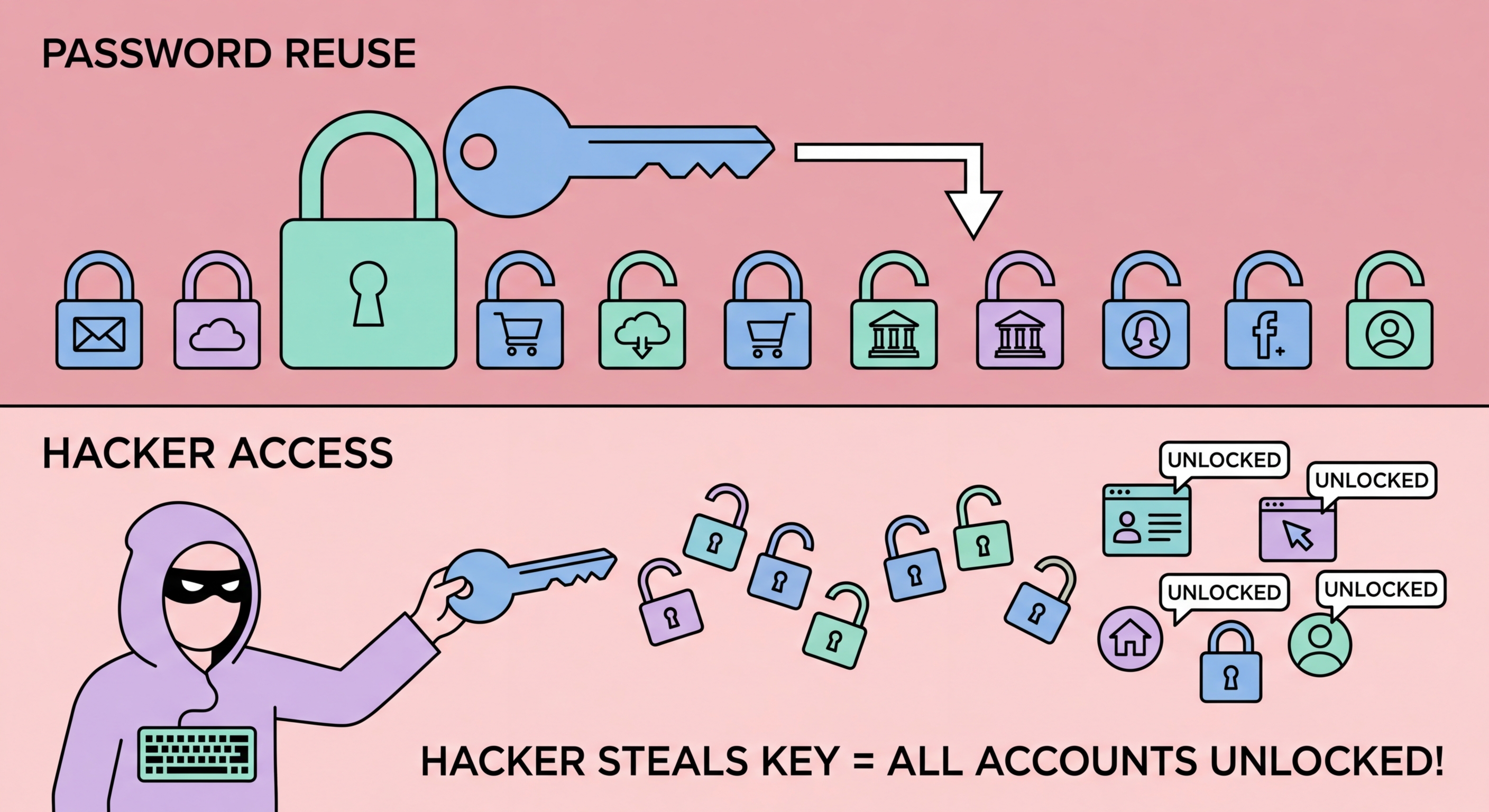
Why Password Reuse Is One of the Biggest Security Risks
Reusing passwords turns every data breach into a potential takeover of all your accounts. Understand why credential stuffing is so dangerous and how to protect yourself.
Reusing passwords turns every data breach into a potential takeover of all your accounts. Understand why credential stuffing is so dangerous and how to protect yourself.
