4After Setup
Managing Google 2FA: Trusted Devices, Recovery, and Troubleshooting
After enabling Google 2FA, you may be prompted on each new login to "trust" the device for 30 days. This tells Google not to require 2FA again on that device for 30 days. Use this option judiciously: trust your personal laptop and home computer, but never trust public computers at libraries, hotels, or internet cafés. You can review and revoke trusted devices in the "Manage trusted devices" section of your Google account security settings.
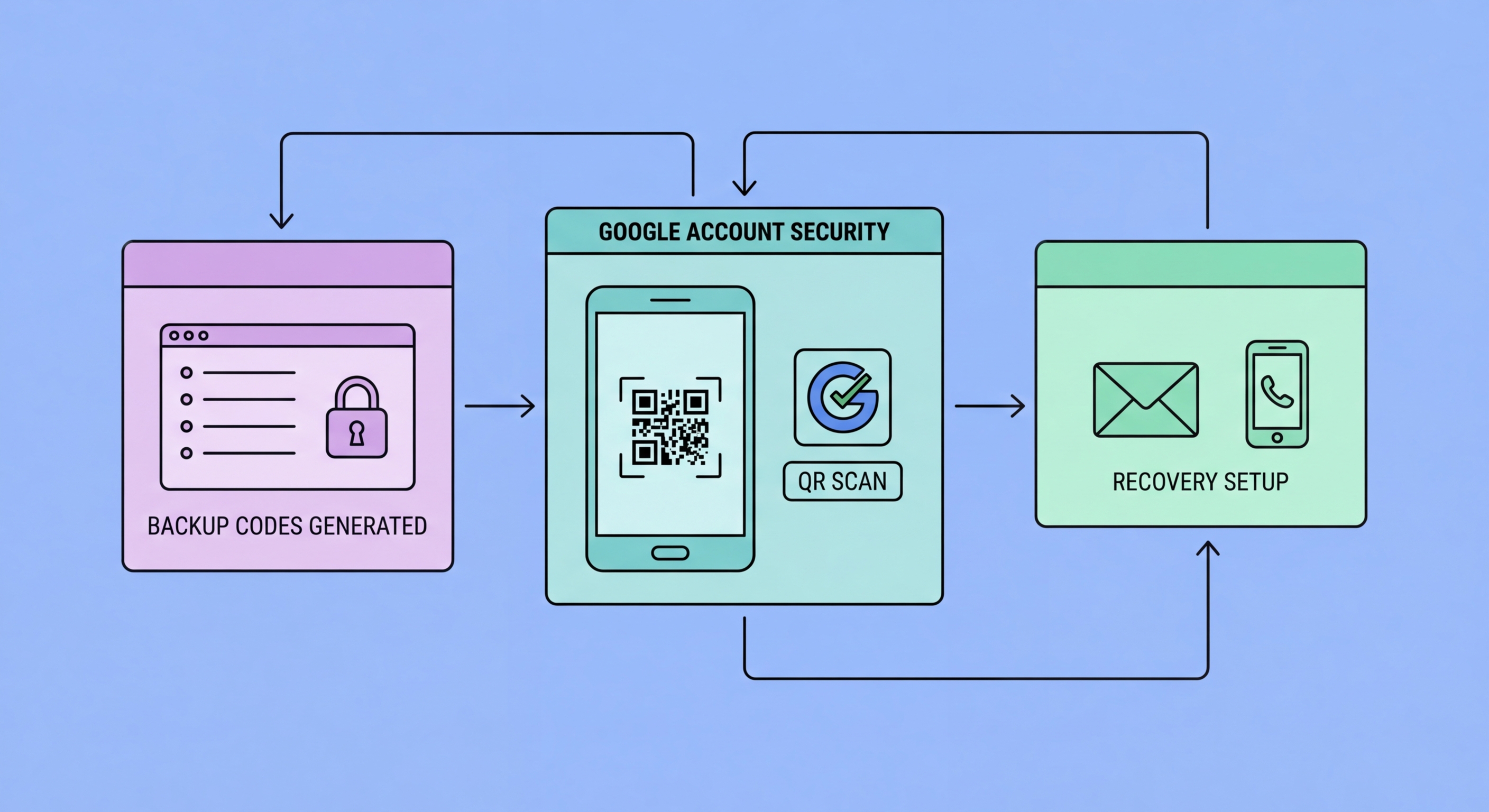
If you change phones, you should update your Google 2FA before losing access to the old phone. With Google Prompts, the new phone automatically becomes eligible for prompts once you sign in to your Google account on it. For your authenticator app setup, you will need to re-scan the setup QR code from Google — go to myaccount.google.com → Security → 2-Step Verification → Authenticator app → Change phone, and scan the new QR code in your new app. Alternatively, if you used Authy or Google Authenticator with backup enabled, the codes transfer with the backup.
If you are locked out — you cannot access your phone, authenticator app, or backup codes — use the Google account recovery at accounts.google.com/signin/recovery. Google will attempt to verify your identity using signals like trusted devices where you have recent login history, recovery phone number, or recovery email. Set these up now, before you need them. A recovery email address should ideally be a different email provider (not another Gmail), secured with its own 2FA.
- Trusted devices: Only trust personal, private devices — never public computers
- Phone change: Update authenticator app by scanning a new QR code from Google security settings
- Recovery email: Set a non-Gmail recovery email — secured with its own 2FA
- Recovery phone: Keep your recovery phone number current in Google settings
- Check security settings annually: Review and update 2FA methods each year
- Backup codes: Regenerate and resave backup codes if you lose or use your current set
See the full guide to recovering from 2FA lockout →