which applications are allowed to accept incoming connections. Block all unnecessary applications from accepting inbound connections by clicking the minus button to remove them or changing their setting to "Block incoming connections."
Stealth Mode is a macOS firewall option that prevents your Mac from responding to network probe requests. Without Stealth Mode, if another device on the network pings your Mac or probes its ports, your Mac responds — confirming its existence and presence on the network. With Stealth Mode enabled, your Mac silently ignores these probes, making it much harder for attackers to detect and map your device on the network. Enable Stealth Mode: System Settings → Network → Firewall → Firewall Options → check "Enable Stealth Mode." This is highly recommended for any Mac used on public WiFi networks and adds meaningful obscurity protection at no cost to normal functionality — your outbound connections work normally, only unsolicited inbound probes are silently dropped.
The Sharing panel is equally important on macOS. File sharing, screen sharing, remote login, remote management, and AirPlay receiving are all services that make your Mac accessible to other devices on the same network. On public WiFi, none of these should be enabled. Go to System Settings → General → Sharing and verify that File Sharing, Screen Sharing, Remote Login, Remote Management, and any other sharing services are turned off. AirDrop, while a separate feature, also uses the local network for device discovery — set AirDrop to "No One" when on public WiFi through the Finder menu or Control Centre. These sharing settings are independent of the firewall; even with the firewall enabled, sharing services may accept connections on ports the firewall is configured to allow.
- Enable firewall: System Settings → Network → Firewall → toggle on
- Block unnecessary apps: Firewall Options → remove or block apps that don't need inbound connections
- Stealth Mode: Firewall Options → "Enable Stealth Mode" — silently drops network probe responses
- Disable sharing: System Settings → General → Sharing — disable File Sharing, Screen Sharing, Remote Login
- AirDrop: Set to "No One" when on public WiFi via Finder or Control Centre
- Verify after updates: macOS major updates occasionally reset sharing settings — re-check after updates
The complete public WiFi safe practices checklist including all device settings →