1Physical Security
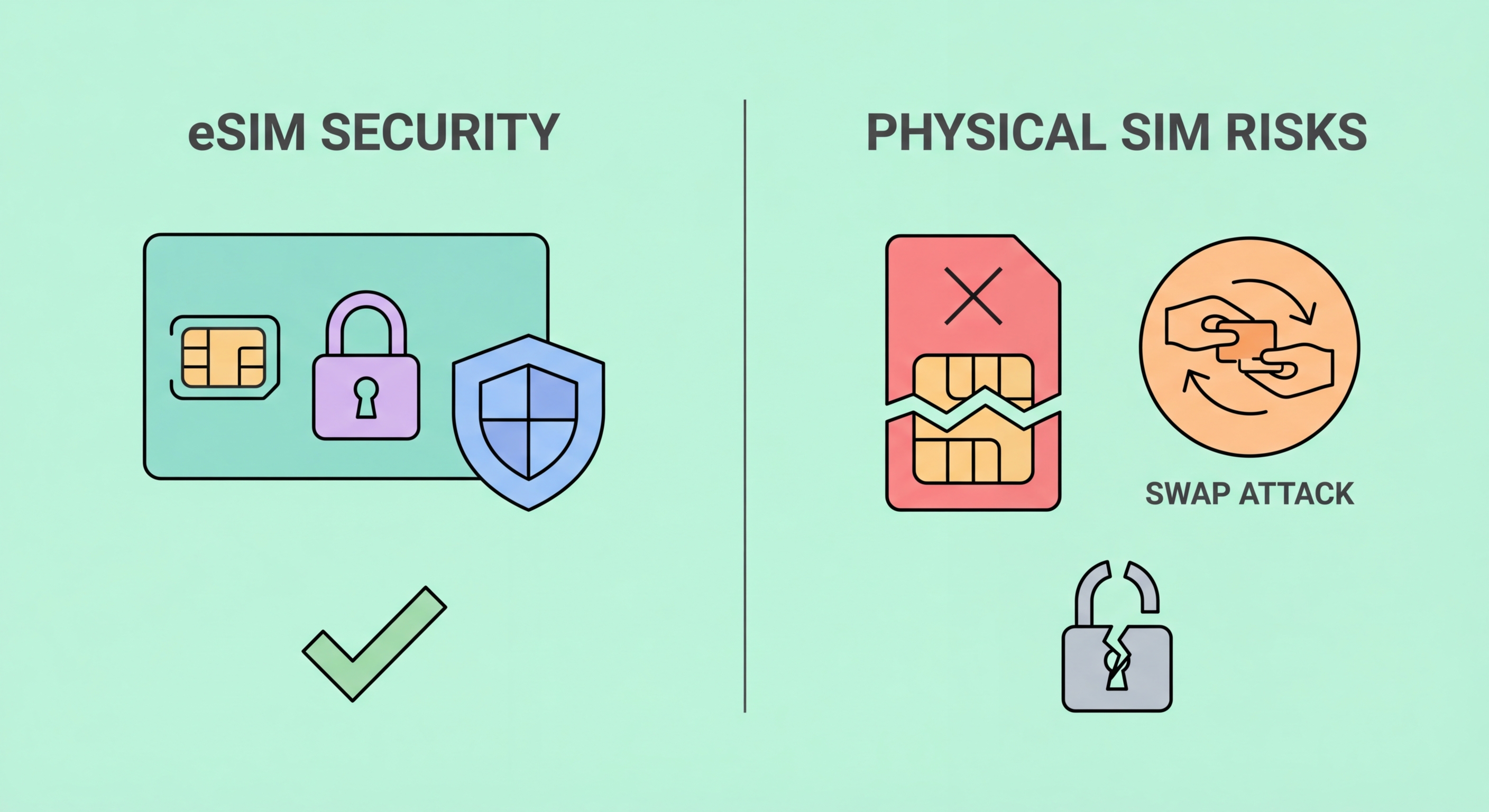
Physical Security: eSIM vs Physical SIM Card
The fundamental physical security difference between eSIM and traditional SIM lies in removability. A physical SIM card can be extracted from a device in seconds — no tools required beyond a SIM ejector pin — and once removed, it can be inserted into any compatible device to operate as your to Spot and Avoid Attacks on Your Phone">Your Phone Number">phone number. This physical portability, while convenient, is simultaneously one of the most significant security vulnerabilities of the physical SIM model. An attacker who gains momentary physical access to your device — in a busy MTR station, at a restaurant while you step away, or through a physical theft — can remove your SIM and use it to receive your calls, SMS messages, and critically, any SMS-based two-factor authentication codes sent to your number.
eSIM credentials are embedded in a secure element that is soldered to the device's motherboard during manufacturing. The secure element is a dedicated, tamper-resistant microchip that stores cryptographic keys and eSIM profiles in an isolated hardware environment that cannot be accessed by the device's main operating system, applications, or any external actor without the appropriate cryptographic credentials. The GSMA SGP.22 specification that governs eSIM architecture requires this secure element isolation — it is not an optional security feature but a mandatory architectural requirement. Even if an attacker physically disassembles the device and removes the secure element chip, the cryptographic keys it contains cannot be extracted without specialist equipment costing hundreds of thousands of dollars.
For Hong Kong users, this physical security distinction is particularly relevant given the density and pace of daily commuting. The MTR network carries over five million passenger trips per day, creating crowded conditions where opportunistic physical theft and pickpocketing occur. A physical SIM theft in this context is a low-sophistication, high-impact attack — the thief has immediate access to your number and all SMS messages sent to it. eSIM eliminates this attack vector entirely: even if your device is stolen, the eSIM profile cannot be extracted and used in another device without breaking through multiple layers of hardware security. The attacker is left with a device they cannot use for number hijacking unless they can also unlock the phone itself.
- Physical SIM can be removed in seconds: No tools beyond a SIM ejector pin — extracted SIM works immediately in any compatible device.
- eSIM is soldered to motherboard: Cannot be physically removed without device disassembly and specialist hardware.
- Secure element architecture: GSMA SGP.22 mandates tamper-resistant hardware storage for eSIM credentials.
- MTR theft relevance: Dense commuting environments create physical SIM theft opportunities that eSIM eliminates.
- No credential extraction: eSIM cryptographic keys cannot be extracted without specialist equipment costing hundreds of thousands of dollars.
- Device PIN as final barrier: Stolen device with eSIM cannot be used for number hijacking without also bypassing device security.