3Migrating Away from SMS 2FA
Migrating from SMS 2FA to Authenticator Apps
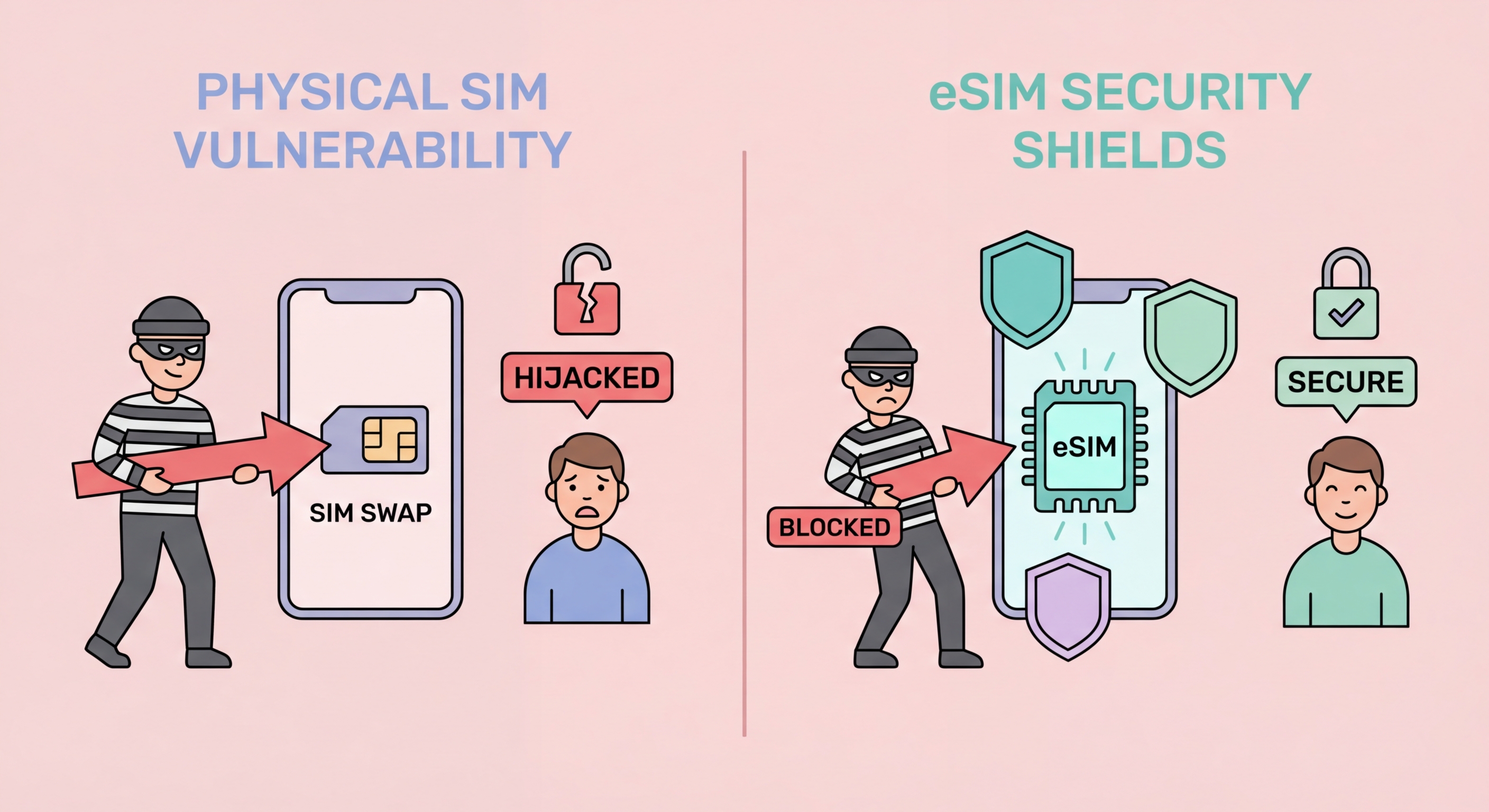
The most durable long-term protection against SIM swap impact is migrating your critical accounts away from SMS-based 2FA to authenticator app-based 2FA or hardware security keys. As long as your phone number is used as an authentication factor for critical accounts, number hijacking through SIM swap or porting remains a meaningful attack vector regardless of how well you protect your carrier account — a sufficiently motivated attacker may still find ways to manipulate carrier processes. Authenticator apps (Google Authenticator, Authy, Microsoft Authenticator) generate time-based one-time passwords (TOTP) that are generated locally on your device and are not transmitted through the phone network — a SIM swap does not give the attacker access to TOTP codes because those codes are generated by software on your specific device, not delivered by SMS to a number.
To migrate a critical account from SMS 2FA to authenticator app 2FA: log into the account, navigate to Security or Two-Factor Authentication settings, select "Authenticator App" or "TOTP" as the 2FA method, scan the QR code displayed with your authenticator app, enter the 6-digit code generated by the app to verify the setup, and save the backup codes provided. Priority accounts to migrate in Hong Kong: email (Gmail, Outlook — the master account for password recovery), banking apps (HSBC, Hang Seng, BOCHK, Standard Chartered — check if each supports authenticator app vs SMS only), cryptocurrency exchange accounts (Binance, OKX, HashKey — these almost universally support TOTP authenticator), social media accounts (Instagram, Facebook, Twitter/X — all support authenticator app 2FA), and password manager accounts.
Some Hong Kong banking apps do not offer authenticator app 2FA as an option — they require SMS OTP for transaction verification as a regulatory compliance measure under HKMA guidance. For these accounts, the pragmatic approach is to maximise carrier account protection (carrier PIN, 2FA on carrier account) and accept the residual SMS dependency while it cannot be eliminated. Hardware security keys (YubiKey, Google Titan) provide the strongest possible 2FA protection for accounts that support them — resistant to phishing, SIM swap, and malware — and are increasingly supported by major platforms. For Hong Kong users with high-value accounts or elevated threat profiles (executives, crypto holders), hardware keys for email and cryptocurrency accounts provide security that exceeds what authenticator apps can offer.
- TOTP authenticator codes are device-generated: SIM swap cannot intercept authenticator codes — generated locally, not delivered via SMS.
- Migrate email first: Email is the master account for password recovery — securing it with authenticator app is the highest-priority migration.
- Cryptocurrency accounts support TOTP: Binance, OKX, HashKey — all major crypto platforms support authenticator app 2FA.
- Some HK banking apps SMS-only: Maximise carrier account protection for banks that cannot migrate from SMS OTP due to HKMA requirements.
- Save backup codes securely: Store TOTP backup codes in password manager or printed offline — needed if authenticator device is lost.
- Hardware keys for highest-value accounts: YubiKey for email and crypto accounts provides strongest anti-phishing and anti-SIM-swap protection.