3Safe vs Unsafe Activities
What's Safe and What's Not on Hong Kong Café WiFi
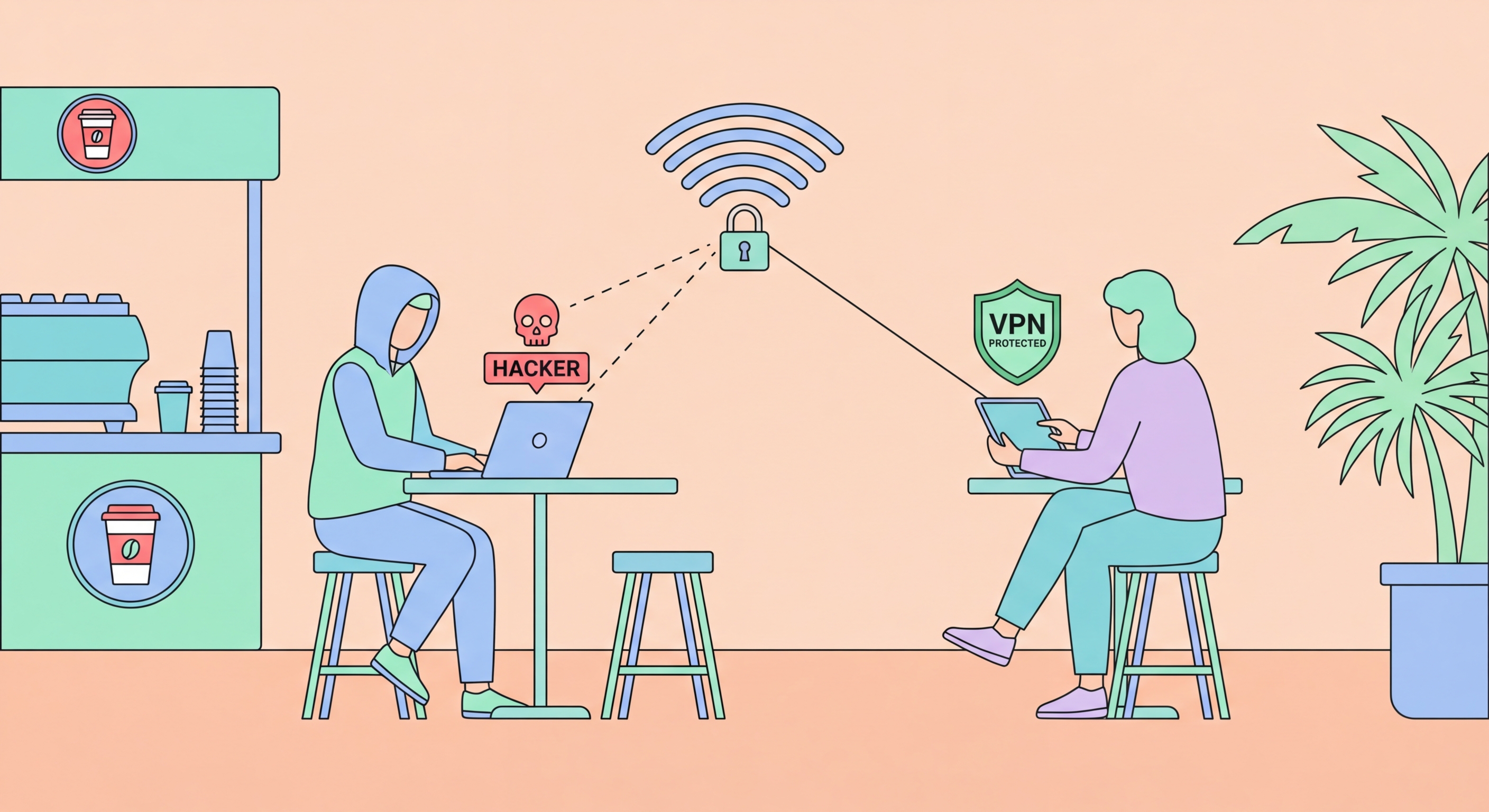
With a VPN active, café WiFi is suitable for a broad range of work and personal activities. Reading news and general web browsing over HTTPS sites is low-risk even without a VPN, but adding a VPN makes it safe enough for anything other than the most sensitive tasks. With a VPN: email (including work email), productivity apps (Google Workspace, Microsoft 365, Notion), video calls where the content is not highly confidential, and cloud storage access are all acceptable. The VPN encrypts your traffic before it reaches the café network, rendering eavesdropping and MITM attacks ineffective. The one activity that remains higher-risk on café WiFi even with a VPN is submitting credentials for very high-value accounts — banking, corporate admin accounts, domain registrars — because the VPN protects against network-level attacks but not against phishing or keyloggers on your device.
Without a VPN, the risk profile of café activities shifts significantly. Without a VPN, you should avoid: logging into any account where you would not want the session to be visible, submitting forms with personal information on any site (even HTTPS sites, because HTTPS gaps remain), accessing work systems with business data, and downloading or uploading sensitive documents. Without a VPN on an open café network, DNS queries are plaintext (revealing sites visited), and any unencrypted traffic is fully readable. With HTTPS-only traffic and no VPN, the content is encrypted but metadata (which sites, when, how much data) is visible. For casual browsing this is acceptable; for any professional or sensitive activity it is not.
Specific activities to avoid entirely on café WiFi, regardless of VPN status: banking and financial transactions (use mobile data instead), entering corporate VPN credentials over café WiFi (use mobile data to establish the corporate VPN), installing software or updates (malware injection risk on unprotected networks), and using café network printers (printer connections on a café network may expose documents to other network users). If you regularly work from cafés and need to access corporate systems, establish a protocol: connect to café WiFi, enable your personal VPN immediately, then use the personal VPN to connect to your corporate VPN. The layered encryption (personal VPN + corporate VPN) provides strong protection for corporate access from café environments.
- Safe with VPN: Email, cloud productivity apps, video calls, general browsing, HTTPS sites
- Safe without VPN: HTTPS news, streaming media, non-sensitive general browsing only
- Avoid without VPN: Account logins, form submissions, work systems, document access
- Avoid even with VPN: Banking (use mobile data), corporate VPN credentials (use mobile data first)
- Never on café WiFi: Software installation, corporate admin account logins, financial transactions
- Layered VPN: Personal VPN → corporate VPN provides strong protection for remote corporate access
How to handle corporate access securely from café and public WiFi →