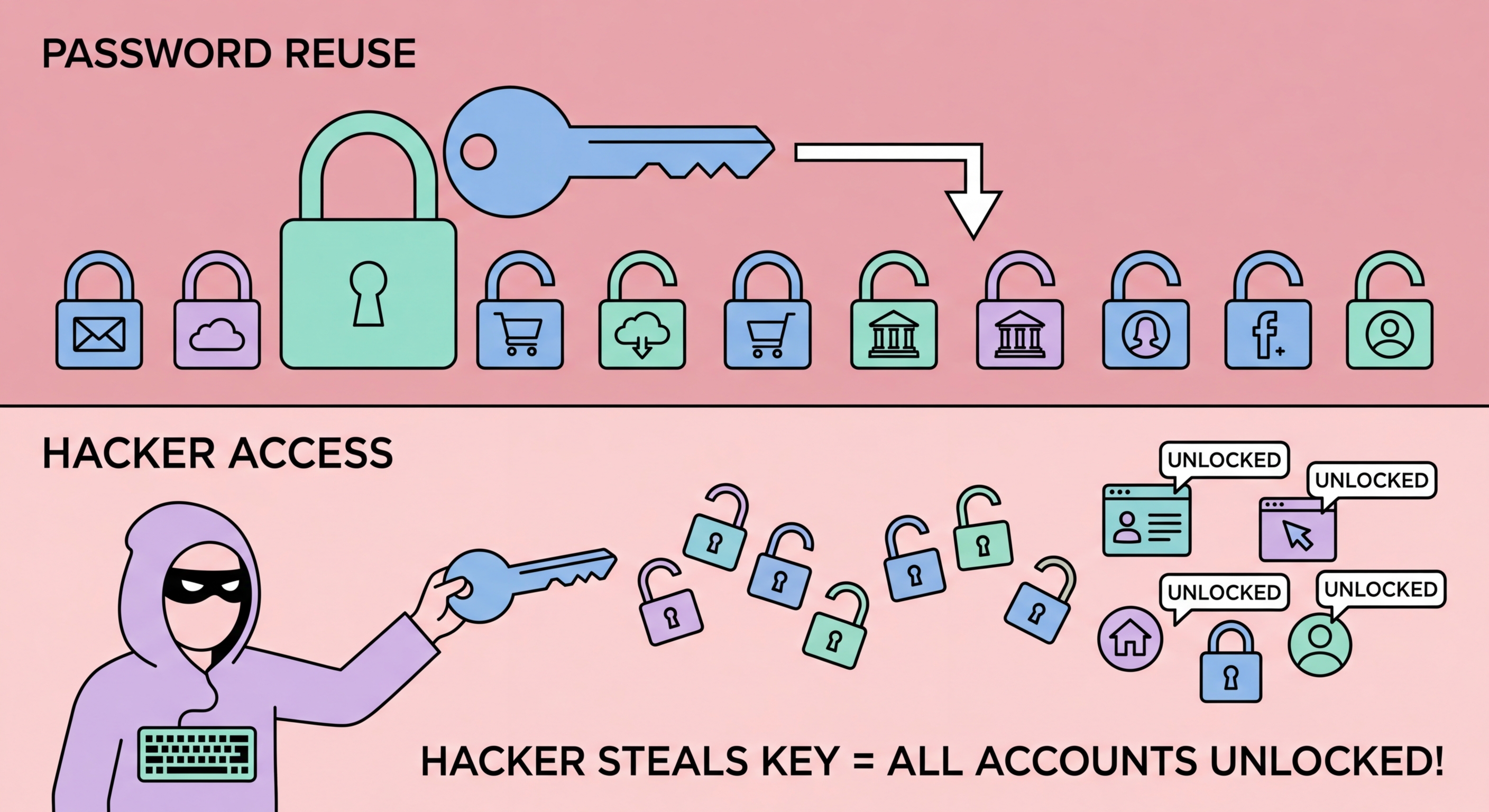
Research consistently shows that password reuse is extremely widespread. Studies of leaked breach data indicate that the majority of people reuse the same password across multiple accounts, with many users having just two to five passwords they rotate across all their accounts. This behaviour is entirely understandable — maintaining dozens of unique passwords is genuinely difficult without a dedicated tool — but it creates an enormous security risk at scale.
