3Individual Wire Fraud
Wire Transfer Fraud Targeting Hong Kong Individuals
While BEC primarily targets businesses, individuals in Hong Kong are targeted by wire transfer fraud through several distinct mechanisms. Real estate transaction fraud is particularly costly — fraudsters monitor property transactions, then send conveyancing solicitors or estate agents forged instructions or impersonated communications diverting deposit payments or completion funds to fraudster accounts. Given that Hong Kong property transaction amounts are among the highest globally, a single successful fraud can result in losses of millions of HK dollars.
Impersonation of government authorities is another prevalent individual wire fraud. Fraudsters posing as HKPF officers, Customs officials, IRD representatives, or court bailiffs claim the victim is under investigation for money laundering, tax evasion, or other serious offences. They instruct victims to wire funds to a "safe government escrow account" while the investigation proceeds or to avoid asset freezing. These calls often use authentic-sounding terminology and are backed by fake warrant numbers, case references, and officer badge numbers. The genuine authorities in Hong Kong do not conduct investigations this way — any instruction to wire money to resolve a government investigation is fraud without exception.
Romance fraud leading to wire transfers is also significant in Hong Kong. After cultivating an online relationship over months, fraudsters claim a personal emergency — medical, legal, or financial — requiring an urgent wire transfer. The victim, believing they have a genuine relationship with the requester, complies. Unlike the investment variant (pig butchering), pure romance fraud focuses on extracting wire transfers for supposed personal emergencies rather than investment returns. The emotional investment created by the scam ↗mer makes victims reluctant to believe the relationship was constructed entirely for financial gain.
- Real estate fraud awareness: Verify all wire transfer instructions for property transactions by calling your solicitor's published number — not a number provided in the instruction
- Government agencies never demand immediate transfers: Police, IRD, Customs, and courts will never instruct you to wire money to resolve investigations — any such demand is fraud
- Romance fraud vigilance: Any online contact requesting financial assistance via wire transfer — regardless of the relationship cultivated — requires extreme scepticism and third-party advice
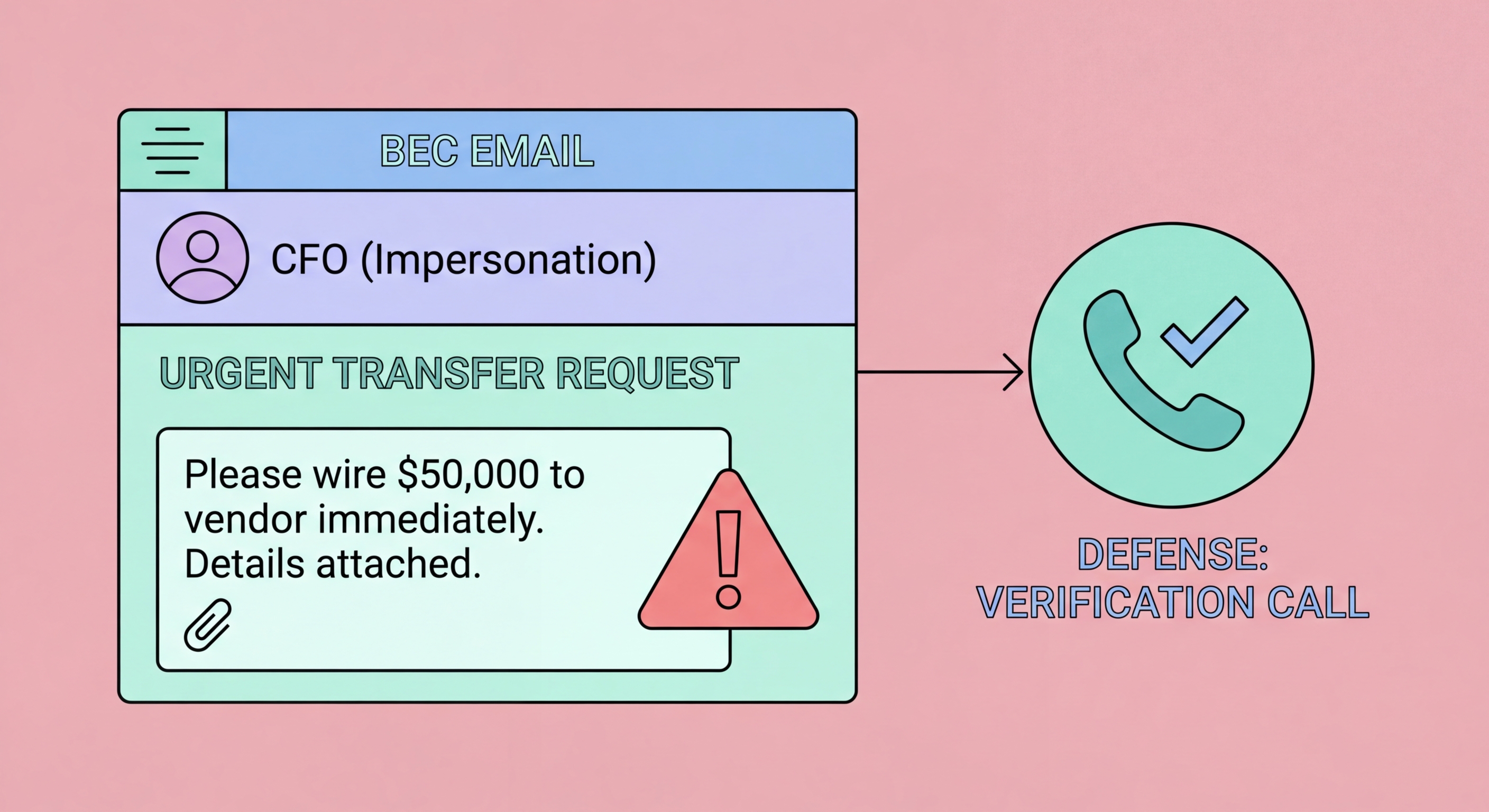
- Independent verification of instructions: Verify any wire transfer instruction involving new or changed banking details by calling the instructing party on a separately verified number
- Cooling-off period for large transfers: Implement a personal rule: sleep on any wire transfer decision above a self-defined threshold — urgency is a fraud signal
- Anti-Scam Helpline 18222: Call before executing any wire transfer that was prompted by unexpected contact or unusual circumstances