4If You're Compromised
What to Do If Your Password May Have Been Compromised on Public WiFi
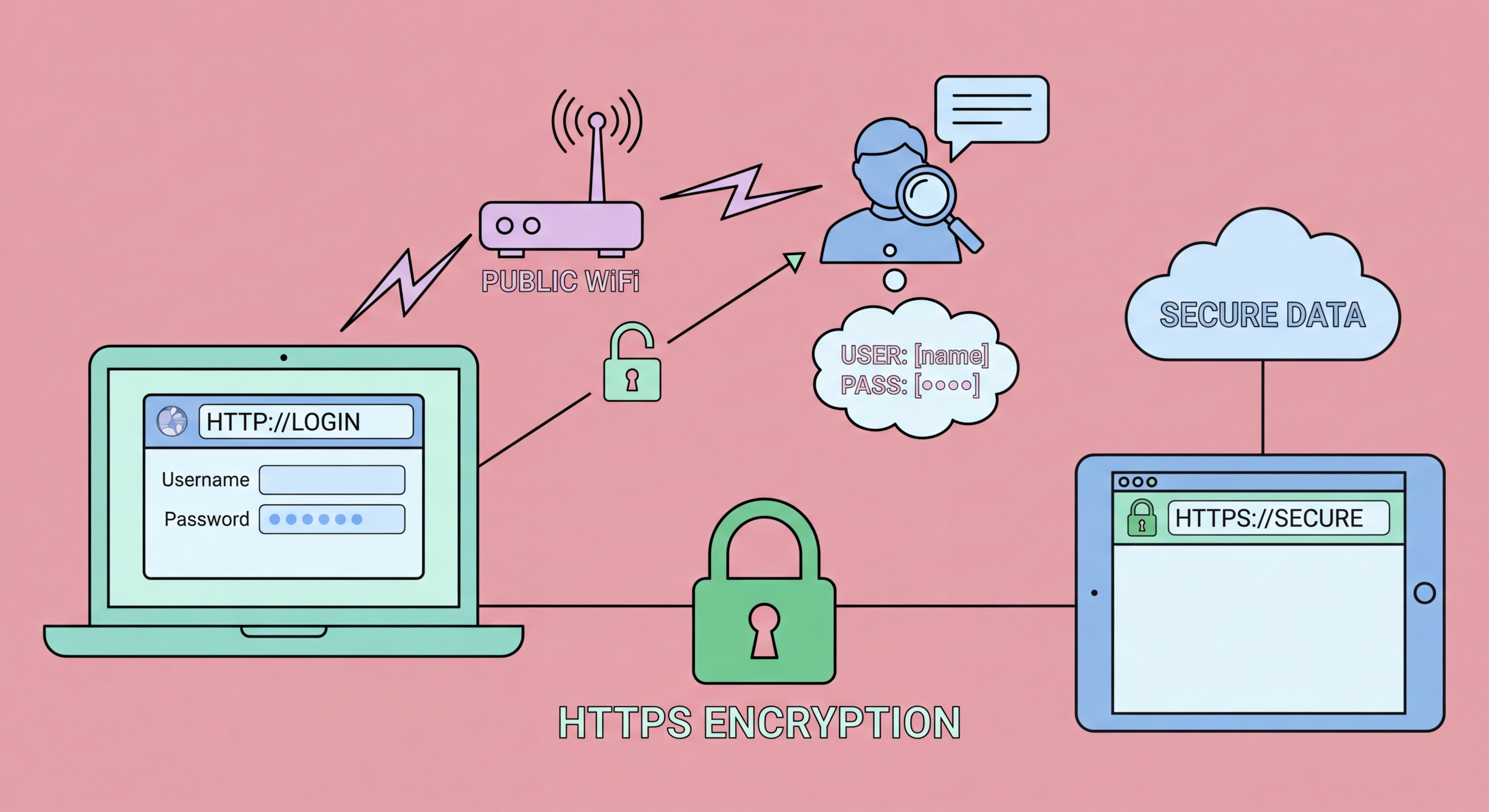
If you suspect a password may have been stolen on a public WiFi session — perhaps you noticed suspicious network behaviour, received an unexpected login notification, or accessed a sensitive account without VPN protection in a high-risk environment — act promptly and systematically. Change the compromised password immediately from a trusted network (your home WiFi or mobile data). Do not wait — if an attacker has the password, every hour of delay is an opportunity for them to use it. After changing the password, review the account's login history and active sessions: most major services (Google, Apple, Microsoft, Facebook) show recent login activity including device type, location, and time. Look for any sessions you do not recognise and terminate them.
Check connected applications and OAuth authorisations for the compromised account. Many accounts allow third-party applications to connect via OAuth — if an attacker accessed your account, they may have authorised a malicious application that maintains access even after you change your password. In Google Account: Security → Third-party apps with account access. In Microsoft/Outlook: myaccount.microsoft.com → Privacy → Apps and services. In each case, revoke any application you do not recognise. Enable or verify 2FA is active after changing the password — this is the most important step to prevent the stolen password from being used again in the future. If you have 2FA enabled already, changing the password alone should be sufficient to lock out an attacker who does not have your second factor.
For potential corporate email compromise, escalate to your organisation's IT security team immediately rather than attempting to resolve it personally. The IT security team can review access logs, identify whether any data was exfiltrated, check whether any email rules were created (attackers commonly create rules to forward copies of email to external addresses), and initiate formal incident response procedures. If your company is in a regulated industry (financial services, legal, medical), data breach notification requirements may apply even to suspected incidents. Report suspected BEC to the Hong Kong Police Force's Cyber Security and Technology Crime Bureau at [email protected] and file a report through the HKPF CyberDefender portal. For banking credential compromise, contact your bank's fraud helpline immediately — HSBC, Hang Seng, and other major HK banks have 24-hour fraud hotlines for exactly this scenario.
- Change immediately: Change compromised password from trusted network without delay
- Review login history: Check account login activity for unrecognised sessions — terminate them
- Revoke OAuth apps: Check and revoke unrecognised third-party app authorisations
- Enable/verify 2FA: Ensure 2FA is active after password change to prevent future use
- Corporate incident: Escalate work email compromise to IT security team — don't handle alone
- Report to HKPF: File cyber crime report at [email protected] for banking and BEC incidents
Prevention is better than response — apply all 10 safe WiFi practices →