3Legal Status in HK
Tor's Legal Status in Hong Kong and Legitimate Uses
Using Tor Browser in Hong Kong is entirely legal. There is no Hong Kong legislation that prohibits using anonymisation software, accessing .onion addresses, or routing internet traffic through the Tor network. What is illegal is not the tool but the activity — the Computer Crimes Ordinance (Cap. 200), the Theft Ordinance, and the Organised and Serious Crimes Ordinance apply to criminal activities whether they are conducted using Tor, a regular browser, or any other means. The same illegal activities (fraud, trafficking, distributing child sexual abuse material, drug sales) are illegal regardless of the technical means used. Conversely, legal activities — journalism, research, privacy-conscious browsing, reading content not available due to geo-restrictions — remain legal regardless of whether you use Tor to access them.
Tor has significant legitimate uses that are relevant to Hong Kong residents and professionals. Journalists and sources communicating sensitive information benefit from Tor's anonymity protections — the Tor Project maintains a SecureDrop directory of news organisations (including international outlets covering Hong Kong) that provide .onion submission channels for whistleblowers and sources. Legal professionals handling sensitive client communications, researchers studying cybersecurity threats (including dark web markets and criminal forums, for the purpose of understanding and defending against them), privacy advocates testing the effectiveness of tracking and surveillance technologies, and ordinary citizens who prefer stronger privacy protections for their general browsing all have legitimate reasons to use Tor. The BBC, ProPublica, New York Times, and many other reputable news organisations maintain .onion versions of their websites specifically to improve accessibility in regions with internet restrictions.
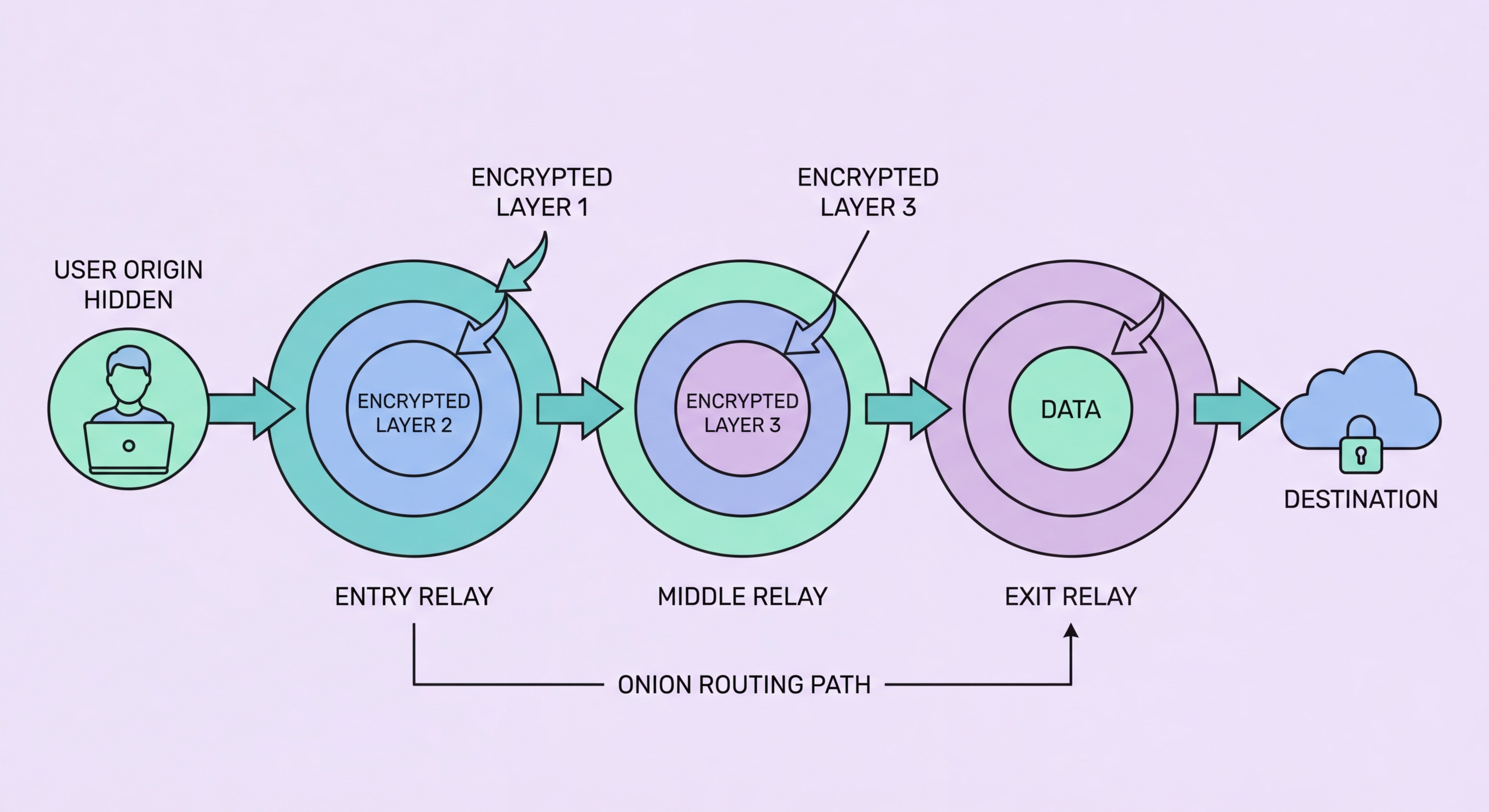
Cybersecurity researchers and dark web monitoring services use Tor professionally to crawl dark web markets and forums for intelligence about stolen data, emerging threats, and criminal tradecraft. This is the legitimate activity that enables the monitoring services discussed throughout this guide — they use Tor to access the same platforms where stolen data is traded, scanning for their clients' information without engaging in any criminal activity themselves. For ordinary Hong Kong residents, the most relevant use case is not accessing the dark web directly but understanding that the monitoring services they use to protect their data do this work on their behalf. You don't need to use Tor yourself to benefit from dark web intelligence — dark web monitoring services handle the technical access while you simply receive the alerts.
- Legal in Hong Kong: Using Tor Browser is not prohibited by any HK legislation — what matters is what you do with it, not the tool itself.
- Whistleblower channels: Many media organisations maintain .onion SecureDrop instances for source protection — relevant for journalists and sources in Hong Kong.
- Research and security: Cybersecurity professionals use Tor to study dark web threats — the same infrastructure that monitoring services use to detect your stolen data.
- Privacy-conscious browsing: Tor is a legitimate option for everyday browsing if you want stronger privacy protections than a VPN provides, at the cost of slower speeds.
- Tor is slow: The multi-relay routing adds latency — expect slower page loads; Tor is not appropriate for video streaming, gaming, or high-bandwidth applications.
- You don't need Tor to benefit from dark web monitoring: Monitoring services access the dark web on your behalf — you receive alerts without needing to use Tor yourself.
Check your dark web exposure without using Tor yourself →