1ARP Explained
How ARP Works and Why It's Vulnerable to Spoofing
ARP (Address Resolution Protocol) is a network protocol that maps IP addresses to MAC (hardware) addresses on a local network. When your device wants to send data to another device on the same network — such as the WiFi router — it needs to know that device's MAC address. It sends an ARP broadcast asking "Who has IP address X? Tell me your MAC address." The device with that IP address responds with its MAC address, and your device caches this mapping in its ARP table for future use. This ARP table tells your device which MAC address to use when sending packets to a given IP address.
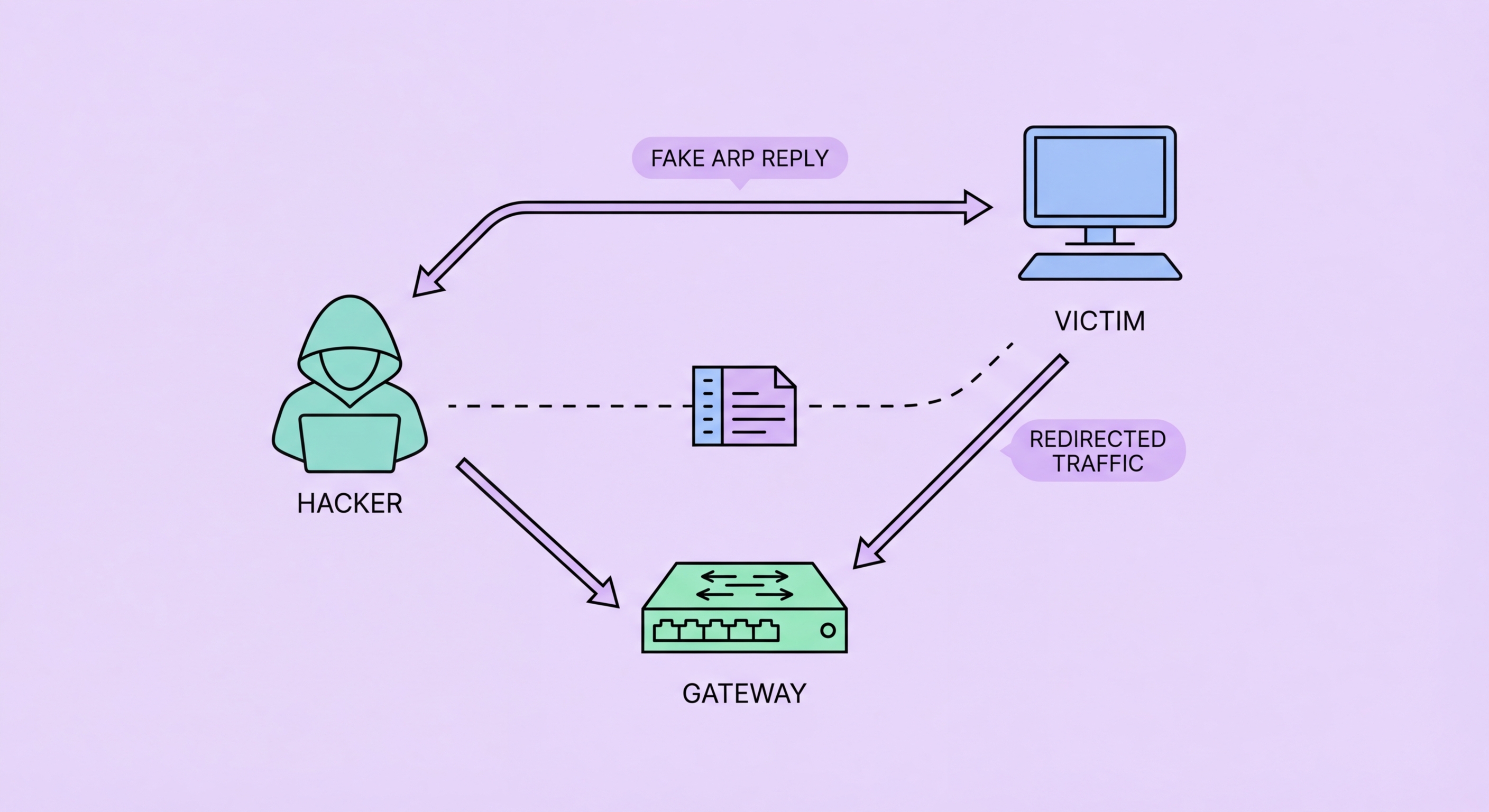
ARP was designed in 1982 with no authentication mechanism — any device on the network can send an ARP response claiming to be any IP address, without any verification. This is the fundamental vulnerability that ARP spoofing exploits. An attacker sends forged ARP response messages to your device, claiming that the router's IP address corresponds to the attacker's MAC address. Simultaneously, the attacker sends forged ARP responses to the router, claiming that your device's IP address corresponds to the attacker's MAC address. Once both your device and the router have updated their ARP caches with the attacker's MAC address, all traffic between your device and the router flows through the attacker's device instead of directly between the two endpoints. This is a classic man-in-the-middle position.
ARP spoofing is entirely passive to the victim — no action is required from you, no warning appears on your device, and internet connectivity continues working normally. The attack exploits a protocol-level weakness rather than any action or vulnerability on your part. The attacker simply needs to be on the same network segment as you — which on any public WiFi network anyone can join, they trivially are. Free tools like Arpspoof, Ettercap, and Cain and Abel automate ARP spoofing with minimal technical skill required. Bettercap, a modern, actively maintained framework, provides ARP spoofing combined with SSL stripping, HTTPS downgrade attacks, and credential capture in a single tool that runs on a laptop in any café or hotel.
- ARP function: Maps IP addresses to hardware MAC addresses on local networks
- Design weakness: ARP has no authentication — any device can claim to be any IP address
- ARP poisoning: Forged ARP responses update victim's and router's ARP caches with attacker's MAC
- MITM position: All victim-router traffic routes through attacker's device transparently
- No victim action needed: Attack is entirely passive — internet continues working normally
- Easy tooling: Bettercap, Arpspoof, Ettercap automate the attack with minimal skill required
What attackers do with a MITM position established via ARP spoofing →