3TOTP
TOTP: How Time-Based Codes Work and Why They Won
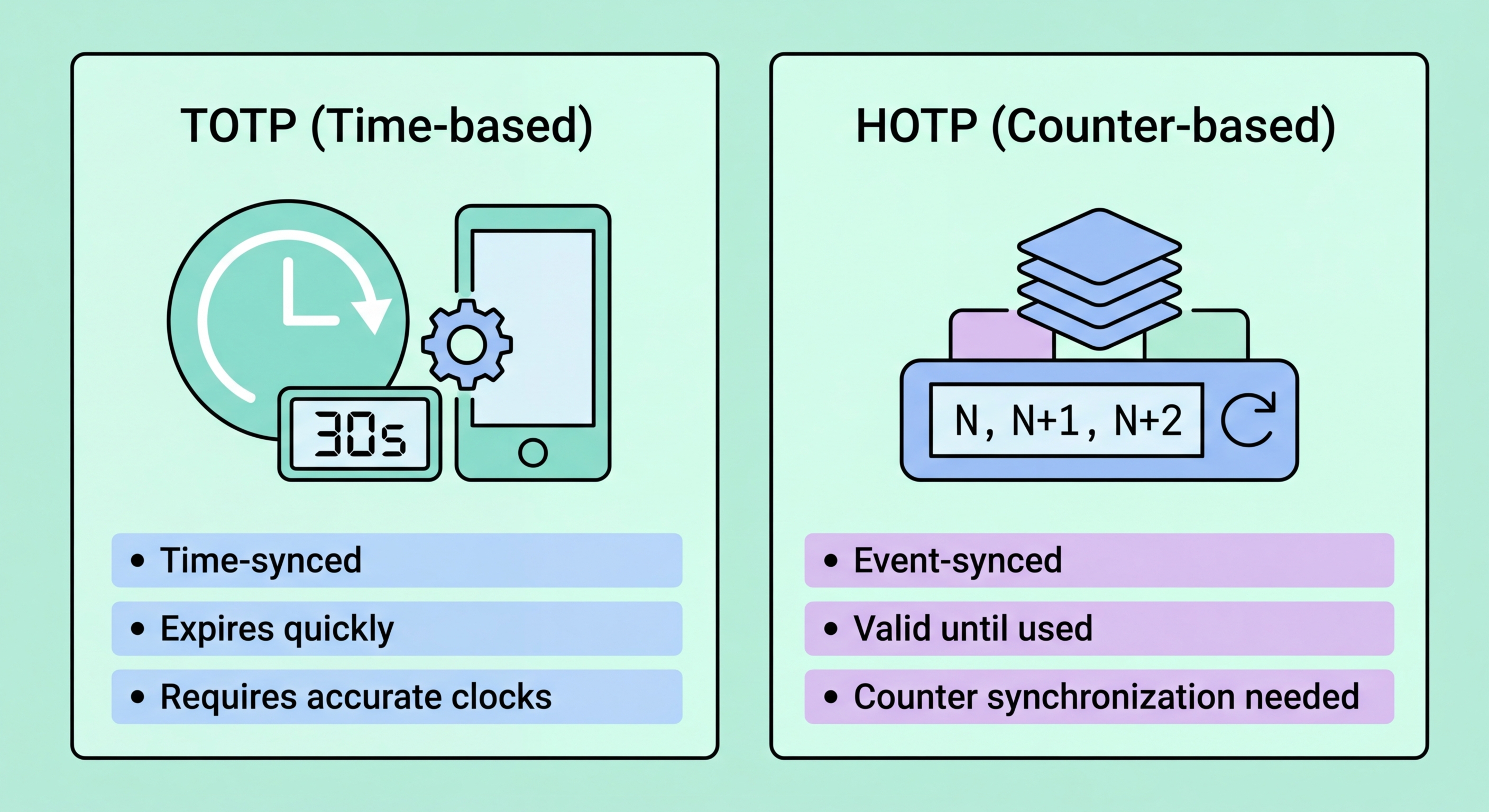
Time-based One-Time Password (TOTP) extends HOTP by replacing the counter with the current Unix timestamp divided into 30-second intervals. Instead of HMAC-SHA1(secret, counter), the calculation is HMAC-SHA1(secret, floor(time/30)). This means the code changes automatically every 30 seconds, with no user action required, and both the authenticator app and the server can independently calculate the current valid code as long as their clocks are reasonably synchronised.
The 30-second window is a pragmatic balance between security and usability. A shorter window would provide slightly better security but cause too many authentication failures due to the few seconds of typing and network delay between code generation and server verification. A longer window would make codes more predictable and expose them to interception attacks over longer periods. Most TOTP implementations accept codes from the current window plus the immediately preceding one, providing roughly 60 seconds of tolerance for slow typists and high-latency connections.
TOTP dominates consumer 2FA today because it combines good security with excellent usability. The code changes automatically, there is no counter synchronisation problem, and the 30-second expiry means intercepted codes are quickly useless. All major authenticator apps (Google Authenticator, Authy, Microsoft Authenticator, Raivo) implement TOTP. All major services (Google, Microsoft, Facebook, Twitter, GitHub) support TOTP enrollment via the standard QR code setup flow. for Hong Kong Businesses">Kong Businesses: Implementation Guide">for Hong Kong Online Banking: What You Need to Know">For Hong Kong users, TOTP via an authenticator app is the practical recommendation for the vast majority of 2FA use cases.
- Time-based: Counter is replaced by current Unix timestamp divided into 30-second slots
- Automatic rotation: Code changes every 30 seconds without any user action
- Clock sync required: Both device and server clocks must be within ~30 seconds of each other
- Acceptance window: Most servers accept current and immediately preceding code (±30 seconds)
- Short validity: 30-second expiry makes intercepted codes quickly useless
- Universal support: All major authenticator apps and services implement standard TOTP
Compare the best TOTP authenticator apps for HK users →