How Hackers Crack Passwords (And How to Stop Them)
From brute force attacks to credential stuffing, understanding how attackers crack passwords is the first step to building defences that actually work.
From brute force attacks to credential stuffing, understanding how attackers crack passwords is the first step to building defences that actually work.
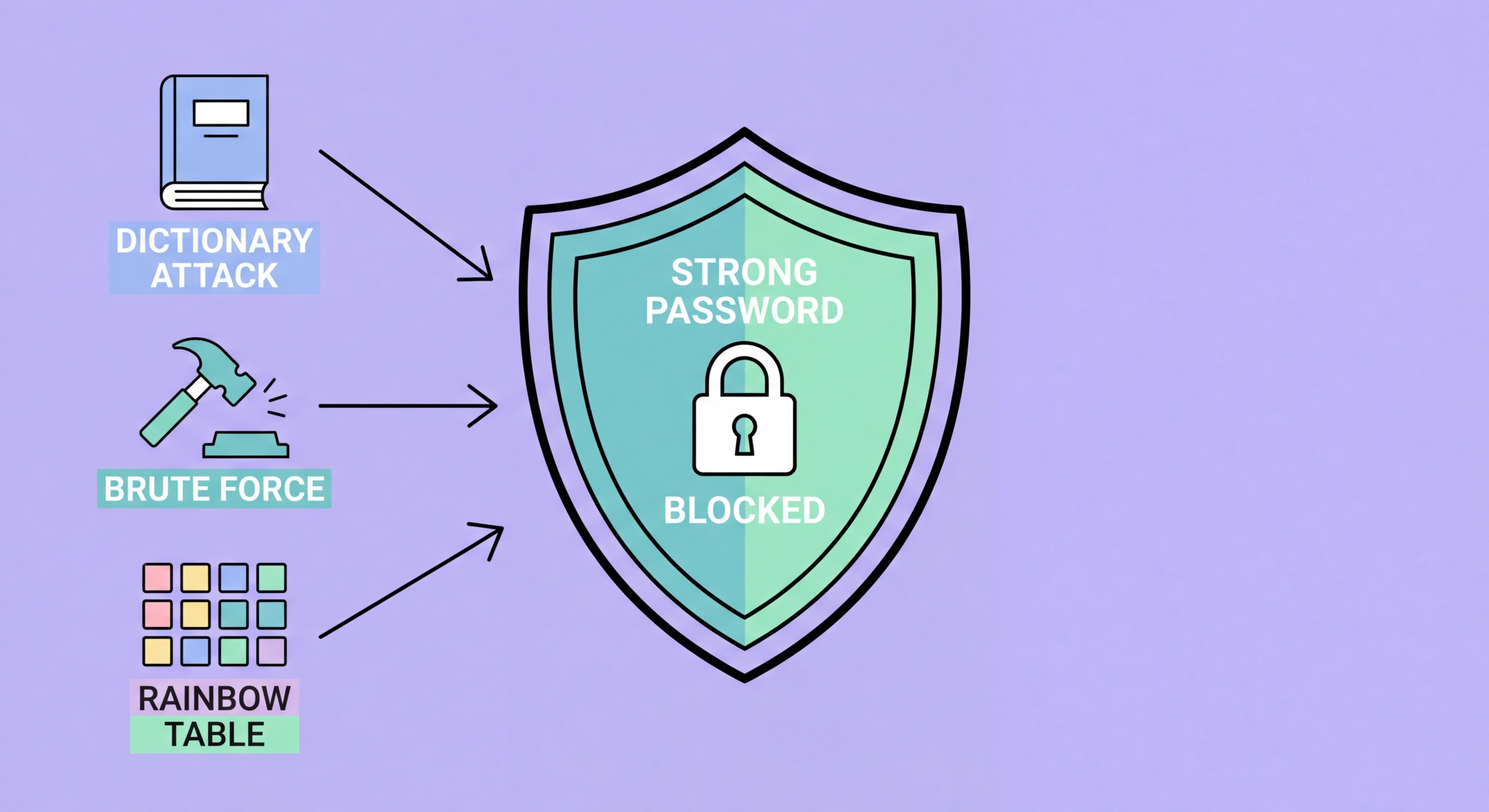
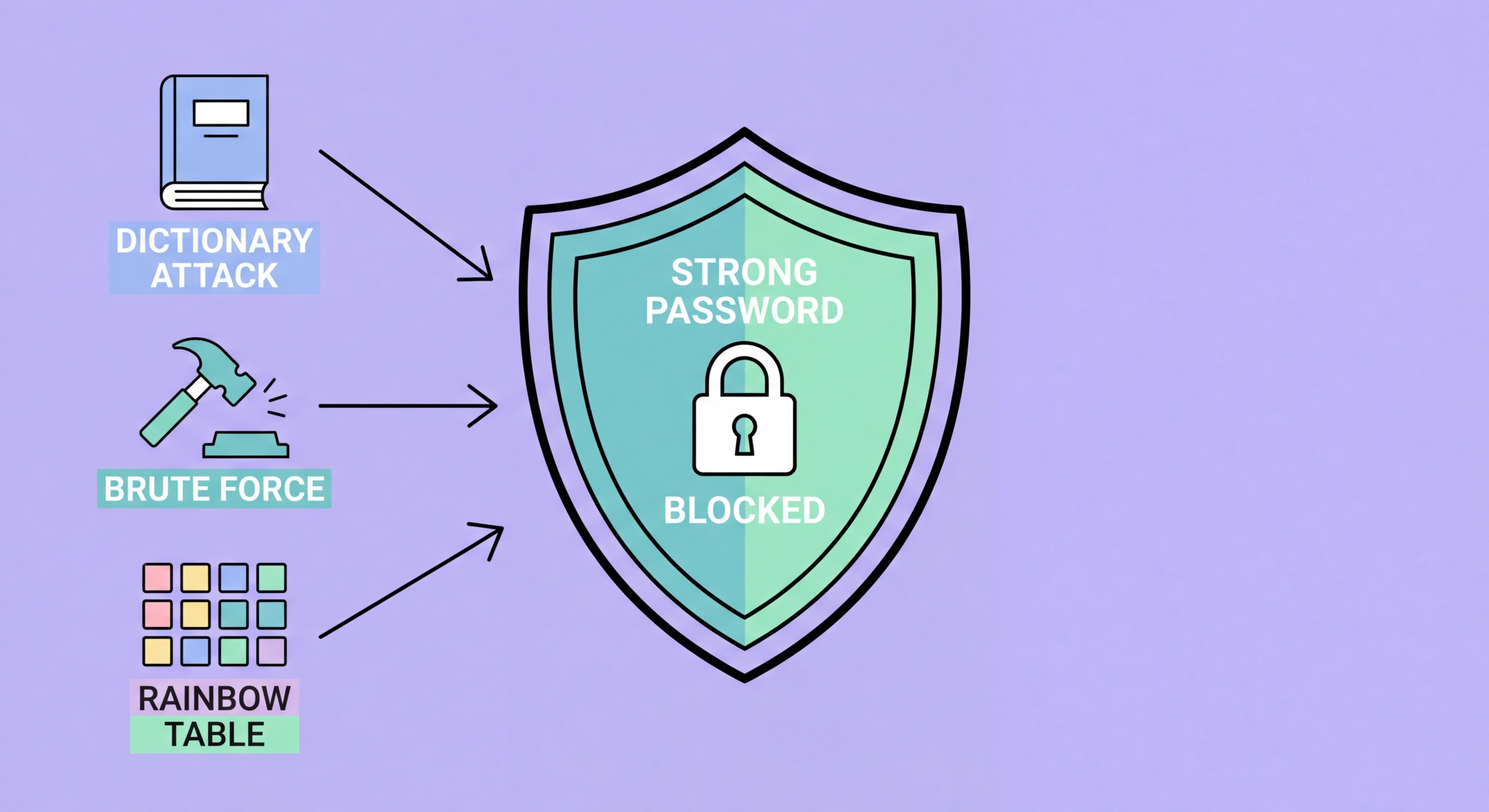
A brute force attack is the most basic form of password cracking: systematically trying every possible combination of characters until the correct password is found. For a modern GPU-accelerated cracking rig, testing billions of combinations per second is routine. Against common MD5 hash functions (unfortunately still used by some services), a single GPU can test over 10 billion passwords per second. This makes any password under 10-12 characters potentially crackable within hours regardless of complexity, given the hash.
