2Email Monitoring
Setting Up HIBP Email Monitoring and Understanding Notifications
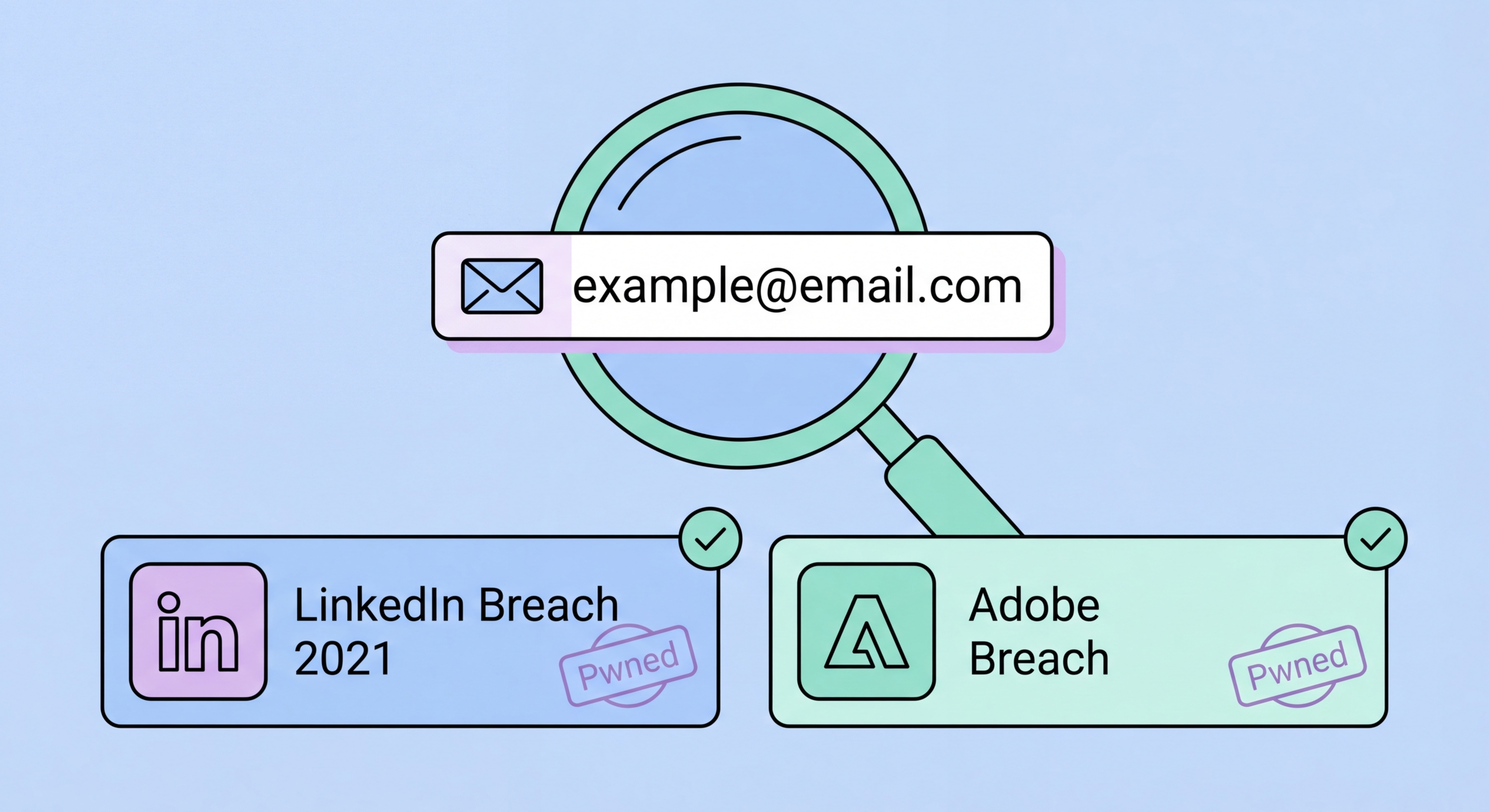
The email notification feature is the most valuable component of HIBP for ongoing protection. To register for notifications, go to haveibeenpwned.com, enter your email address, click "notify me of pwnage" (or go directly to haveibeenpwned.com/NotifyMe), and complete the email verification. Once verified, HIBP will email you whenever your address appears in a newly added breach dataset. These notifications arrive within hours of a breach being added to the HIBP database — significantly faster than relying on companies to self-report breaches (which, under Hong Kong's currently voluntary PDPO notification framework, may never happen). The notifications are free, permanent, and arrive at your registered address without any recurring subscription or expiry.
Register every email address you actively use — primary, secondary, work, and any address associated with important accounts. You'll need to complete a verification step for each address, which confirms you control the mailbox before HIBP begins sending breach notifications to it. After verification, each address is independently monitored. When a breach notification arrives, it includes the breach name, the date the breach occurred (if known), the date it was added to HIBP, and the data types exposed (email addresses, passwords, phone numbers, etc.). Read each notification carefully and take action within 24 hours — particularly for password exposures, where the window before automated credential stuffing attacks begin may be narrow.
HIBP notification emails are designed to be informative and actionable. Each email contains a direct link to the breach details page, which includes a full description of the service that was breached, how the breach occurred (if known), the scale of the breach, and a list of compromised data types. The breach details page also links to Have I Been Pwned's full database entry for that breach, where you can see example exposed data types (without any personal details) and advice specific to that breach. When you receive a HIBP notification for a breach involving a service you recognise, the response is clear: change your password immediately, check whether you used the same password elsewhere, and enable 2FA on the breached service if you haven't already.
- Register all email addresses: haveibeenpwned.com/NotifyMe — verify each address to confirm mailbox control before monitoring begins.
- Notifications arrive within hours: Much faster than company self-reporting — often the first indication a user receives that a service they use has been breached.
- Free and permanent: No subscription, no expiry — once registered, monitoring continues indefinitely without any recurring cost.
- Read the data types carefully: Email-only breaches require less urgency than password or identity data exposures — calibrate response to what was actually exposed.
- Act within 24 hours: For password exposures, change the affected password and audit reuse immediately — automated attacks exploit breached credentials rapidly.
- Check the breach details page: Each notification links to a full description of the breach — read it to understand the context and specific risks.
Full action plan for when HIBP notifications arrive →