2Real Attacks
Real Hotel WiFi Attacks: DarkHotel and Beyond
The "DarkHotel" APT (Advanced Persistent Threat) group, first documented by Kaspersky Lab in 2014, demonstrated that nation-state attackers specifically target hotel networks to compromise high-profile business travellers. The DarkHotel operation involved penetrating hotel networks and positioning malware that prompted specific targeted guests to install what appeared to be legitimate software updates when connecting to the hotel WiFi. The malware, once installed, provided the attackers with access to corporate emails, intellectual property, and strategic business plans from the targeted executives.
The DarkHotel campaign operated primarily across Asia, targeting guests at luxury hotels in Japan, Taiwan, China, Russia, and Korea — precisely the kind of travel corridors used by Hong Kong-based executives and international business visitors. The operation was notable not just for its technical sophistication but for the targeting intelligence it demonstrated: attackers knew which specific guests to target, what hotels they would stay at, and when they would arrive. This level of targeting suggests not just technical compromise but some combination of insider information, compromised booking systems, or open-source intelligence gathering.
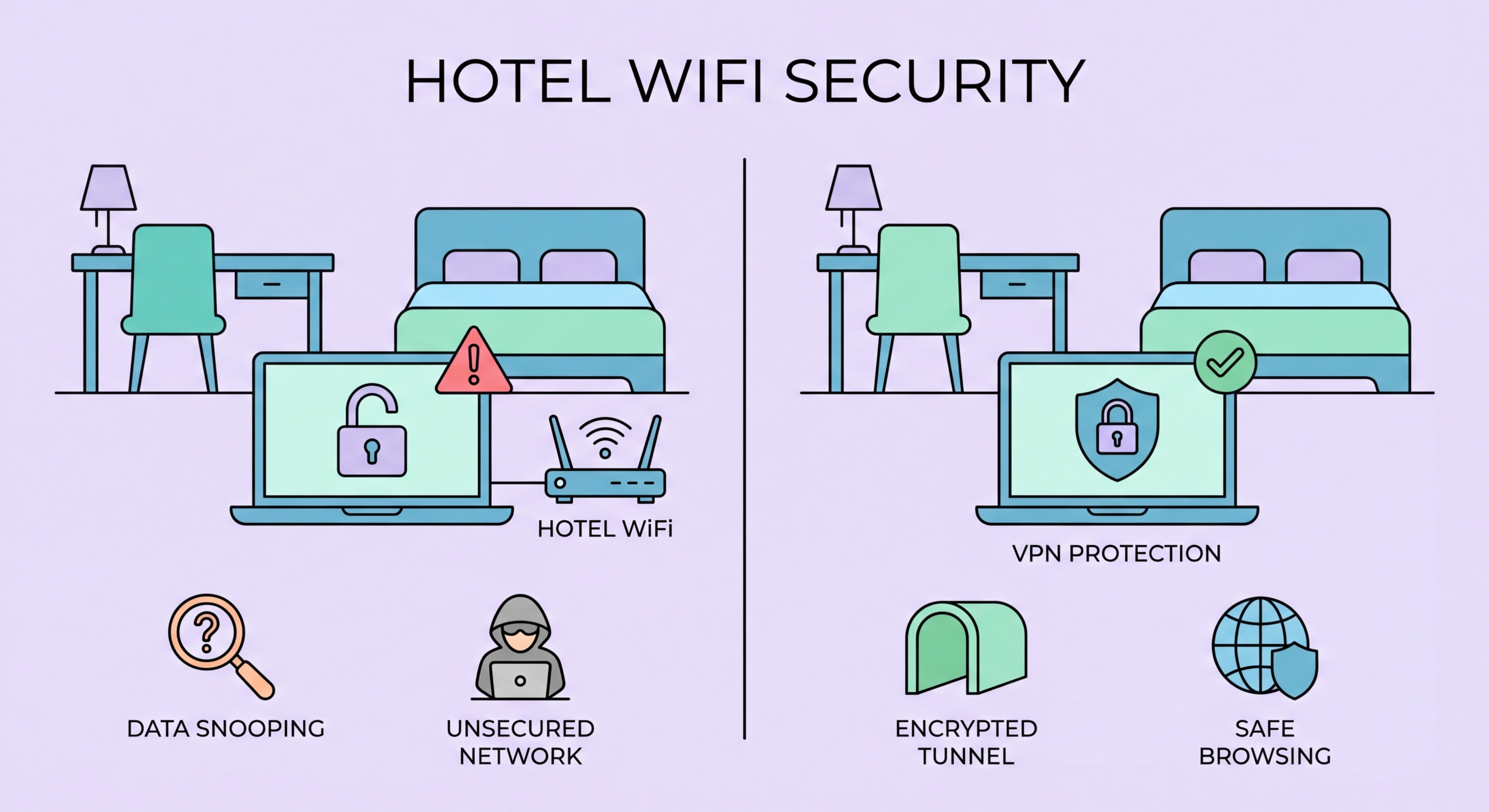
Less sophisticated attacks on hotel networks are far more common and do not require nation-state resources. Security researchers at conferences like DEF CON regularly demonstrate how easily an attacker can set up a man-in-the-middle position on a hotel network using commercial hardware costing less than HK$1,000. The combination of a laptop with two network adapters, readily available attack tools, and a hotel room provides everything needed to intercept the network traffic of other guests on the same network. This type of opportunistic financial crime is far more common than targeted espionage and affects business travellers and tourists alike.
- DarkHotel APT: Nation-state operation targeting executives at Asian luxury hotels via malicious software updates
- Asia focus: Hong Kong travel routes (Japan, Taiwan, China, Korea) were primary DarkHotel targets
- Booking system compromise: Sophisticated attacks combine network access with travel intelligence
- Low-cost attacks: MITM attacks on hotel networks achievable with HK$1,000 in consumer hardware
- Opportunistic crime: Financial credential theft on hotel networks is far more common than targeted espionage
- Software update caution: Never install software updates prompted through hotel WiFi captive portals
See how man-in-the-middle attacks work on hotel networks →