Dictionary attacks are more efficient than pure brute force: instead of trying every character combination, they start with lists of known passwords, common words, and previously cracked passwords. The "Rockyou2024" leak contains over 10 billion real-world passwords collected from breach data, and it is freely available as a cracking dictionary. Dictionary attacks are often combined with rule engines that apply transformations: capitalising the first letter, appending numbers, substituting '@' for 'a', adding '!' at the end. "Summer2025!", "Password123", and "Liverpool1" are all efficiently covered by these combined dictionary-and-rule attacks.
Hybrid attacks combine dictionary and brute force approaches: take dictionary words, apply rule transformations, then append brute-forced suffixes. This approach efficiently covers the huge number of human-created passwords that follow predictable patterns while not being limited to only exact dictionary matches. Modern cracking tools like Hashcat and John the Ripper support all these approaches and are freely available, meaning the barrier to sophisticated password cracking is extremely low.

Credential stuffing is the most prevalent large-scale attack method against online accounts today. Unlike brute force or dictionary attacks, it does not try to crack a password — it uses already-known username/password pairs stolen from previous breaches. With over 15 billion credentials available in breach databases, attackers use automated tools to test these pairs against hundreds of popular sites simultaneously. Because so many people reuse passwords, even a small percentage success rate across billions of tests results in millions of successfully compromised accounts.
The scale of credential stuffing operations is staggering. Specialised tools can test credentials against multiple sites simultaneously at high speed, and commercial services on dark web markets offer "checking" services where someone supplies a list of credentials and the service tests them against specified targets. Reports from major retailers and financial institutions document millions of credential stuffing attempts per day. The only effective defence is unique passwords per site — if your credentials are stolen from one service but every other service has a different password, the stuffing attack cannot succeed elsewhere.
Rainbow tables are precomputed lookup tables that allow rapid reversal of password hashes. Rather than cracking each hash individually, an attacker with a rainbow table can look up a hash and immediately find the corresponding password. This approach is extremely fast for common passwords — far faster than real-time cracking. It is defeated at the service level by password salting (adding a unique random string to each password before hashing), which is why modern well-designed systems store salted hashes. However, older or poorly designed systems that store unsalted hashes are vulnerable to instant rainbow table lookups.

Not all password compromises involve technical cracking. Phishing attacks — fraudulent websites or emails designed to trick victims into entering their credentials — are responsible for a large proportion of account compromises and require no cryptographic cracking at all. The victim simply types their real password into a fake site designed to look like their bank, their Google login, or their workplace system. These attacks are particularly effective because they bypass all the protections that strong passwords provide — a 30-character random password is just as easily stolen via phishing as a 6-character one.
Keyloggers — malware that records every keystroke — are another non-cracking method that defeats even the strongest passwords. If malware is installed on a device, it can capture passwords as they are typed, making strong password creation irrelevant. Keyloggers are often installed via email attachments, malicious browser extensions, or pirated software. Hardware keyloggers exist as physical devices inserted between keyboards and computers. The defence against both software and hardware keyloggers includes using a password manager (which auto-fills rather than requiring typing), keeping software updated, and using reputable endpoint security software.
OSINT-based personalised attacks target specific individuals using publicly available information. Attackers research their target's social media, published data, and easily discoverable personal information to build lists of likely passwords — birthdays, names, sports teams, anniversaries, pets. These attacks are effective against anyone who uses personally meaningful information in their passwords, regardless of password length. The defence is using truly random passwords with no personal connection — which again points toward password manager-generated credentials.

An effective defence against password cracking attacks is layered: no single measure defeats all attack types, but combining strong passwords, unique credentials, and multi-factor authentication creates a system where defeating any one layer does not provide full account access. This defence-in-depth approach is the foundation of practical password security.
The first layer — long, random, unique passwords generated by a password manager — defeats brute force, dictionary, rule-based, and credential stuffing attacks simultaneously. A 20-character random password takes billions of years to brute force and is not in any dictionary. Because it is unique per site, stealing it from one service gains the attacker nothing on any other service. The second layer — two-factor authentication — defeats phishing attacks. Even if an attacker tricks you into entering your password on a fake site, they cannot access your account without also having your physical 2FA device.
The third layer — device and endpoint security — defeats keyloggers and malware. Keeping your operating system and applications updated, avoiding pirated software, using reputable endpoint security software, and being cautious about browser extensions all reduce the risk of malware that could capture credentials before the manager's auto-fill even operates. Together, these three layers — strong unique passwords, 2FA, and endpoint security — provide protection against the full spectrum of password attack methods.