The problem is compounded by the frequency and scale of data breaches. Thousands of organisations are compromised every year, ranging from minor forums and e-commerce sites to major corporations and government agencies. When any one of these organisations is breached and user credentials are stolen, those credentials are typically put to immediate use in automated attacks against other, higher-value services. Your password for a relatively minor site you barely remember creating an account on could be the key that unlocks your banking account if you used the same password for both.
Studies of reuse patterns in leaked data reveal another sobering reality: people do not tend to reuse passwords randomly across accounts. They tend to use their "important" password for the sites they care about most. This means that when a breach occurs, the password exposed is often the one that was also used for email, banking, or other critical services — the exact accounts where the damage from compromise would be greatest.

The most damaging aspect of password reuse is the cascade effect: a single compromised credential can unlock access to multiple accounts simultaneously. Consider a typical scenario: you create an account on a small online shopping site and use the same email and password as your Gmail account. The shopping site is breached six months later. Attackers run the leaked credentials through automated tools and successfully log into your Gmail account. From Gmail, they can reset passwords for every other account linked to that email address — your banking app, your social media, your cloud storage. Within minutes, a breach on an unimportant site becomes a full account takeover.
Email accounts are particularly dangerous as reuse targets because they serve as password recovery hubs for most other services. Once an attacker has your email credentials, they do not need to know any other passwords — they can use "Forgot Password" to reset every other account. This is why your email account password should be the most carefully protected credential you have — absolutely unique, very long, protected by 2FA, and not reused anywhere else under any circumstances.
Social media account takeovers are another common cascade outcome. Compromised Instagram or Facebook accounts are used to send convincing scam messages to all of the victim's contacts, dramatically increasing the reach and success rate of subsequent scams. The attacker appears to be a trusted friend or family member, making investment scam approaches or request-for-money messages far more likely to succeed. In Hong Kong, where WhatsApp is nearly universally used, a compromised WhatsApp account becomes a tool for scamming everyone in the victim's contact list.

Password reuse is not the result of carelessness but of a genuine cognitive limitation: the human brain is simply not designed to reliably store and recall dozens of arbitrary, complex character strings. Research in human memory suggests people can reliably maintain four to seven distinct items in working memory. Asking individuals to maintain 100+ unique complex passwords without assistance is asking the impossible, which is why even security-conscious people fall back on a small set of memorised passwords.
Partial reuse strategies — where people add a suffix or prefix based on the site name — are a common attempt to solve this problem without a password manager. "Netflix123", "Facebook123", "Banking123" might seem like distinct passwords but represent a pattern that is trivially detectable in breach data and can be automatically extended by attackers to other services. These "keyboard walk" and site-specific suffix patterns are well-documented in cracking research and provide minimal additional protection over simple reuse.
The only sustainable solution to password reuse at scale is a password manager. It removes the memory burden entirely: you generate a unique random password for each service, save it to the vault, and never need to remember it. The manager handles all recall via auto-fill. This makes using unique 20-character random passwords for every account no more cognitively demanding than using the same simple password everywhere — which is exactly what is needed to permanently break the reuse habit.

While unique passwords are the primary defence against credential stuffing, two-factor authentication (2FA) provides an essential backstop for the scenario where a credential is exposed. With 2FA enabled, an attacker who successfully obtains your email and password still cannot access your account without also having your second factor — typically a time-based one-time password (TOTP) from an authenticator app, or a hardware security key. This completely neutralises credential stuffing attacks against 2FA-protected accounts.
Not all 2FA is equal in its protection against sophisticated attacks. SMS-based 2FA (receiving a text message code) is the most widely deployed but also the most vulnerable — SIM swapping attacks can redirect your phone number to an attacker's device, allowing them to receive your SMS codes. TOTP authenticator apps (Google Authenticator, Authy, Aegis) are significantly more resistant to remote attacks. Hardware security keys (YubiKey, Google Titan) provide the strongest protection, requiring physical possession of the device for every login.
For Hong Kong users, enabling 2FA on email accounts, banking apps, government services like eTax, PayMe, and all major social media platforms should be treated as a priority action — ideally completed before working through the transition to unique passwords, since 2FA can protect existing weak or reused passwords while the transition is in progress. Many HK banks now provide their own authenticator apps or hardware tokens for corporate accounts — check with your bank about the options available for your account type.
