1What Is Clone Phishing
What Is Clone Phishing and How Does It Work?
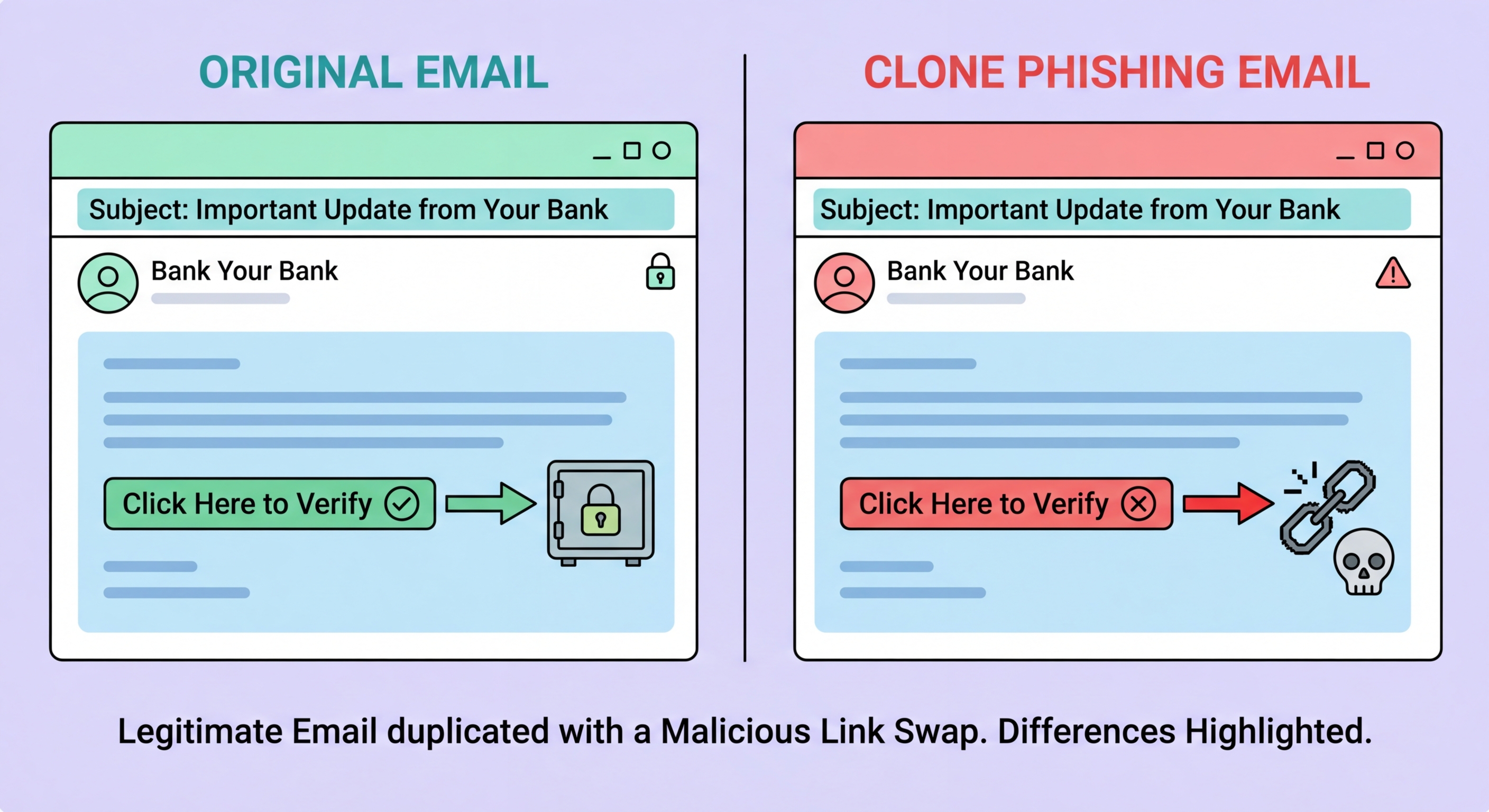
Clone phishing is a specific phishing technique in which an attacker creates a near-perfect duplicate of a legitimate email that the target has previously received. The attacker obtains a copy of the original email — through network interception, a compromised account, or by receiving the original communication themselves if it was a mass email — and then creates a new version that is nearly identical in appearance, content, and formatting. The only differences are that the links or attachments in the cloned message have been replaced with malicious versions, and the sender address is spoofed or uses a lookalike domain. The cloned email is then sent to the target, often with a note suggesting it is a "resend" of the original due to a technical error or to add updated information.
The effectiveness of clone phishing stems from the victim's prior positive experience with the genuine email. When you have previously received a legitimate notification from your bank, a service provider, or a business partner, and you receive what appears to be the same email — same layout, same language, same apparent sender, referencing the same subject matter — the likelihood that you will scrutinise it carefully is lower than it would be for an unfamiliar message. The psychological mechanism is pattern recognition: you recognise the email as something you have seen and trusted before, and the recognition itself suppresses the critical evaluation you would apply to a new communication. This makes clone phishing particularly effective against regular business communications like invoice notifications, delivery confirmations, and software update alerts.
Clone phishing is used both as a standalone attack and as a follow-up to a successful account compromise. In the standalone variant, the attacker intercepts or obtains a copy of a legitimate email and creates a fraudulent clone. In the post-compromise variant, the attacker has access to a victim's compromised inbox and uses the actual email history to create clones precisely tailored to the victim's existing relationships and communication patterns — making the attack significantly more convincing because the email genuinely references real prior conversations and relationships. This latter variant is technically a form of Hong Kong: Prevention Guide">Business Email Compromise and is increasingly common as email account compromise has become more prevalent through credential phishing and password reuse exploitation.
- Core technique: Duplicate of a real previously received email, with links/attachments replaced with malicious versions
- Source of original email: Network interception, compromised account, or receipt of the original mass communication
- Prior trust exploitation: Pattern recognition from previous legitimate email suppresses scrutiny of the clone
- "Resend" framing: Technical error or updated information explanation for why you are receiving it again
- Post-compromise variant: Attacker with inbox access creates clones tailored to actual email history and relationships
- Common targets: Invoice notifications, delivery confirmations, software update alerts, service renewal notices
How clone phishing fits into the broader phishing taxonomy →