1DNS Basics
What DNS Is and Why It Leaks on Public WiFi
DNS (Domain Name System) is the internet's address book. When you type "google.com" or "hsbc.com.hk" into your browser, your device first sends a DNS query to resolve that domain name to an IP address (the actual network address where the server is located). Without DNS resolution, your browser cannot connect to websites by name — only by IP address, which is impractical for regular use. By default, these DNS queries are sent using a simple, unencrypted UDP protocol that travels in plaintext across the network. Any device on the same network — or any network device between you and the DNS server — can read these plaintext queries and see exactly which domain names you are looking up.
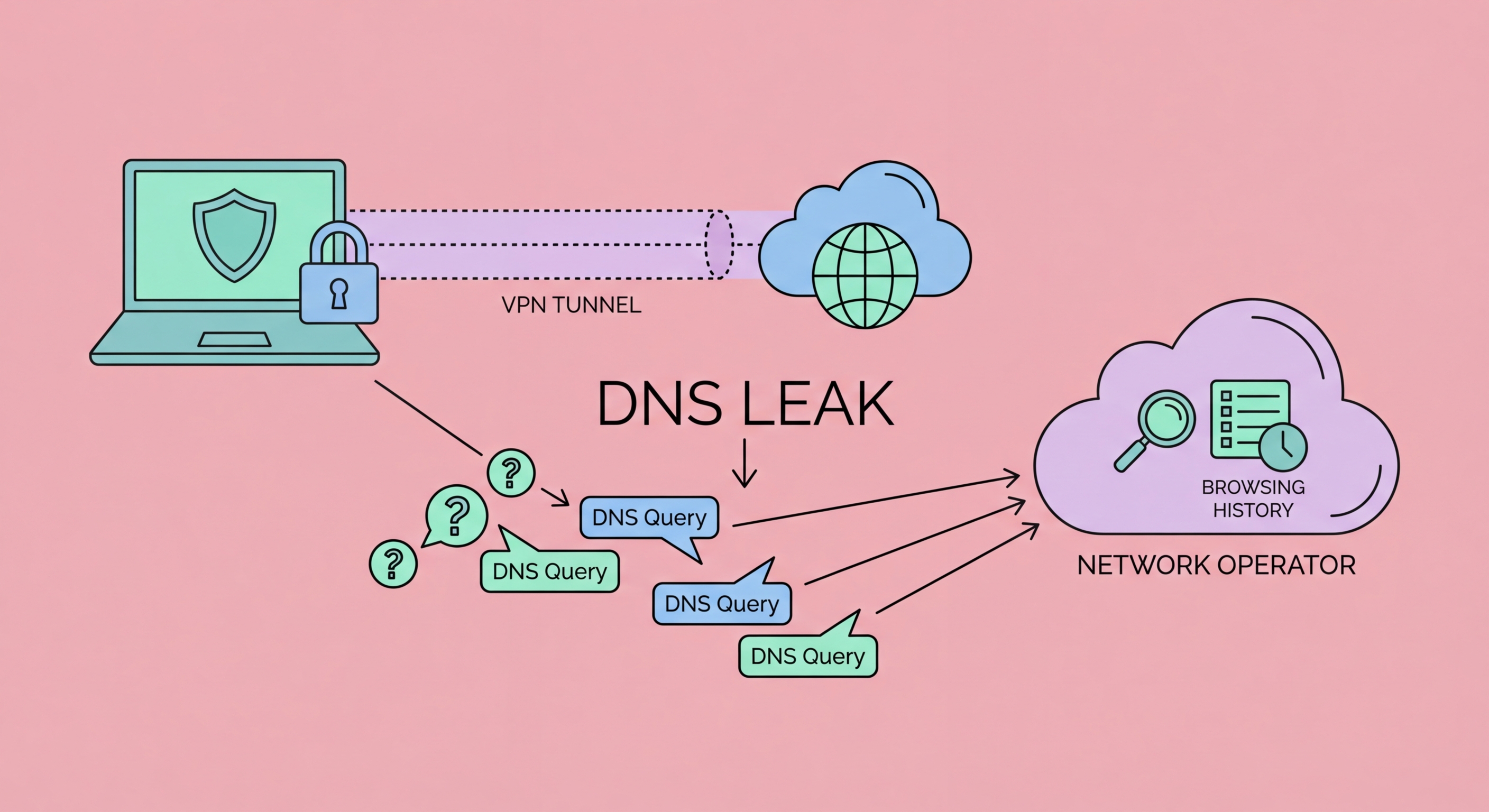
A DNS leak occurs when your DNS queries travel outside the encrypted protection of your VPN and are sent through your regular ISP or network DNS servers instead. This can happen for several reasons. When you connect to a public WiFi network, the captive portal or DHCP server may push its own DNS server configuration to your device, overriding your VPN's DNS settings. Some operating systems have a feature called "smart multi-homing" (Windows) or "prefer IPv6" (macOS) that may send DNS queries through multiple network interfaces simultaneously, with some queries bypassing the VPN tunnel. On mobile devices, the transition between WiFi and cellular data can briefly expose DNS queries outside the VPN. Even with a VPN nominally active, DNS queries may escape Does a VPN Work? Inside the Tunnel">the tunnel through these mechanisms.
The practical consequence of a DNS leak on public WiFi is that your browsing behaviour is visible to network monitors even though your connection uses HTTPS and a VPN. A network monitor logging DNS queries from your device's IP address on a hotel WiFi network can build a precise record of every website you visited: the banking site, the medical information site, the legal service, the competitor's website, the news sources consulted before a business decision. This metadata profile can be valuable for financial crime, corporate espionage, blackmail, and targeted social engineering attacks, even without any content being decrypted. DNS metadata is often more revealing than content, because it reflects all activity regardless of whether the activity itself involves transmitting sensitive content.
- DNS function: Translates domain names to IP addresses — all web browsing depends on DNS
- Plaintext by default: Standard DNS uses unencrypted UDP — visible to all devices on the network
- DNS leak: Queries escaping VPN tunnel and reaching network DNS servers in plaintext
- Causes: DHCP overrides, smart multi-homing, IPv6 bypasses, WiFi/cellular transitions
- Consequence: All visited domains visible to network monitors despite HTTPS and VPN use
- Intelligence value: DNS metadata reveals activity patterns valuable for espionage and targeted attacks
Why HTTPS alone doesn't prevent DNS visibility on public WiFi →